The Password Panacea Thinking a Strong Password Is Your Digital Fortress
For years, the bedrock of online security advice has been the mantra: "Use a strong, unique password." And while this advice is absolutely crucial and remains foundational, the myth that a robust, complex password alone constitutes an impenetrable digital fortress is dangerously outdated. In today's threat landscape, a strong password is no longer a silver bullet; it's merely the first line of defense, and often, it's not enough to withstand the relentless onslaught of modern cyberattacks. Relying solely on a password, no matter how intricate, is like building a magnificent, heavily reinforced front door for your house, but leaving all the windows wide open and a spare key under the doormat. The digital world has evolved, and the methods attackers use to bypass or compromise even the strongest passwords have become incredibly sophisticated, rendering singular password protection increasingly vulnerable.
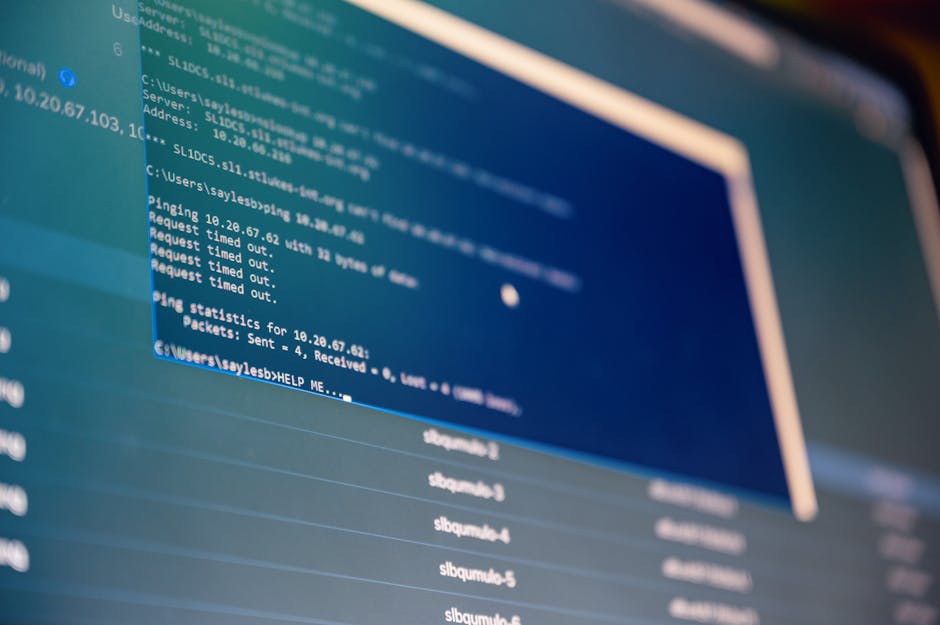
Consider the myriad ways a strong password can be circumvented. Firstly, data breaches are a constant threat. Major companies, often with far more robust security than an individual user, frequently suffer breaches that expose millions of user credentials. When these databases are leaked, attackers can use "credential stuffing" attacks, where they automatically try combinations of stolen usernames and passwords across hundreds of other websites. If you've reused that strong password on multiple sites, a breach on one minor service could compromise your banking, email, or social media accounts. Furthermore, sophisticated brute-force attacks and dictionary attacks, while less effective against truly strong, unique passwords, can still succeed if the password isn't long enough or lacks sufficient entropy. The National Institute of Standards and Technology (NIST) now emphasizes password length over complexity, recommending passphrases of 12-14 characters or more, rather than forcing complex character sets that are hard to remember and often lead to predictable patterns like "Password123!".
Beyond direct password cracking, phishing remains an incredibly effective method for attackers to gain access. Even the most technically savvy individual can fall victim to a well-crafted phishing email or text message that mimics a legitimate service. By tricking you into entering your "strong" password on a fake login page, attackers bypass all your careful password creation efforts. We've seen countless examples, from sophisticated spear-phishing campaigns targeting high-profile individuals to broad attacks aimed at harvesting credentials from millions of ordinary users. Then there are more advanced techniques like "SIM swapping," where attackers trick your mobile carrier into porting your phone number to their SIM card, allowing them to intercept SMS-based multi-factor authentication codes. This highlights the critical need for something more than just a strong password. As a journalist specializing in network security, I've seen firsthand how quickly even the most diligent users can be compromised if they aren't employing layered security measures beyond just their primary password. The fortress needs more than just a strong gate; it needs walls, watchtowers, and vigilant guards.
