Beyond Your Browser The Unseen Eyes Tracking Your Every Move
The misconception that Incognito Mode offers a cloak of invisibility is a dangerous one, often leading users to engage in activities they believe are private, only to find their data exposed or their activities traceable. It's not just about your browser's local cache; it's about the entire ecosystem of the internet, a sprawling network where countless entities have a vested interest in collecting, analyzing, and monetizing your digital behavior. From the moment you connect to the internet, a complex web of data collection begins, orchestrated by players far more powerful and pervasive than the simple cookies your Incognito window might discard. Understanding these unseen eyes, their motivations, and their methods is the crucial first step in truly reclaiming your online privacy. This isn't a dystopian fantasy; it's the operational reality of the modern web, and ignoring it is akin to walking through a crowded street shouting your personal details.
For over a decade, I’ve delved into the mechanics of how these digital watchers operate, and it’s a constant arms race between privacy advocates and data harvesters. The tools and techniques employed are constantly evolving, becoming more sophisticated and harder to detect. It's a landscape where your personal preferences, your political leanings, your health concerns, and even your financial stability can be inferred from your browsing habits, all without your explicit consent or even your awareness. The sheer volume of data being collected is staggering, and its aggregation creates incredibly detailed profiles that can be used for targeted advertising, credit scoring, insurance risk assessment, and even political manipulation. This isn't just about ads following you around the internet; it's about the construction of a persistent digital identity that, once formed, is incredibly difficult to dismantle or escape, regardless of how many "private" windows you open.
Your Internet Service Provider Knows More Than You Think
Let's start with the most fundamental layer of internet access: your Internet Service Provider (ISP). Whether you're connecting via fiber, cable, or mobile data, your ISP is the gatekeeper to the internet. Every single byte of data you send or receive passes through their servers. And yes, they log it. This isn't a conspiracy theory; it's a standard operational practice, often mandated by law in many countries for data retention purposes. Your ISP knows your IP address, the precise timestamp of your connection, the duration of your sessions, and crucially, every website you visit. They can see the domain names of every server you connect to, even if the content of your communication is encrypted (HTTPS). Think about it: they are the literal pipeline for all your online traffic, and they have complete visibility into the metadata of your connections. This means that while Incognito Mode might prevent your browser from remembering you visited a particular site, your ISP has a permanent record of that exact interaction.
This reality has profound implications. In the United States, for example, Congress voted in 2017 to repeal broadband privacy rules, effectively allowing ISPs to collect and sell your browsing history and other personal data without your explicit consent. This legislative action cemented the commercial viability of your browsing data for ISPs, turning your online activities into a valuable commodity. Imagine a detailed dossier of your online life, including your health searches, political affiliations, financial inquiries, and even personal interests, all compiled and potentially sold to advertisers, data brokers, or other third parties. This data is not anonymized in the way many users hope; it's directly linked to your account, your home address, and your identity. So, while you might think you're discreetly researching a sensitive topic in Incognito, your ISP is quietly adding that information to your ever-growing digital profile, ready to be exploited.
