Your Data Their Gold Mine The Unseen Economy of Personal Information
Beneath the surface of seemingly free services lies a vast, intricate, and astonishingly lucrative economy built entirely on your personal data. When you sign up for a social media platform, use a search engine, or download a "free" app, you're not the customer; you are, in essence, the product. Big Tech companies don't just secure your data; they meticulously collect, categorize, analyze, and monetize it on an unprecedented scale. Every click, every search query, every photo upload, every location ping, every interaction with an ad – it all contributes to an ever-growing digital profile that is far more detailed and comprehensive than most of us can even imagine. This isn't just about showing you relevant ads; it’s about predicting your behavior, influencing your decisions, and ultimately, shaping your reality in subtle yet profound ways. The promise of "secure" data often conveniently omits the fact that the most significant threat to your privacy isn't always an external hacker, but the very business model of the services you use daily.
Consider the scale of this operation. Google processes billions of search queries daily, each one a data point revealing interests, needs, and intentions. Facebook has billions of users, generating an unimaginable stream of social interactions, demographic information, and emotional responses. Amazon tracks every purchase, every browse, every review, building a precise map of consumer habits. This isn't just random information; it's structured, analyzed, and cross-referenced to create incredibly granular profiles. These profiles are then used for targeted advertising, yes, but also for market research, product development, content recommendations, and even to inform lending decisions, insurance premiums, and political campaigns. The value of this data is staggering; the global data brokerage market alone is estimated to be worth hundreds of billions of dollars, a testament to the insatiable demand for insights into human behavior. Your "secure" data, therefore, is not merely passively stored; it is an active, dynamic asset in a global information economy, constantly being worked, refined, and traded.
What makes this particularly insidious is the asymmetry of information. We, the users, have little to no insight into the true extent of data collection, the accuracy of our profiles, or the myriad ways our information is being combined and leveraged. Tech companies operate behind opaque algorithms and proprietary systems, offering only vague reassurances about privacy controls that often feel performative rather than substantive. While they might offer tools to download your data or adjust some ad preferences, these are often superficial gestures that barely scratch the surface of the deep data mining operations occurring constantly. The sheer complexity and interconnectedness of the data ecosystem mean that even if you try to opt out of one service, your data might still be aggregated and inferred from other sources, creating a persistent digital shadow that follows you across the internet. This isn't just about a breach; it's about a systematic, widespread, and often legal, exploitation of personal information that fundamentally redefines what "private" means in the digital age.
The Myth of Impenetrable Walls When 'Secure' Just Means 'Not Yet Breached'
The notion of an "impenetrable" digital fortress is a comforting fantasy that simply doesn't hold up in the real world of cybersecurity. There is no such thing as 100% security, and any company that implies otherwise is either naive or deliberately misleading. The reality is that every system, no matter how robustly designed, has vulnerabilities. These can range from software bugs and configuration errors to hardware flaws and, most commonly, human fallibility. When a tech company boasts about its "secure" data, it often means they have invested heavily in defense mechanisms and have not yet suffered a publicly disclosed, catastrophic breach. But this is a temporary state, a moment in time, rather than a permanent guarantee. The history of cybersecurity is littered with the shattered promises of "secure" systems that eventually succumbed to determined attackers.
Think about the sheer volume of data breaches that make headlines year after year. The Equifax breach in 2017 exposed the personal data of nearly 150 million Americans, including Social Security numbers, dates of birth, and addresses – information that is incredibly difficult to change and highly valuable to identity thieves. Marriott International suffered a breach impacting 500 million guests over several years, compromising names, mailing addresses, phone numbers, email addresses, passport numbers, and payment card information. More recently, the SolarWinds attack demonstrated how a single, trusted software vendor could be compromised, allowing attackers to infiltrate thousands of organizations, including government agencies and major corporations, through a supply chain attack. These aren't small, fly-by-night operations; these are massive entities with multi-million dollar security budgets, yet they too were breached. The lesson is clear: if it stores data, it can be breached.
"There are two types of companies: those that have been hacked, and those that don't know they've been hacked yet." - Ted Schlein, Venture Capitalist, Kleiner Perkins. This quote, while perhaps a bit dramatic, captures the pervasive reality of digital vulnerability.