My Data Isn't Valuable The Dangerous Delusion of Digital Insignificance
Another deeply entrenched and particularly dangerous myth is the belief that "my data isn't valuable to anyone." This sentiment often goes hand-in-hand with the "nothing to hide" fallacy, as individuals assume that because they aren't celebrities, politicians, or high-net-worth individuals, their personal information holds no appeal for hackers or data brokers. This delusion of digital insignificance is profoundly mistaken and actively contributes to a cavalier attitude towards online privacy. In the hyper-connected, data-driven economy of today, *all* data has value, regardless of how mundane or innocuous it may seem in isolation. Your preferences, your habits, your location, your search queries, your purchase history – every single data point is a valuable piece of a much larger puzzle, and aggregators are constantly piecing together these fragments to create incredibly detailed profiles of you, the individual.
The value of your data isn't necessarily in its direct monetary worth (though identity theft is a huge industry); it's in its ability to predict behavior, influence decisions, and facilitate targeted advertising or manipulation. Data brokers, a largely invisible industry, collect, analyze, and sell vast quantities of personal information, often without your explicit knowledge or consent. They compile profiles that can include everything from your income bracket and political leanings to your health conditions and hobbies. This information is then sold to advertisers, political campaigns, insurance companies, and even government agencies. For instance, a seemingly harmless purchase of baby formula online, combined with location data and social media activity, could signal to a data broker that you are a new parent, making you a target for specific product advertisements, but also potentially impacting your insurance rates or loan eligibility based on algorithms that correlate parenthood with certain financial risks. The "data is the new oil" adage isn't just a catchy phrase; it's the operational reality of the internet economy.
Even seemingly insignificant data can be weaponized for identity theft or social engineering. A combination of your birth date (often publicly available on social media), your address (from a public record or old breach), and the name of your first pet (a common security question answer) could be enough for a determined attacker to gain access to accounts or impersonate you. The Cambridge Analytica scandal, where political consulting firm harvested data from millions of Facebook users without their consent to build psychological profiles and influence elections, stands as a stark reminder of how even seemingly innocuous "likes" and connections can be leveraged for mass manipulation. Your data, collectively, is incredibly powerful. It's the fuel that drives the modern surveillance economy, shapes public discourse, and increasingly dictates access to opportunities. To believe your data is worthless is to surrender your digital autonomy and underestimate the sophisticated mechanisms at play, constantly working to extract value from your online existence. Every piece of information about you, no matter how small, contributes to a larger picture that someone, somewhere, is willing to pay for.
Beyond the Myths Reclaiming Your Digital Autonomy with Actionable Steps
Now that we've peeled back the layers of illusion and exposed some of the most pervasive myths surrounding online privacy and security, the natural question arises: what can we actually do? The good news is that while the digital landscape is fraught with challenges, you are not powerless. Reclaiming your digital autonomy requires a proactive, multi-faceted approach, moving beyond simplistic solutions and embracing a mindset of continuous vigilance and education. It’s about building a robust, layered defense, much like securing a physical property with more than just a strong front door. Here are practical, actionable steps you can implement to significantly bolster your online privacy and security, turning knowledge into power.
Fortifying Your Digital Gates with Multi-Factor Authentication
One of the single most impactful steps you can take to protect your online accounts is to enable Multi-Factor Authentication (MFA) or Two-Factor Authentication (2FA) wherever it's offered. This isn't just a recommendation; it's a non-negotiable requirement in today's threat environment. MFA adds an extra layer of security beyond just your password, typically requiring a second form of verification that only you should possess. Even if an attacker manages to get hold of your password through a breach or phishing attack, they still won't be able to access your account without that second factor. Think of it as requiring two keys to open a safe, instead of just one.
To implement MFA, start by auditing your most critical accounts: email, banking, social media, and any services storing sensitive personal information. Look for "Security Settings" or "Privacy Settings" and enable 2FA. There are several common types of MFA, each with varying levels of security:
- Authenticator Apps: These are generally the most secure and recommended option. Apps like Google Authenticator, Authy, or Microsoft Authenticator generate time-sensitive codes on your smartphone. Since these codes are generated locally and don't rely on network communication, they are much harder to intercept.
- Hardware Security Keys: Devices like YubiKey or Google Titan are physical keys that you plug into your computer or tap to your phone. They offer the highest level of security, making phishing and SIM-swapping attacks incredibly difficult.
- SMS Codes: While better than nothing, SMS-based 2FA is susceptible to SIM-swapping attacks. Use it if no other option is available, but prioritize authenticator apps or hardware keys.
- Email Codes: Similar to SMS, these are less secure as email accounts can be compromised. Use only as a last resort.
Make a commitment today to enable MFA on at least your primary email account, as this is often the "master key" for resetting passwords on other services. Then, systematically work your way through your other important accounts. It might add a few seconds to your login process, but the peace of mind and significantly enhanced security are immeasurable.
Mastering the Art of Password Management
The days of trying to remember dozens of complex, unique passwords for every single online service are long gone, and frankly, were never sustainable. The solution lies in embracing a robust password manager. These tools act as encrypted vaults for all your login credentials, allowing you to use incredibly long, complex, and unique passwords for every single account without having to memorize them. You only need to remember one strong master password to unlock the vault, which should be truly unique and not used anywhere else.