The Relentless Pursuit of Ad Trackers and Website Profilers
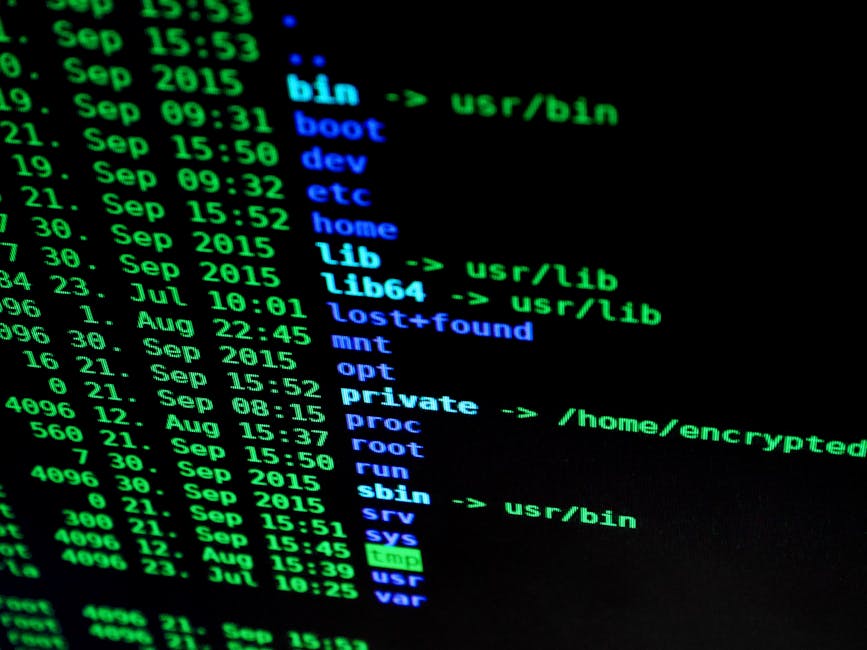
Beyond your ISP, the internet is teeming with a vast, invisible network of ad trackers, analytics scripts, and data brokers whose sole purpose is to monitor your behavior across websites. These aren't just limited to major tech giants; thousands of companies participate in this ecosystem. When you visit a website, it’s rarely just a direct connection between your browser and that site's server. Instead, your browser loads dozens, sometimes hundreds, of third-party scripts from advertising networks, social media platforms, analytics providers, and content delivery networks. Each of these scripts is a potential tracker, dropping cookies, collecting data points, and building a profile of your interests, demographics, and online habits. Incognito Mode, unfortunately, does little to deter these pervasive trackers. While it clears *first-party* cookies (those set by the website you directly visit) upon closing the window, many third-party trackers are designed to be more persistent or to use alternative tracking methods.
Consider the insidious nature of "supercookies" or evercookies, which are incredibly difficult to delete and can re-create themselves even after you attempt to clear your browser data. These aren't typically cleared by Incognito Mode and can persist across sessions, providing a long-term identifier for trackers. Furthermore, many trackers don't even rely solely on cookies anymore. Techniques like pixel tracking, referrer headers, and even the unique configuration of your browser (known as browser fingerprinting, which we'll delve into deeper) allow them to identify and track you with remarkable accuracy, regardless of whether you're in a "private" browsing session. The goal of these trackers is to create a comprehensive, actionable profile of every internet user, enabling highly targeted advertising that is eerily precise. This constant surveillance transforms every click, every scroll, and every page view into a data point, contributing to a digital identity that is bought, sold, and traded in an opaque market, far beyond the reach of your browser's Incognito settings.
Workplace Surveillance and School Network Monitoring
The illusion of Incognito Mode's privacy becomes particularly stark and potentially problematic in environments like workplaces or educational institutions. Many organizations employ network monitoring software, firewalls, and content filters to manage network usage, enforce policies, and ensure security. These systems operate at the network level, meaning they monitor all internet traffic flowing through the organization's network, irrespective of the browser or browsing mode used on individual devices. If you're using a company-issued laptop or connecting to the office Wi-Fi, your employer can absolutely see every website you visit, every search query you make, and potentially even the content of your communications, especially if the traffic isn't encrypted (HTTP instead of HTTPS). Even with HTTPS, they can often see the domain names you're visiting, just like your ISP can. I've personally advised numerous companies on implementing such systems, and the data they collect is extensive and detailed.
The same principle applies to school networks. Educational institutions often have even stricter monitoring policies in place, not just for security but also for safeguarding minors and preventing access to inappropriate content. A student using Incognito Mode on a school computer or network might believe they're circumventing these filters or hiding their activities, but in reality, they're merely hiding it from the local browser history. The network administrator, with the right tools, has a clear view of their online activities. This isn't about judging the ethics of such monitoring, but rather about dispelling the myth that Incognito Mode provides any meaningful barrier against it. In these controlled network environments, the notion of private browsing is largely a fantasy, and relying on it can lead to disciplinary actions or, in more severe cases, legal repercussions, demonstrating a profound disconnect between user perception and technical reality.