Beyond the technical mechanisms of tracking, a significant portion of our online vulnerability stems from the legal frameworks—or lack thereof—and the underlying business models that drive the internet. We live in a world where data is the new oil, and our personal information is constantly being extracted, refined, and traded. This commercial imperative often clashes directly with our desire for privacy, creating a landscape where our digital footprints are not just observed but actively exploited. Understanding these broader forces is crucial to grasping why Incognito Mode, for all its local utility, offers such a thin veneer of protection against systemic surveillance.
The Shifting Sands of Privacy Laws and Corporate Practices
The regulatory environment surrounding online privacy is a patchwork of differing laws across jurisdictions, often struggling to keep pace with rapid technological advancements. What's considered acceptable data collection in one country might be illegal in another. This global inconsistency creates loopholes and challenges for effective privacy protection. While regions like the European Union have enacted robust legislation like the GDPR (General Data Protection Regulation), giving individuals more control over their data, many other parts of the world, including the United States, have a more fragmented approach. This often leaves consumers at the mercy of corporate policies, which are designed to maximize data collection within the bounds of loosely defined legal limits. The result is a wild west where companies often push the boundaries, knowing that enforcement is slow and penalties might be a mere cost of doing business. This regulatory ambiguity provides fertile ground for persistent tracking, even when users attempt to assert their privacy.
Furthermore, many privacy policies are purposefully vague, written in legalese that few ordinary users bother to read or fully comprehend. By clicking "I agree" to terms of service, we often unknowingly grant companies broad permission to collect and share our data. This implicit consent becomes a powerful tool for data harvesting. The sheer volume and complexity of these agreements make informed consent a practical impossibility for most people. This legal and ethical quagmire means that even when you *think* you're protecting your privacy with tools like Incognito Mode, you might have already consented to broader tracking simply by using a service. It's a subtle but powerful form of manipulation, where the burden of understanding and opting out falls entirely on the individual, rather than on the corporations profiting from their data.
ISPs Know Everything You Do (Unless You Take Specific Action)
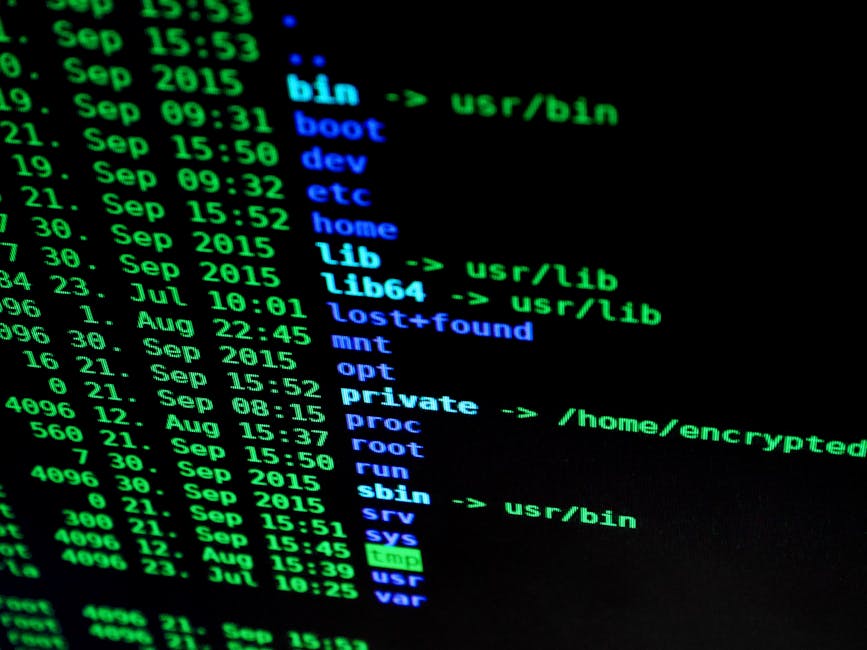
Perhaps one of the most overlooked and significant threats to online privacy comes from your own Internet Service Provider. Your ISP is the gateway to the internet; every packet of data that flows into and out of your home or device passes through their servers. They have a complete, unencrypted record of every website you visit, every service you connect to, and every app you use. This isn't just about IP addresses; they see the full domain names, the timestamps, and the volume of data transferred. Incognito Mode offers absolutely zero protection against your ISP's ability to monitor your traffic. It's like asking your mail carrier to forget what's written on your postcards – they've already read it before delivering.
In the United States, for example, the FCC's broadband privacy rules were controversially rolled back in 2017, effectively allowing ISPs to collect and sell their customers' browsing history and app usage data without explicit consent. While some ISPs claim to anonymize this data, the process of de-anonymization is becoming increasingly sophisticated, making it possible to link seemingly anonymous data back to individual users. This means your private Incognito searches for health information, political views, or sensitive personal topics could theoretically be packaged and sold to advertisers or data brokers by the very company providing your internet access. It's a stark reminder that true online privacy requires more than just browser settings; it demands securing the entire pipeline of your internet connection.
The Dark Side of Free Services You Are the Product
The adage "if you're not paying for the product, you are the product" rings truer than ever in the digital age. Many of the most popular and seemingly indispensable online services—Google Search, Gmail, Facebook, Instagram, YouTube—are offered "for free." However, their immense profitability comes from a different currency: your data. These companies operate on an advertising-driven model, where the more they know about you, the more precisely they can target ads, and thus, the more valuable their advertising space becomes to businesses. Every search query, every email scanned, every video watched, every post liked, every location visited—all contribute to an incredibly rich and granular profile that is meticulously built and constantly updated.
Even when you use these services in an Incognito window, if you log into your account, all your activity within that session is still linked directly to your profile. And even if you don't log in, their extensive network of third-party trackers, embedded across millions of other websites, can still link your activity back to your existing profile through various other identifiers. This data isn't just used for advertising; it's also used to personalize your experience, filter information, and even influence your behavior. The "free" aspect is a powerful incentive, but it comes with a steep privacy cost. The convenience these services offer is often a trade-off for a constant, pervasive level of surveillance that Incognito Mode is simply incapable of mitigating, because the core business model relies on knowing as much about you as possible.
Data Breaches and the Unintended Consequences of Tracking
The sheer volume of personal data being collected and stored by countless entities creates an enormous target for malicious actors. Every company that collects your data—from the websites you visit to the data brokers and advertising networks—becomes a potential point of failure. Data breaches are a depressingly common occurrence, exposing sensitive information ranging from email addresses and passwords to financial details and even health records. The more data that is collected about you, and the more places it is stored, the higher the risk that some piece of that data will eventually fall into the wrong hands. It's a fundamental principle of cybersecurity: you can't lose data you don't collect.
Consider the Equifax breach in 2017, which exposed the personal information of nearly 150 million people, including names, Social Security numbers, birth dates, and addresses. Or the Marriott breach, which affected 500 million guests. These incidents highlight the devastating real-world consequences of excessive data collection. Even if a company has the best intentions and robust security, no system is entirely impenetrable. When your Incognito browsing habits are still being tracked and aggregated by dozens of third parties, each of those entities represents an additional vulnerability. The illusion of privacy provided by Incognito Mode not only fails to stop the initial tracking but also leaves you exposed to the downstream risks of data aggregation and potential breaches, making the stakes for true online privacy incredibly high.