The sobering reality that our digital lives are constantly under threat, potentially for sale on the dark web, shouldn't lead to despair or digital paralysis. Instead, it must serve as a powerful catalyst for action, a wake-up call to fortify our personal digital fortresses. While no defense is absolutely impenetrable, and the threat landscape is ever-evolving, adopting a proactive, multi-layered approach can significantly reduce your risk and make you a far less attractive target for cybercriminals. Think of it not as a one-time fix, but as an ongoing commitment to digital hygiene, much like maintaining your physical health. Small, consistent efforts can yield substantial protective benefits, transforming you from a potential victim into a resilient digital citizen.
The journey to reclaim your digital autonomy begins with understanding that you have agency in this fight. It’s about moving beyond passive acceptance of the risks and actively engaging with the tools and strategies available to protect yourself. We often hear advice about strong passwords, but the true defense involves a deeper understanding of how data is collected, how it's exploited, and how you can disrupt those processes. It means becoming a more informed participant in your own digital life, questioning default settings, scrutinizing requests for information, and leveraging privacy-enhancing technologies. This isn't about becoming a cybersecurity expert overnight; it's about building a foundation of practical habits that collectively create a formidable barrier against those who seek to profit from your personal information.
Fortifying Your Digital Borders A Multi-Layered Approach
Securing your digital life requires more than just one silver bullet; it demands a strategic combination of tools and practices that work in concert to protect your information. One of the most fundamental steps is to conduct a thorough personal data audit. Start by identifying all online accounts you possess, especially those containing sensitive information like banking, email, social media, and healthcare portals. For each account, ensure you are using a unique, complex password, ideally generated and stored by a reputable password manager. Seriously, stop reusing passwords; a single breach can then compromise your entire digital ecosystem. Enable two-factor authentication (2FA) or multi-factor authentication (MFA) on every single account that offers it. This simple step adds a crucial layer of security, making it exponentially harder for an attacker to gain access even if they manage to steal your password.
Next, consider your devices themselves, which are often the primary entry points for data exfiltration. Keep all your operating systems, applications, and web browsers updated to their latest versions. Software updates often contain critical security patches that close vulnerabilities exploited by cybercriminals. Install a reputable antivirus and anti-malware solution on all your computers and mobile devices, and ensure it's configured for real-time protection and regular scans. Be incredibly cautious about what you download and from where; stick to official app stores and trusted websites. Furthermore, encrypt your devices if you haven't already; most modern operating systems offer built-in encryption, which protects your data if your device is lost or stolen, making it inaccessible to unauthorized parties.
Finally, embrace privacy-enhancing tools as part of your daily routine. A Virtual Private Network (VPN) is no longer a niche tool for tech enthusiasts; it's a fundamental privacy shield. A good VPN encrypts your internet traffic and masks your IP address, making it much harder for third parties (including your ISP, advertisers, and potential attackers) to track your online activities and collect data about your browsing habits. While a VPN isn't a silver bullet against all threats, it significantly enhances your anonymity and secures your connection, especially when using public Wi-Fi. Also, consider using privacy-focused browsers or browser extensions that block trackers and intrusive ads, further limiting the data points that companies can collect about you for their own profiling purposes. These tools, when used consistently, build a robust digital perimeter around your online presence.
