The digital world we navigate is far more complex and interconnected than most casual users realize, a sprawling network where data flows ceaselessly, often without our explicit consent or even our awareness. When you open that Incognito window, you might feel like you've slipped into the shadows, but in reality, you've merely adjusted the curtains on your own personal stage, while the audience and the backstage crew continue to observe your performance with unwavering attention. The entities collecting information about your online activities extend far beyond the parameters of your browser's local memory, forming a vast web of surveillance that operates on multiple layers, each with its own motivations and methods. To truly understand why Incognito Mode offers such a limited shield, we need to dissect these layers, revealing the myriad of unseen watchers who meticulously record and analyze our every digital move, transforming our online presence into a rich tapestry of data points that are then bought, sold, and leveraged in ways that can feel both invasive and unsettling. This intricate ecosystem of data collection is the true adversary of online privacy, an adversary that a simple browser setting is woefully unprepared to combat, highlighting the urgent need for a more comprehensive approach to personal data protection.
Your Internet Service Provider Always Has a Front-Row Seat
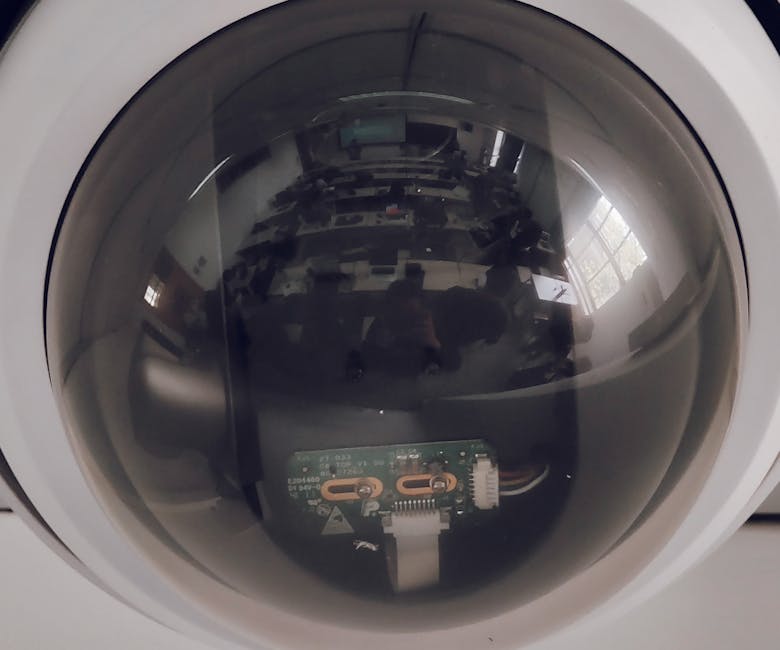
Imagine your internet service provider (ISP) as the gatekeeper to the entire internet, a powerful entity through which all your online traffic must pass. Every single packet of data, every request for a webpage, every streaming video, every email you send or receive – it all flows through your ISP's servers. This fundamental architectural reality means that no matter what browser settings you employ, including Incognito Mode, your ISP possesses an unparalleled view of your online activities. They can see which websites you visit, when you visit them, how long you stay, and even the type of content you're accessing, even if they can't always decipher the exact content of an encrypted page. This isn't theoretical; it's a core function of how the internet works, and it grants ISPs a unique and incredibly powerful vantage point into the digital lives of their subscribers, making them one of the most significant and often overlooked players in the data collection game.
This visibility extends to a vast array of metadata, which, when aggregated, can paint an incredibly detailed picture of your online behavior. Your ISP logs your IP address, which is essentially your unique identifier on the internet, allowing them to link all your online activity directly back to your account and, by extension, to you personally. They record the destination IP addresses of the websites you visit, the domain names you resolve through their DNS servers, the amount of data you upload and download, and the times of your online sessions. While the content of an HTTPS-encrypted website is technically obscured from your ISP, the fact that you visited "netflix.com" or "facebook.com" or a specific news site is not. This seemingly innocuous metadata, when combined with other data points, can reveal highly personal information about your habits, interests, political leanings, health concerns, and even your relationships. It's like a postal service knowing every address you send mail to and receive mail from, even if they can't read the letters themselves; the pattern of communication alone can be incredibly revealing and is often more than enough for profiling purposes.
