Firewalls and Antivirus Software Are Not the Fortress You Imagine
For decades, the firewall and antivirus software have been the twin pillars of conventional cybersecurity, the digital equivalent of a castle wall and a guard dog. Many organizations, particularly smaller ones, still place an enormous amount of faith in these tools as their primary line of defense. They are, without a doubt, essential components of any security strategy, providing foundational protection against a vast array of common threats. However, to view them as impenetrable fortresses capable of repelling all attacks is a dangerous misconception that can leave organizations catastrophically exposed. Their limitations, especially against modern, sophisticated threats, are becoming increasingly apparent, transforming them from ultimate guardians into merely one layer among many, and a layer with significant chinks in its armor.
Let's consider the humble firewall. Its primary job is to monitor and control incoming and outgoing network traffic based on predetermined security rules, essentially deciding what gets in and what stays out. This works wonderfully for preventing unauthorized access from the internet to internal networks, blocking known malicious IP addresses, and enforcing network segmentation. But what happens when the threat originates *inside* the network? A firewall, by design, often has a blind spot for internal lateral movement once an initial breach has occurred. An attacker who successfully compromises a single workstation through a phishing email can then move freely within the network, bypassing the very firewall designed to keep them out, because their traffic is now originating from a "trusted" internal source. Furthermore, misconfigurations are rampant; complex firewall rulesets are notoriously difficult to manage, and a single error can inadvertently open a gaping hole. Cloud environments introduce additional complexity, where traditional perimeter firewalls struggle to adapt to dynamic, distributed infrastructures, often leading to insecure configurations that are easy to overlook.
Then there's antivirus software, the digital immune system we've relied on for so long. Traditional antivirus primarily operates on a signature-based detection model, meaning it identifies malware by comparing file characteristics against a database of known threats. This is highly effective against widespread, well-documented viruses and worms. The problem, however, is that this approach is inherently reactive. It can only detect threats that have already been identified, analyzed, and added to its database. Modern attackers are far more agile. They employ polymorphic malware that constantly changes its code signature, making it difficult for signature-based AV to recognize. Even more insidious are fileless attacks, which operate entirely in memory, leveraging legitimate system tools and processes, leaving no malicious files on disk for the antivirus to scan. Zero-day exploits, vulnerabilities unknown to the vendor and therefore unpatched, also sail straight past traditional antivirus defenses, as there's no signature to match. While modern AV has evolved into Endpoint Detection and Response (EDR) solutions that incorporate behavioral analysis and machine learning, they are still not foolproof, and often struggle with highly targeted, novel attacks that don't fit established patterns.
The Human Element Our Most Vulnerable Link
Despite all the technological advancements, the stark reality remains: the human element continues to be the weakest link in the cybersecurity chain. No matter how sophisticated your firewalls, how cutting-edge your EDR, or how robust your encryption, a single click on a malicious link, a moment of inattention, or a lapse in judgment can unravel an entire defense strategy. This isn't a criticism of individuals; it's an acknowledgment of our inherent fallibility, our susceptibility to manipulation, and the sheer ingenuity of threat actors who understand psychology as well as, if not better than, they understand code. We are the ultimate "zero-day" exploit, constantly present, often predictable, and always a potential point of compromise.