The Power of Prudence Simple Habits for Stronger Security
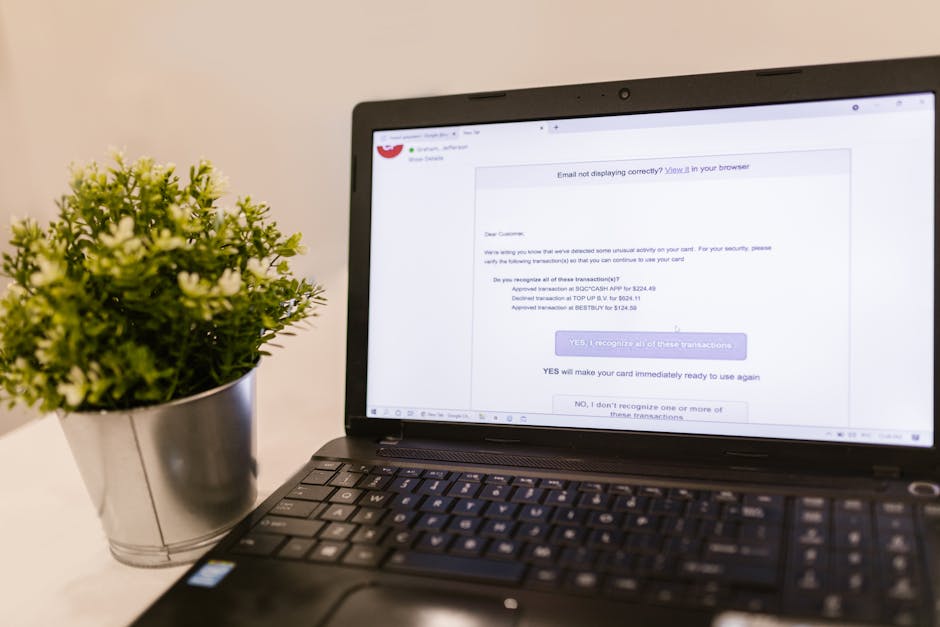
While technical solutions are vital, many successful cyberattacks exploit human behavior rather than technological flaws. Cultivating a habit of digital prudence can be your strongest defense. The first crucial habit is to be perpetually skeptical of unsolicited communications. Whether it's an email, a text message, a phone call, or even a social media direct message, always question the sender's legitimacy. Never click on suspicious links or download attachments from unknown sources. If an email seems to come from a legitimate entity like your bank or a service provider, instead of clicking the link in the email, open your browser and navigate directly to their official website to log in or verify the information. This simple verification step can thwart the vast majority of phishing attempts that rely on immediate, unthinking clicks.
Another powerful habit is to be mindful of what you share online, both intentionally and unintentionally. Every piece of information you post on social media, every survey you fill out, and every app you grant permissions to, contributes to your digital footprint. Before sharing, ask yourself: "Could this information be used against me?" Think twice about revealing your birthday, your pet's name, your mother's maiden name, or even your current location, as these details are frequently used as security questions or for social engineering. Regularly review the privacy settings on your social media accounts and other online services, ensuring they are set to the strictest levels you're comfortable with. Many platforms default to sharing more information than you might realize, so a periodic check can prevent unintended data exposure.
Finally, develop a routine for monitoring your digital identity. Regularly check your bank and credit card statements for any suspicious activity. Consider signing up for a credit monitoring service that alerts you to new accounts opened in your name or significant changes to your credit report. Many identity theft protection services also offer dark web monitoring, which scans illicit marketplaces for your personal information and alerts you if it's found. While these services don't prevent your data from being stolen, they provide early warning, allowing you to react quickly and mitigate potential damage. Being proactive in monitoring your digital presence ensures that you're not caught off guard and can take swift action if your information surfaces on the dark web.
Building a Resilient Digital Persona Your Ongoing Commitment
Understanding that the threat of your digital life being for sale is a continuous challenge, not a one-time battle, is perhaps the most important realization. Building a resilient digital persona is an ongoing commitment that requires periodic review and adaptation. Technology evolves, and so do the methods of cybercriminals. What was considered secure five years ago might be vulnerable today. Therefore, staying informed about the latest cybersecurity threats and best practices is crucial. Follow reputable cybersecurity blogs, news outlets, and expert advice to keep your knowledge current. This doesn't mean becoming an alarmist, but rather an informed participant in your own digital defense, adapting your strategies as the landscape shifts.
Part of this ongoing commitment involves regularly reviewing your digital footprint. Perform occasional searches for your own name online to see what information is publicly available about you. If you find outdated or incorrect information, or data you'd rather not be public, take steps to have it removed where possible. This might involve contacting website administrators or leveraging data removal services. Remember that data brokers collect and sell vast amounts of personal information, and while removing all of it is challenging, reducing your public exposure can help. It's a bit like spring cleaning for your digital self, ensuring that your online presence reflects what you want the world to see, and minimizes what others can exploit.
Ultimately, the goal is to cultivate a mindset of proactive digital self-preservation. It's about empowering yourself with knowledge and tools, making informed decisions about your online interactions, and understanding that your digital life is a valuable asset worth protecting. By embracing strong authentication, smart browsing habits, privacy-enhancing technologies, and continuous vigilance, you can significantly reduce the chances of your personal information becoming another commodity on the dark web. It’s a collective effort, too; by setting a good example and educating those around you, we can collectively raise the bar for digital security and make the internet a safer place for everyone, transforming the narrative from one of inevitable victimhood to one of empowered resilience.