In an increasingly interconnected yet fractured world, where digital borders are policed with ever-greater scrutiny and personal data has become the new oil, the imperative for enhanced anonymity has never been more pressing. The notion that a basic VPN suffices for everyone is a dangerous oversimplification, especially for individuals whose safety, livelihood, or even freedom hinges on their ability to operate without being traced. From journalists risking their lives to expose corruption in authoritarian states to human rights activists organizing protests, and even whistleblowers bringing corporate malfeasance to light, these individuals exist in a high-stakes environment where every digital footprint is a potential vulnerability. For them, Multi-Hop VPN isn't just an optional extra; it's a critical tool in their digital survival kit, a robust layer of protection against the formidable forces arrayed against them.
Consider the harrowing case of a journalist working undercover in a country known for its aggressive surveillance tactics. Every email, every encrypted chat, every article draft transmitted could be intercepted, analyzed, and traced back to them. A single VPN might offer some protection against their ISP or local network monitoring, but a determined state actor with sophisticated deep packet inspection capabilities and access to internet backbone infrastructure could potentially monitor traffic going into and out of the VPN server. If that single server is identified, or if the government pressures the VPN provider, the journalist's connection could be compromised. However, with a Multi-Hop VPN, their traffic first travels to a server in a neutral country, then to another server in a different, perhaps more privacy-friendly, jurisdiction, before finally reaching its destination. This complex routing path makes it exponentially harder for the hostile government to connect the dots, offering a crucial buffer zone that could mean the difference between freedom and incarceration, or worse. It's not just about hiding; it's about becoming a moving target across multiple jurisdictions, making interception a logistical nightmare.
Real-World Scenarios Where Multi-Hop Becomes Essential
Beyond the realm of high-stakes journalism, the need for Multi-Hop extends to various other scenarios where robust anonymity is paramount. Think of political dissidents organizing resistance movements in countries with severe internet censorship and surveillance. Their communications are constantly monitored, and any slip-up can lead to arrests, torture, or enforced disappearance. A single VPN might bypass some censorship, but the metadata—the timing and volume of connections to a specific VPN server—could still be used to identify potential users. Multi-Hop adds layers of obfuscation, making it far more difficult to profile and identify individuals based on their network activity. The double encryption and geographical separation introduce enough 'noise' to frustrate even advanced traffic analysis techniques, allowing these individuals to communicate and coordinate with a greater degree of safety. It's about providing a truly secure channel when the consequences of exposure are dire.
Another pertinent example involves whistleblowers within corporations or government agencies. These individuals often possess highly sensitive information that, if leaked, could expose corruption, illegal activities, or severe ethical breaches. Their digital communications are under immense scrutiny, and corporate security teams are often equipped with sophisticated tools to monitor internal networks. If a whistleblower uses a single VPN to leak documents, the connection to that VPN server from within the corporate network could still be flagged, and forensic analysis might trace it back to a specific internal IP. Multi-Hop, by adding an additional layer of indirection and external IP masking, makes it significantly harder for internal security teams to pinpoint the source of the leak, effectively creating a digital firewall that protects the whistleblower's identity. This isn't about enabling illicit activities, but about safeguarding those who bravely step forward to expose wrongdoing in the face of immense personal risk.
The Shadow of State-Sponsored Surveillance
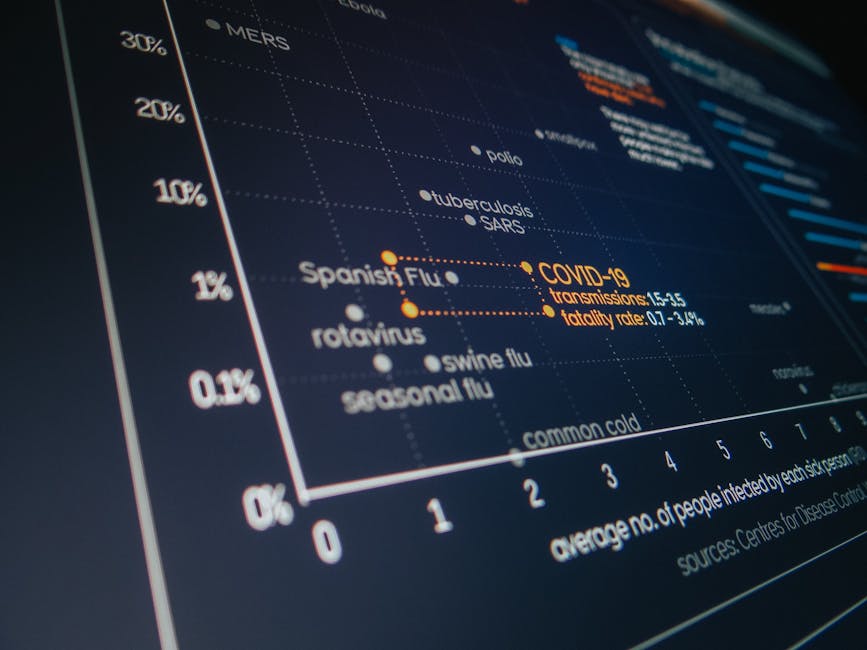
The specter of state-sponsored surveillance looms large over the digital landscape. Reports from organizations like Privacy International and the Electronic Frontier Foundation consistently highlight the vast reach and capabilities of intelligence agencies worldwide. These agencies often employ sophisticated tools, including deep packet inspection, traffic analysis, and even the ability to compel VPN providers to hand over data or install backdoors. While many reputable VPNs fight vigorously against such demands, the legal and political pressure can be immense. This is where the distributed trust model of Multi-Hop VPN truly shines. By scattering your digital footprint across multiple, geographically diverse servers, it creates a significant hurdle for any single government entity trying to track you. An agency in Country A might be able to monitor the first VPN server, but they would then need the cooperation of an agency in Country B (where the second server is located) to continue the trace, and potentially even more jurisdictions depending on the hops. This jurisdictional fragmentation makes comprehensive surveillance a logistical and legal nightmare, often rendering it impractical for all but the most high-priority targets.