The situation is further complicated by varying data retention laws across different countries, or in many cases, the complete absence of such laws. In some regions, ISPs are legally mandated to store customer browsing data for extended periods, sometimes for years, for potential access by law enforcement or government agencies. In other places, while not legally required, ISPs may choose to collect and retain this data for their own business purposes, such as creating aggregated user profiles to sell to advertisers or using it to inform their own marketing strategies. The controversial repeal of internet privacy rules in the United States in 2017, for instance, explicitly allowed ISPs to sell customer browsing data to third parties without requiring customer consent, highlighting the significant commercial value placed on this information. This legislative landscape, coupled with the inherent technical capabilities of ISPs, means that your "private" browsing session is anything but private from the entity that literally connects you to the world wide web, underscoring a critical vulnerability in the perceived anonymity of Incognito Mode.
Websites and Their Persistent Trackers Never Forget a Face
Even if your ISP weren't watching, the websites you visit themselves are armed with an arsenal of tracking technologies designed to identify, monitor, and profile you, irrespective of your browser's Incognito setting. The moment you land on a webpage, a complex dance of data collection begins, orchestrated by the site itself and often by numerous third-party entities embedded within it. The most commonly known culprits are cookies, those small text files stored on your computer by websites. While Incognito Mode typically clears *first-party* cookies (those set by the site you're directly visiting) at the end of a session, preventing you from being automatically logged in or seeing personalized content on a subsequent visit, it does not stop new ones from being set during your current "private" session. More importantly, it does little to mitigate the pervasive threat of *third-party* cookies and other, more sophisticated tracking mechanisms.
Third-party cookies, often placed by advertising networks, analytics providers, or social media widgets embedded on a site, are designed to track your movements across multiple websites. These cookies build a comprehensive profile of your browsing habits, interests, and demographics, following you from one site to another, creating a persistent digital shadow. Even if your Incognito session deletes these cookies upon closing, the trackers have already done their job, recording your visit and associating it with your IP address or other persistent identifiers. When you open a regular browser session later, or even another Incognito session, these networks can often re-identify you through other means, linking your new activity back to your existing profile. This is why you might search for a product in an Incognito window, only to see ads for that exact product appearing in your regular browser session or on social media days later; the advertising network has connected the dots, sidestepping your browser's local privacy settings with remarkable ease and efficiency, demonstrating the limitations of a client-side approach to a network-wide problem.
Beyond traditional cookies, the tracking landscape has evolved to include much more insidious methods, collectively known as "browser fingerprinting." This technique involves collecting a unique set of characteristics from your browser and device to create a distinctive "fingerprint" that can identify you with a high degree of accuracy, even without traditional cookies. This fingerprint can be composed of dozens of data points: your browser type and version, operating system, installed fonts, screen resolution, time zone, language settings, plugins, hardware details (like GPU and CPU), and even subtle variations in how your browser renders graphics (Canvas fingerprinting). Researchers have shown that these fingerprints can be unique enough to identify a significant percentage of users across different websites, making it a powerful tool for persistent tracking. Incognito Mode does nothing to alter these system-level characteristics, meaning your unique browser fingerprint remains consistent whether you're in a regular or "private" session, allowing sophisticated trackers to recognize you as the same user across multiple visits and build a continuous profile of your online behavior, rendering the concept of a "fresh start" utterly meaningless in the face of such advanced surveillance technologies.
Furthermore, websites employ a variety of other stealthy tracking technologies, such as pixel trackers (tiny, invisible images embedded on a page that load from a tracking server), web beacons, and sophisticated JavaScript tracking scripts (like those from Google Analytics, Adobe Analytics, or Facebook Pixel). These scripts execute directly in your browser, sending data about your interactions – clicks, scrolls, time spent on page, mouse movements – directly to third-party servers. They don't rely on storing data on your local machine in the same way cookies do; instead, they transmit data in real-time. Even if Incognito Mode prevents the *storage* of certain session data, it does not prevent the *transmission* of this real-time interaction data to external servers. These trackers are often deeply integrated into website functionality, making them difficult to block without disrupting the site itself. They represent a fundamental challenge to online privacy, as they operate largely outside the scope of what a simple "private browsing" mode can hope to control, continuously feeding the voracious appetite of data brokers and advertising networks with granular details about your online journey, regardless of your perceived anonymity.