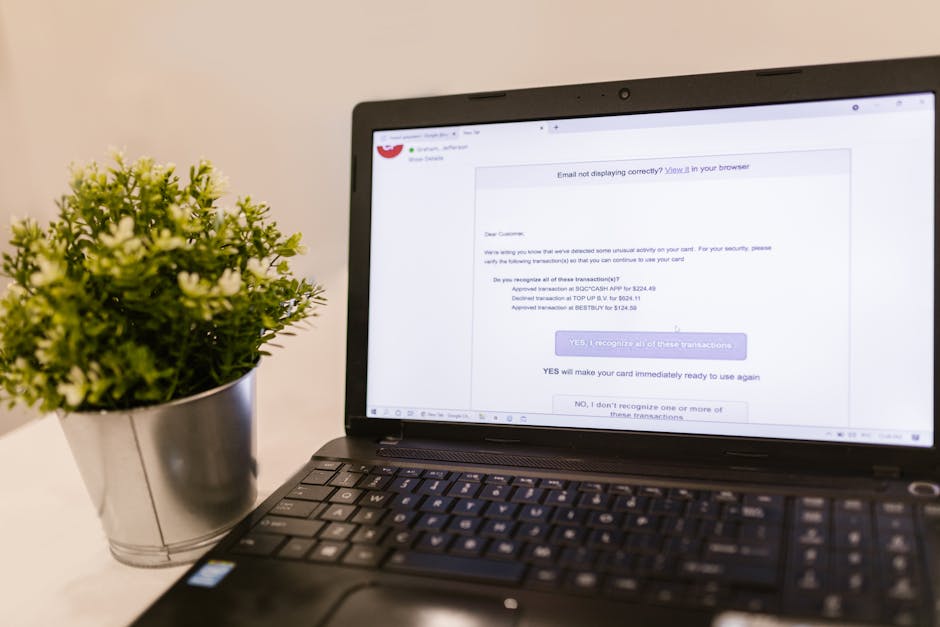
Social engineering, in its myriad forms, is the primary weapon targeting this human vulnerability. Phishing, the classic email scam, has evolved dramatically from poorly worded messages promising Nigerian fortunes. Today's phishing attacks are highly sophisticated, often spear-phishing campaigns meticulously crafted to impersonate trusted colleagues, vendors, or even senior executives. These emails leverage urgency, fear, or curiosity to trick recipients into revealing credentials, clicking malicious links, or downloading infected attachments. Pretexting involves creating an elaborate false scenario to gain trust and information, perhaps impersonating an IT support technician to gain remote access. Baiting involves enticing victims with physical media (like a USB stick dropped in a parking lot) or tempting online offers. And then there’s ransomware, often delivered via these social engineering vectors, encrypting an organization's critical data and holding it hostage, demonstrating the catastrophic real-world impact of a single human error.
The problem is compounded by a pervasive lack of effective, ongoing security awareness training. Many organizations treat security training as a one-off, annual compliance exercise, often a dry presentation that employees quickly forget. What's needed is a continuous, engaging, and relevant training program that fosters a culture of vigilance. Furthermore, insider threats, whether malicious or accidental, present a unique challenge. A disgruntled employee with privileged access can intentionally sabotage systems or exfiltrate sensitive data. More commonly, an accidental insider threat occurs when a well-meaning employee inadvertently causes a breach through negligence, such as using weak passwords, sharing confidential information on unsecured channels, or falling for a sophisticated phishing attack. Technology alone cannot solve these human-centric problems; it requires a deep understanding of human behavior, robust policies, and a commitment to continuous education and reinforcement.
The Illusion of Strong Passwords and Multi-Factor Authentication's Achilles' Heel
We've been told for years to use strong, unique passwords – a complex mix of uppercase, lowercase, numbers, and symbols. And for good reason; a strong password is a fundamental building block of digital security. Password managers have made this advice more actionable, allowing users to create and store incredibly complex, unique passwords for every service without having to remember them all. Yet, even with these advancements, the password remains a surprisingly fragile defense. Brute-forcing attacks, where attackers systematically try every possible character combination, are becoming more efficient with powerful computing resources. Credential stuffing, where stolen username/password pairs from one breach are tried across hundreds of other services, capitalizes on the common human tendency to reuse passwords. A single breach on an unrelated website can compromise your accounts everywhere if you’ve recycled your credentials, a stark reminder that even the strongest password on one site is only as strong as the weakest link in your digital footprint.
Multi-Factor Authentication (MFA) was hailed as the game-changer, the definitive answer to password vulnerabilities. By requiring a second form of verification – something you have (like a phone or hardware token) or something you are (biometrics) – in addition to something you know (your password), MFA significantly raises the bar for attackers. And indeed, it has been incredibly effective at preventing many common attacks, making it an absolute must for any critical account. However, even MFA, which I still advocate for vehemently, has its Achilles' heel. Threat actors are constantly devising ingenious ways to bypass it, turning what we thought was an ironclad lock into merely a stronger one, still susceptible to a determined and creative burglar.
MFA fatigue attacks, for instance, involve repeatedly sending MFA push notifications to a user's device until they, out of annoyance or confusion, inadvertently approve a malicious login request. SIM swapping is another insidious technique where attackers trick a mobile carrier into transferring a victim's phone number to a SIM card controlled by the attacker, thereby intercepting SMS-based MFA codes. Session hijacking, where an attacker steals a valid session cookie after the user has already authenticated with MFA, allows them to bypass subsequent MFA prompts entirely. Phishing campaigns have also evolved to capture MFA codes in real-time. A user might be directed to a fake login page that not only asks for their password but also immediately prompts them for their MFA code, relaying it directly to the attacker who then uses it to log into the legitimate service. These sophisticated bypass techniques demonstrate that while MFA is indispensable, it is not an unbreakable shield, and its effectiveness relies heavily on user awareness and the specific implementation of the MFA solution itself.