Popular and reputable password managers include LastPass, 1Password, Bitwarden, and Dashlane. They often offer features like:
- Secure Password Generation: Automatically create strong, random passwords that meet complexity requirements.
- Auto-fill Capabilities: Conveniently fill in usernames and passwords on websites and apps, reducing the risk of phishing by only filling on legitimate sites.
- Password Audits: Identify weak, reused, or compromised passwords in your vault.
- Secure Notes and File Storage: Store other sensitive information like credit card numbers or secure documents.
Transitioning to a password manager might seem daunting initially, but the long-term benefits in terms of security and convenience are substantial. Start by choosing a reputable manager, then systematically migrate your existing logins. As you create new accounts, let the password manager generate and store the credentials. This simple step eliminates the common pitfalls of password reuse and weak passwords, dramatically reducing your attack surface.
Understanding and Reducing Your Digital Footprint
Your digital footprint is the trail of data you leave behind as you navigate the internet. Every website you visit, every social media post, every online purchase, every app you download – it all contributes to this ever-growing dossier. To reclaim privacy, you need to understand what information is out there and actively work to reduce it.
- Audit Your Social Media: Review the privacy settings on all your social media accounts (Facebook, Instagram, X/Twitter, LinkedIn, etc.). Limit who can see your posts, photos, and personal information. Remove old, embarrassing, or sensitive content. Be mindful of what you share; once it's online, it's very difficult to erase completely.
- Delete Unused Accounts: If you signed up for a service years ago and no longer use it, delete the account. Data associated with inactive accounts can still be compromised in breaches. Many websites have a "delete account" option, though sometimes it's buried in settings.
- Control Location Data: Review privacy settings on your smartphone. Limit which apps have access to your location services, and consider turning off location history for Google Maps or Apple Maps if you don't need it.
- Use Privacy-Focused Browsers and Extensions: Consider browsers like Brave or Firefox with enhanced tracking protection. Install browser extensions like uBlock Origin (for ad and tracker blocking) or Privacy Badger (to block invisible trackers).
- Think Before You Click: Be skeptical of unfamiliar links, especially in emails or social media. Phishing attempts are often designed to trick you into revealing information or downloading malware.
Regularly searching for your own name on Google and other search engines can also provide insights into what information about you is publicly available. You might be surprised by what you find.
Building a Layered Security Approach Beyond Antivirus
As we discussed, antivirus software is a necessary but insufficient defense. A truly robust security posture requires a layered approach. Think of it like a castle with multiple defenses, not just one wall.
- Firewall: Ensure your operating system's firewall (Windows Defender Firewall, macOS Firewall) is enabled and configured correctly. It controls incoming and outgoing network traffic, blocking unauthorized access to your computer.
- Virtual Private Network (VPN): This is where my expertise truly comes into play. A reputable VPN encrypts your internet connection, routing your traffic through a secure server. This hides your IP address, making it much harder for ISPs, websites, and snoopers to track your online activities. It's especially crucial when using public Wi-Fi networks, which are often unsecured and ripe for data interception. Choose a VPN provider with a strict no-logs policy and strong encryption protocols.
- Regular Software Updates: Always keep your operating system, web browsers, and all installed applications updated. Software updates frequently include security patches that fix newly discovered vulnerabilities that attackers could exploit. Enable automatic updates wherever possible.
- Ad Blockers and Tracker Blockers: Tools like uBlock Origin or Privacy Badger not only improve your browsing experience by removing annoying ads but also block many of the trackers that collect data on your online behavior, enhancing your privacy.
- Disk Encryption: For sensitive data on your computer, consider enabling full disk encryption (BitLocker for Windows, FileVault for macOS). This ensures that if your device is lost or stolen, your data remains inaccessible without the correct password.
No single tool offers complete protection, but by combining these elements, you create a formidable defense that significantly reduces your risk of compromise and enhances your privacy.
Cultivating a Mindset of Continuous Education and Healthy Skepticism
Perhaps the most vital tool in your online privacy arsenal isn't a piece of software or a specific setting, but your own informed judgment. The digital landscape is constantly evolving, with new threats and technologies emerging regularly. Therefore, continuous education and a healthy dose of skepticism are paramount. Don't blindly trust every link, every email, or every pop-up. Question the permissions apps request, scrutinize the privacy policies of services you use, and stay informed about the latest cybersecurity news and best practices.
Engage with reputable cybersecurity blogs, follow experts on social media, and read up on data privacy regulations. Understand that convenience often comes at the cost of privacy, and make conscious choices about the trade-offs you are willing to make. The battle for online privacy is ongoing, and while it might seem overwhelming at times, every step you take to understand the threats and implement stronger defenses contributes to a safer, more private digital experience for yourself and, by extension, for everyone. Your active participation and informed decisions are the ultimate antidote to the myths that have held us captive for too long.