Crafting Your Ideal Digital Environment Harnessing Browser Profiles and Containers
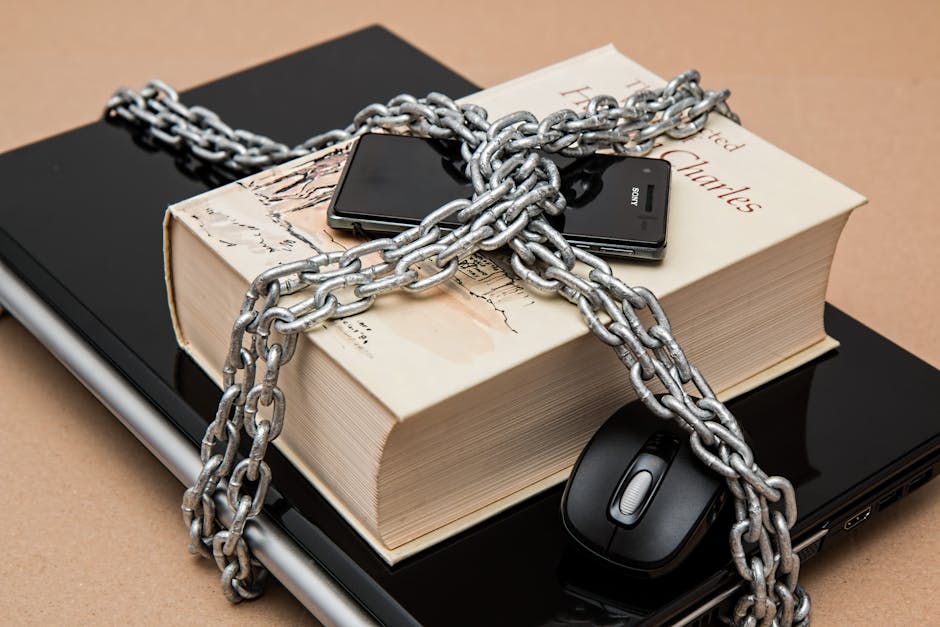
For most of us, our browser is a chaotic melange of work tabs, personal social media feeds, online shopping carts, and various research projects, all jumbled together in a single, undifferentiated space. This constant intermingling of contexts not only creates mental clutter and makes it incredibly difficult to focus on a single task but also presents significant security and privacy risks. Imagine trying to manage multiple distinct projects on a single physical desk, with documents from each project scattered haphazardly, client files mixed with personal letters, and sensitive financial statements lying next to your grocery list; that's precisely the digital disarray many professionals contend with daily within their browser. The concept of browser profiles and, more specifically, "container tabs" (a feature popularized by Firefox), offers a revolutionary solution to this problem, allowing you to segment your online life into distinct, isolated environments, each with its own set of cookies, login sessions, and even browsing history. This strategic compartmentalization not only dramatically improves focus and productivity but also adds a crucial layer of security by isolating sensitive activities and preventing cross-site tracking, fundamentally transforming your browser into a highly organized, multi-faceted digital workspace.
Browser profiles, available in Chrome, Edge, and Firefox, allow you to create entirely separate browser instances, each with its own bookmarks, extensions, themes, and crucially, its own set of login credentials and cookies. This means you can have one profile dedicated solely to work, logged into your corporate accounts and cloud services, another for personal browsing and social media, and perhaps a third for sensitive financial transactions, ensuring that your work activities remain completely separate from your personal life. This separation prevents accidental data leakage, eliminates the constant login/logout dance when switching between accounts (e.g., managing multiple Google accounts for different clients), and creates a clean, focused environment for each context. Even more powerful are Firefox's Container Tabs, which take this concept to a granular level, allowing you to open individual tabs within designated "containers" (e.g., Work, Personal, Banking, Shopping). Each container behaves like a completely separate browser instance, preventing websites in one container from seeing cookies or login sessions in another, effectively isolating your activities and significantly enhancing privacy by thwarting cross-site tracking and cookie-based fingerprinting. This level of digital hygiene is not just a convenience; it's a strategic advantage in managing the complexities of modern online life.
Segregating Your Online Life A Strategy for Focus and Security
The benefits of segregating your online life through browser profiles and container tabs extend far beyond mere organization; they form a cornerstone of a robust cybersecurity strategy and a powerful tool for cognitive load management. From a security standpoint, isolating sensitive activities like online banking or managing cryptocurrency in a dedicated, clean profile or container drastically reduces the risk of credential theft or session hijacking, as malicious scripts or compromised websites in other tabs cannot access those isolated sessions. Should one container become compromised, the damage is contained to that specific environment, preventing the breach from spreading to your other, more sensitive digital spaces. This compartmentalization acts as a digital airlock, ensuring that the vulnerabilities of one online activity do not expose the integrity of another, providing a peace of mind that is invaluable in today's threat landscape. It's a proactive defense mechanism that doesn't rely on detecting threats after they've already entered your system but rather on preventing them from ever reaching your critical data in the first place.