Statistics on government requests for user data from tech companies and VPN providers paint a stark picture. Many companies receive thousands of such requests annually, and while some are fought, others are complied with, often under gag orders preventing public disclosure. This inherent vulnerability within the single-point-of-failure model underscores the necessity of features like Multi-Hop. It's a proactive defense mechanism against the increasingly aggressive posture of state actors in the digital realm. It acknowledges that even the most well-intentioned VPN provider might eventually face insurmountable pressure, and by designing a system that doesn't rely on the absolute infallibility of any single entity, it provides a much higher degree of resilience. This isn't about paranoia; it's about pragmatic security in an environment where digital privacy is constantly under assault, and the stakes for individuals are often incredibly high.
Expert Consensus on Layered Security
Cybersecurity experts and privacy advocates have long championed the principle of layered security, often summarized by the adage "defense in depth." This philosophy dictates that no single security measure is foolproof, and true resilience comes from combining multiple, independent layers of protection. Multi-Hop VPN perfectly embodies this principle. As Bruce Schneier, a renowned cryptographer and security expert, often emphasizes, "Security is a process, not a product." Relying solely on a single VPN connection, however strong, is akin to building a house with a single, albeit robust, front door. It's good, but a determined intruder might eventually find a way through or around it. Adding Multi-Hop is like adding a second, independently locked door behind the first, and then perhaps a third, each requiring a different key and a different method of entry. This exponential increase in complexity makes successful breaches far less likely.
Quotes from leading figures in the cybersecurity community frequently echo this sentiment. Dr. Steven Murdoch, a security researcher at University College London, has highlighted the challenges of traffic analysis against layered systems, noting that "the more hops and the more diverse the paths, the harder it is to correlate traffic." Similarly, privacy advocacy groups consistently advise users in high-risk environments to adopt multi-layered approaches, often recommending tools like Tor Browser in conjunction with VPNs, or explicitly mentioning Multi-Hop VPNs as a stronger alternative to single VPNs. The consensus is clear: for ultimate cybersecurity, especially when facing advanced threats, a single layer of protection is insufficient. Multi-Hop VPN represents a crucial step forward in implementing this layered security philosophy within the practical context of everyday internet usage, moving beyond mere encryption to active obfuscation and distributed anonymity. It's a recognition that the threat landscape demands more than just basic protection; it demands strategic, multi-faceted defense.
Case Study The Hypothetical Whistleblower Scenario
Let's paint a detailed hypothetical scenario: Imagine "Alex," an employee at a major tech company, discovers their employer is secretly collecting and selling highly sensitive user data without consent, a clear breach of privacy laws. Alex decides to blow the whistle. They need to leak documents to a trusted journalist, but doing so from their home network or corporate network carries immense risk. If Alex uses a standard VPN from home, their ISP will see a connection to a VPN server. If the company's internal security is sophisticated, they might notice Alex connecting to an external VPN from their corporate network. In either case, if the journalist's connection to the same VPN server is also monitored, or if the VPN provider is pressured, Alex's anonymity could be compromised.
Now, consider Alex using a Multi-Hop VPN. From their home, Alex connects to a VPN server in Canada (the first hop). This server encrypts their traffic and forwards it to a second VPN server in Switzerland (the second hop), which then connects to the journalist's secure drop box. Alex's ISP only sees a connection to the Canadian server. The Canadian server only knows Alex's real IP and the Swiss server's IP. The Swiss server only knows the Canadian server's IP and the journalist's dropbox IP. To trace Alex, the tech company or a government agency would need to compel the Canadian authorities to seize the Canadian server, then compel the Swiss authorities to seize the Swiss server, and then successfully correlate traffic across both. The legal and logistical hurdles are immense, especially given different international laws and privacy protections. This layered approach provides Alex with a significantly higher degree of plausible deniability and protection, making it a powerful tool for safeguarding those who dare to speak truth to power. It's a stark illustration of how a seemingly complex feature translates into real-world, life-saving security.