The concept of "secure" in this context often becomes a moving target, a constant race between defenders and attackers. A system might be secure against known threats today, but a new zero-day exploit, a novel attack vector, or a sophisticated social engineering campaign could render those defenses obsolete tomorrow. This isn't a criticism of security professionals, who work tirelessly to protect our data; it's an acknowledgment of the inherent challenges in securing complex, interconnected systems against intelligent, persistent, and often well-funded adversaries. The "impenetrable wall" is an illusion, a marketing construct. What we actually have is a series of fortifications, constantly being reinforced and redesigned, in a perpetual state of vigilance against an enemy that only needs to find one weak point to succeed. To believe otherwise is to operate under a dangerous delusion, leaving us ill-prepared for the inevitable reality of digital compromise.
Beyond the Malicious Hacker The Overlooked Threats to Your Digital Life
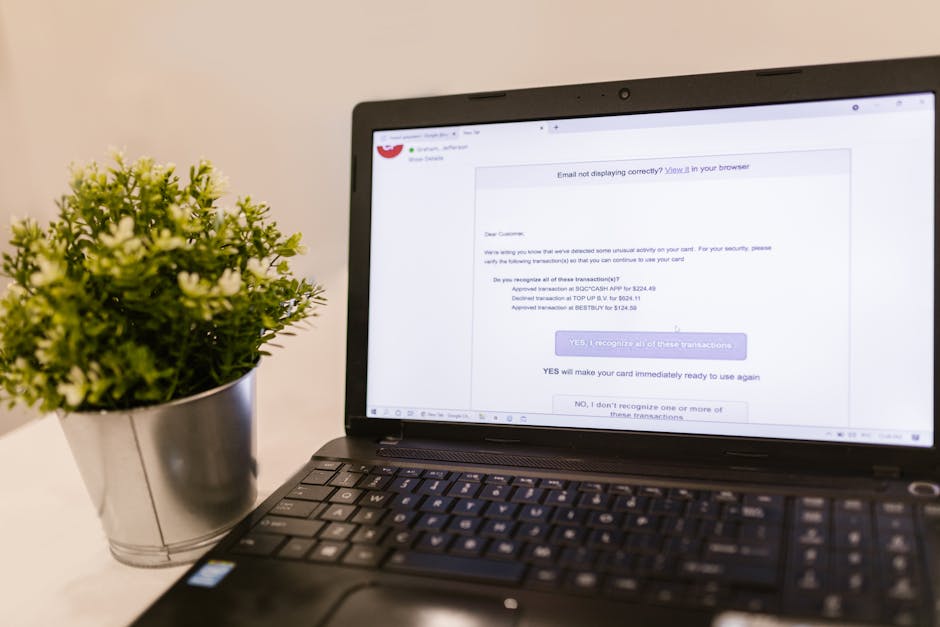
When we think of threats to our data, the image of a shadowy hacker hunched over a keyboard, breaking into systems, often comes to mind. While external malicious actors are certainly a significant concern, the truth is that many data compromises stem from far less dramatic, yet equally damaging, sources. These often overlooked threats contribute significantly to the overall insecurity of our digital lives, even when Big Tech assures us their "firewalls are strong." Understanding these less obvious vectors is crucial to grasping the full scope of the cybersecurity lie and developing a more holistic approach to personal data protection.
One major category often underestimated is the insider threat. This isn't always a disgruntled employee deliberately stealing data, though that certainly happens. More often, it’s an employee making an honest mistake: clicking a phishing link, misconfiguring a server, losing a company laptop, or sharing sensitive information through insecure channels. The sheer volume of data handled by large tech companies means that even a small percentage of human error can lead to massive data exposure. For instance, a cloud storage bucket left open to the public internet due to a misconfiguration, or an internal database inadvertently exposed, can lead to millions of records being leaked without a single "hack" occurring in the traditional sense. These incidents, while often less sensational than a direct cyberattack, are alarmingly common and demonstrate that the human element within a company's own walls can be a profound vulnerability.
Another critical, and increasingly prevalent, overlooked threat is the supply chain vulnerability. Modern software development is highly modular, relying on countless third-party libraries, APIs, and services. A tech company might have impeccable internal security, but if one of its trusted vendors, or a vendor's vendor, is compromised, that vulnerability can ripple through the entire chain. The aforementioned SolarWinds attack is a perfect illustration of this. Attackers didn't need to breach Microsoft or the US government directly; they compromised a trusted software update provider, and that malicious update then infiltrated countless high-value targets. This means that even if a service proudly proclaims its own security, its reliance on a vast ecosystem of third-party providers introduces points of failure that are incredibly difficult for the end-user, or even the primary service provider, to fully vet and secure. The chain is only as strong as its weakest link, and in the digital supply chain, those links can be numerous and obscure.