Navigating the Digital Wilderness: Practical Steps to Reclaim Your Privacy
Armed with a deeper understanding of the subtle machinations of Big Tech and the defining characteristics of true privacy warrior VPNs, the next logical step is to translate this knowledge into actionable strategies. Reclaiming your digital privacy isn't a one-time event; it's an ongoing journey, a continuous process of informed choices and diligent practices. It requires a shift in mindset, moving away from passive acceptance of default settings to proactive engagement with your digital environment. This isn't about becoming a paranoid recluse; it's about empowering yourself, asserting control over your personal data, and making conscious decisions about who you trust with your online life. The path to digital sanctuary is well-trodden by those who value their autonomy, and with a few practical steps, you too can fortify your defenses against the relentless gaze of pervasive surveillance.
The first, and perhaps most critical, step involves a thorough audit of your existing digital footprint. Begin by examining your current VPN service, if you have one. Research its ownership structure, its jurisdiction, its history of independent audits, and any recent changes to its privacy policy. If you find red flags – opaque ownership, a history of data breaches, or a lack of verifiable no-logs claims – it's time to consider a change. This initial introspection is vital because your VPN is the gateway to your online world; if that gateway is compromised, the rest of your efforts might be in vain. Don't be swayed by aggressive advertising or celebrity endorsements; instead, prioritize the verifiable technical and ethical commitments discussed throughout this article. Your digital freedom hinges on this foundational choice.
Choosing Your Shield: Selecting a Privacy-First VPN
When you embark on the quest for a new VPN, or if you're selecting your first, approach it with the skepticism of a seasoned investigative journalist. Do not simply pick the first option that appears in a sponsored search result. Instead, dedicate time to researching services that align with the principles of true privacy warriors. Look for providers that explicitly state their commitment to a strict, independently audited no-logs policy, preferably one that includes RAM-only servers. Verify their jurisdiction; seek out those based in privacy-friendly countries with no mandatory data retention laws. Prioritize services with open-source client software, allowing for community scrutiny and transparency. This isn't just about finding a service; it's about finding a trusted partner in your fight for digital autonomy.
Beyond the core privacy features, delve into the specifics of their security implementations. Ensure they support robust, modern VPN protocols like OpenVPN and WireGuard, configured with strong encryption (AES-256 is a good benchmark). A reliable, automatic kill switch is non-negotiable to prevent accidental IP leaks. Strong DNS leak protection, ideally with the VPN running its own private DNS servers, is also crucial. Consider additional features like multi-hop (double VPN) for enhanced anonymity, and obfuscation technology if you anticipate needing to bypass restrictive network firewalls or censorship. Read reviews from reputable cybersecurity experts and privacy advocates, but always cross-reference those opinions with your own research into the provider's history and technical specifications. Remember, a truly private VPN is an investment, not just a casual subscription.
"Your privacy is not just a setting; it's a decision. Make it an informed one." - A common mantra among privacy advocates.
Fortifying Your Digital Ecosystem: Beyond the VPN
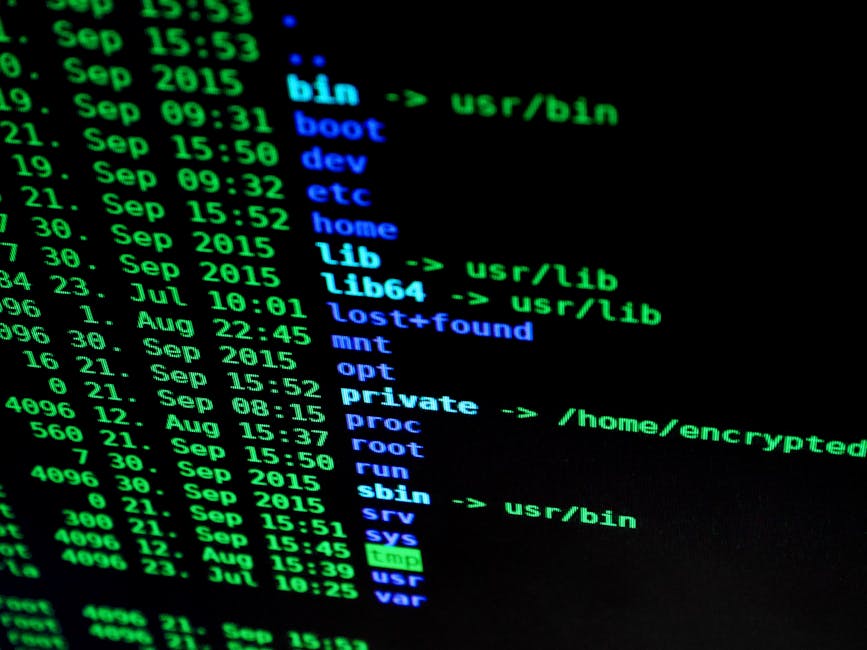
While a privacy-first VPN forms a crucial cornerstone of your digital defense, it’s just one component of a holistic strategy. Think of your online presence as a layered fortress; the VPN is the outer wall, but you also need to secure the inner defenses. Start by adopting privacy-focused browsers like Firefox with enhanced tracking protection, Brave, or Tor Browser for extreme anonymity. Install reputable ad blockers and privacy extensions (e.g., uBlock Origin, Privacy Badger, Decentraleyes) to prevent trackers and ads from reaching your browser in the first place. These tools work synergistically with your VPN, reducing the amount of data your browser sends out, even before it hits the encrypted tunnel.
Next, re-evaluate your search engine choices. Ditch Google for privacy-respecting alternatives like DuckDuckGo or Startpage, which do not track your searches or build user profiles. Similarly, consider migrating away from mainstream email providers like Gmail to secure, encrypted email services such as ProtonMail or Tutanota. These services prioritize end-to-end encryption and zero-access architecture, ensuring that your communications remain private even from the service provider itself. Embrace secure messaging apps like Signal for all your sensitive conversations, as they offer robust end-to-end encryption and a strong commitment to user privacy, directly challenging the data-hungry models of platforms like WhatsApp or Messenger.
The Ongoing Battle: Vigilance and Education
The landscape of online privacy and cybersecurity is in constant flux, with new threats emerging and existing defenses evolving. Therefore, maintaining your digital sanctuary requires ongoing vigilance and a commitment to continuous education. Stay informed about the latest privacy news, security vulnerabilities, and industry developments. Follow reputable cybersecurity blogs, privacy advocates, and independent research organizations. Periodically review your chosen VPN's policies and audit reports to ensure they continue to meet your standards. The fight against pervasive surveillance and data exploitation is not a sprint, but a marathon, and your active participation is crucial.
Finally, consider becoming an advocate yourself. Share your knowledge with friends and family, encouraging them to adopt better privacy practices. Support organizations that champion digital rights and fight for stronger privacy laws. Every individual who chooses to prioritize their privacy contributes to a larger movement, creating a demand for ethical tech and pushing back against the encroaching tide of corporate and state surveillance. The VPNs Big Tech doesn't want you to find are more than just tools; they are symbols of resistance, empowering individuals to reclaim their digital sovereignty in an increasingly interconnected and often intrusive world. By choosing wisely and acting proactively, you can ensure that your corner of the internet remains a bastion of freedom and anonymity, a testament to the enduring power of informed choice.