From a productivity perspective, the ability to maintain distinct digital workspaces is nothing short of revolutionary. Imagine switching from a deep-dive research project to a quick check of personal email without inadvertently being distracted by a social media notification or seeing an ad for something you browsed an hour ago for leisure. With profiles and containers, your "work" browser can be lean and mean, loaded only with essential extensions, logged into only work-related accounts, and free from the clutter of personal distractions. Your "personal" browser, conversely, can be set up with all your favorite social media logins and entertainment bookmarks, without them spilling over into your professional sphere. This clear delineation not only minimizes context-switching costs, allowing your brain to stay focused on the task at hand, but also provides a psychological boundary, helping you maintain a healthier work-life balance by literally closing down your "work" browser when your workday is done. This strategy moves beyond simply managing tabs to managing entire digital identities, offering a level of control and clarity that transforms the often-overwhelming experience of online multitasking into a streamlined, intentional process.
"Compartmentalization in the digital realm is as vital as it is in physical security. Browser profiles and containers are the firewalls for your digital identities." - Kevin Mitnick, World-renowned Hacker and Security Consultant.
Reclaiming Control Over Your Digital Footprint Managing Advanced Site Permissions
Every time you visit a website, your browser acts as an intermediary, fielding requests from that site for access to various parts of your computer and personal data, ranging from your geographical location and camera to your microphone, notifications, and even your clipboard. While some of these requests are legitimate and necessary for a site's functionality (e.g., a video conferencing tool needing camera access), many are either superfluous, overly broad, or outright intrusive, posing significant privacy risks if granted indiscriminately. The default browser behavior is often to prompt you with a modal dialog box, asking for a simple "Allow" or "Block," and in our haste to access content, we frequently click "Allow" without fully considering the long-term implications of granting persistent access to our most sensitive hardware and data. This seemingly innocuous act can lead to a gradual erosion of privacy, where numerous websites gain perpetual access to your location data, listen in through your microphone, or send you incessant, distracting notifications, all without your conscious awareness or ongoing consent. Truly mastering your browser involves moving beyond these initial prompts to proactively manage and revoke these permissions, ensuring that only trusted sites have access to what they truly need, precisely when they need it.
Modern browsers provide a centralized hub for managing these advanced site permissions, allowing you to review and revoke access on a site-by-site basis, often buried within the site information panel (usually accessible by clicking the padlock icon in the address bar) or within the browser's main settings menu. This isn't just about blocking notifications; it extends to crucial controls over camera and microphone access, location sharing, autoplay media, pop-up windows, and even more subtle permissions like clipboard access or the ability to send push notifications. For example, you might have granted a news site permission to send notifications months ago, only to find yourself bombarded with irrelevant alerts throughout your workday. By navigating to the site's permissions, you can revoke this access permanently, restoring your peace and focus. Similarly, if you used a video conferencing tool once and granted it camera and microphone access, it might retain that permission indefinitely; a quick check allows you to disable it until your next meeting, ensuring your privacy is maintained when those devices are not actively in use. This granular control transforms a passive acceptance of site requests into an active, informed decision-making process, putting you firmly back in the driver's seat of your digital interactions.
The Perils of Unchecked Access Understanding Browser Permission Risks
The dangers of granting unchecked access to browser permissions are multifaceted, spanning privacy breaches, security vulnerabilities, and a general degradation of user experience. From a privacy perspective, constantly sharing your location data with multiple websites can build a detailed map of your physical movements, which can be easily aggregated and sold to third parties, often without your explicit knowledge or consent. Similarly, granting microphone or camera access to untrustworthy sites opens the door to potential eavesdropping or unauthorized recording, a chilling prospect that underscores the importance of stringent permission management. Even seemingly innocuous permissions like clipboard access can be exploited by malicious sites to steal sensitive information you might have copied, such as passwords or financial data, highlighting the subtle but significant risks associated with an overly permissive browser environment. The cumulative effect of these small, seemingly insignificant permissions can create a surprisingly detailed and vulnerable digital footprint, making you an easier target for targeted advertising, phishing scams, or even more sophisticated forms of cyberattack.
Beyond privacy, the unmanaged proliferation of site permissions can also impact browser performance and user experience. Websites constantly sending notifications, for instance, can be a significant source of distraction, breaking your concentration and forcing you to context-switch away from important tasks, thereby torpedoing productivity. Auto-playing videos, another common permission request, can consume bandwidth, drain battery life, and create an irritating browsing experience, especially on mobile devices or slower connections. A cluttered permission landscape also means that your browser is constantly performing background checks and maintaining connections for sites that you rarely visit, consuming valuable system resources unnecessarily. By regularly reviewing and revoking permissions, you not only tighten your privacy and security posture but also streamline your browser's operation, reducing unnecessary background processes and creating a cleaner, more responsive environment. This proactive approach ensures that your browser remains a tool that empowers you, rather than one that subtly undermines your privacy, security, and focus, ultimately leading to a more intentional and less anxiety-inducing online experience.