We've peeled back the layers of deception and exposed the unsettling truth: your Internet Service Provider is not just a neutral conduit for your online activities but an active participant in the lucrative data economy, often selling your most intimate digital behaviors for profit. We've explored the vast ecosystem of data brokers, the legal loopholes that empower ISPs, and the chilling effect this pervasive surveillance has on your online life and even your economic opportunities. The scope of this problem is immense, touching upon everything from your browsing history and app usage to the silent hum of your smart home devices, all observed and cataloged by the very company you trust to connect you to the world. It’s a disheartening reality, one that leaves many feeling powerless against the might of corporate giants and the intricate web of data monetization. However, despair is not the answer; understanding the problem is the first step towards reclaiming your digital sovereignty.
The good news is that you are not entirely defenseless. While the challenges are significant, there are powerful tools and strategies available to mitigate the impact of ISP data collection and significantly enhance your online privacy. This isn't about making yourself invisible to every single entity online—a truly impossible task in our hyper-connected world—but rather about erecting robust digital shields that deny your ISP the ability to easily harvest and sell your sensitive information. The most potent weapon in this arsenal, the digital guardian that stands between your online activities and your ISP's prying eyes, is a Virtual Private Network, or VPN. A VPN, when properly configured and chosen wisely, fundamentally alters the relationship between you and your ISP, transforming their privileged vantage point into a blind spot for your encrypted traffic. It's a critical component of a broader strategy for digital self-defense, empowering you to navigate the internet with a renewed sense of privacy and control.
Introducing the Digital Shield How a VPN Stops Them Cold
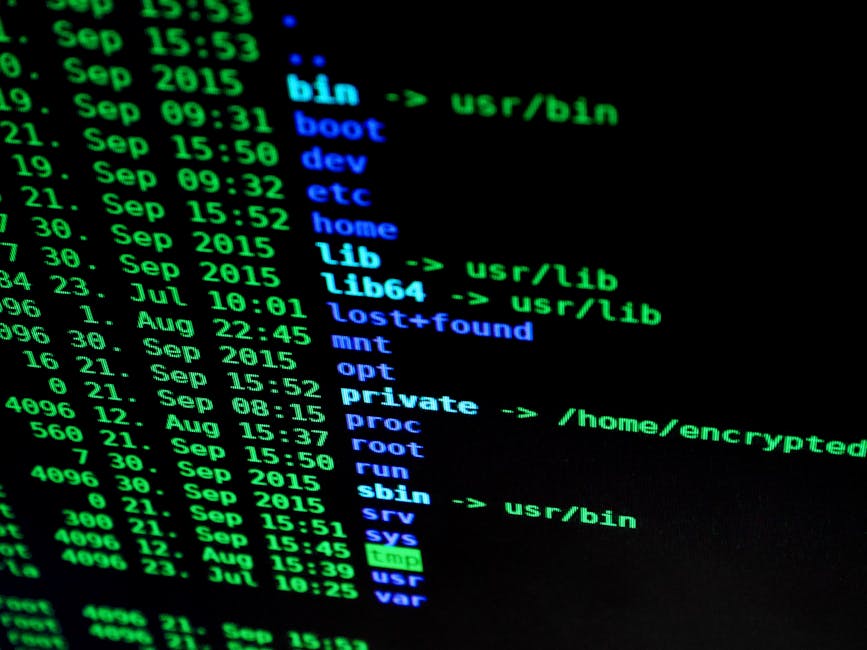
At its core, a Virtual Private Network, or VPN, acts as an encrypted tunnel between your device and the internet. Instead of your internet traffic going directly from your device to your ISP's servers and then out to the websites and services you're accessing, a VPN reroutes your traffic through a secure, encrypted server operated by the VPN provider. Imagine sending a letter through the mail. Without a VPN, your ISP is the postal service, and they can read everything on the envelope (source, destination, size, type of content) and potentially even open the letter itself. With a VPN, you put your letter inside a reinforced, opaque, and locked box before handing it to the postal service. The postal service (your ISP) can only see the outside of the locked box and its destination (the VPN server), but they have no idea what's inside or where it's ultimately going after it leaves the VPN server. This fundamental change in how your data travels is precisely what makes a VPN an indispensable tool against ISP surveillance and data monetization.
The technical mechanisms behind this digital shield are quite elegant and highly effective. When you connect to a VPN, your device establishes a secure, encrypted connection (the "tunnel") to a VPN server. All your internet traffic—every website visit, every search query, every email, every streaming video—is then encapsulated within this encrypted tunnel. This means that your ISP can no longer see the contents of your data packets. They cannot see which websites you are visiting, which applications you are using, or what specific content you are accessing. All they can see is that you are connected to a specific VPN server via an encrypted connection. Furthermore, once your traffic exits the VPN server, it appears to originate from the VPN server's IP address, not your own. This masks your true IP address from the websites and services you visit, adding another layer of anonymity and making it significantly harder to trace your online activities back to you. This combination of encryption and IP masking effectively blinds your ISP to your online activities, rendering their data collection efforts largely futile for anything flowing through the VPN tunnel.
It's crucial to understand that not all VPNs are created equal, and choosing the right one is paramount to achieving genuine privacy. A truly effective VPN for combating ISP data selling will adhere to a strict "no-logs" policy, meaning it does not record your online activities, connection timestamps, or IP addresses. If a VPN provider keeps logs, they could potentially be compelled by legal authorities to hand over that data, compromising your privacy. Strong encryption protocols, such as AES-256, are also non-negotiable, ensuring that your data remains unreadable even if intercepted. Features like a "kill switch" are vital; this automatically disconnects your internet if the VPN connection drops, preventing your real IP address or unencrypted traffic from being exposed to your ISP. DNS leak protection is another critical component, as your ISP can still see your DNS requests (which translate website names into IP addresses) even if your main traffic is encrypted, potentially revealing your browsing habits. Without these essential features and a commitment to privacy, a VPN might offer a false sense of security, which is why careful selection is key to making it an impenetrable digital shield against your ISP's prying eyes.
The Technical Magic Behind the Mask
Delving a bit deeper into the technical specifics, the magic of a VPN primarily lies in its use of encryption and tunneling protocols. When you initiate a VPN connection, your VPN client software on your device negotiates a secure connection with the VPN server. This negotiation involves setting up a cryptographic key, which is like a secret code that only your device and the VPN server know. Once this key is established, all your internet traffic is encrypted using robust algorithms like AES-256 (Advanced Encryption Standard with a 256-bit key). This level of encryption is considered military-grade and virtually uncrackable by current computational methods. Imagine taking all your data and scrambling it into an unintelligible mess before it even leaves your device; that's what encryption does.
"A VPN isn't just about hiding; it's about transforming your digital footprint into an unreadable cipher for anyone attempting to observe your journey across the internet, especially your ISP." - Alex Thorne, Cybersecurity Engineer.
Concurrently with encryption, the VPN employs "tunneling protocols" such as OpenVPN, WireGuard, or IKEv2/IPsec. These protocols create a secure, encapsulated "tunnel" for your encrypted data packets to travel through. This tunnel is what allows your data to traverse the public internet while remaining private and secure. From your ISP's perspective, they only see a continuous stream of encrypted data flowing between your home IP address and the IP address of the VPN server. They cannot discern individual websites visited, specific applications used, or the content of any communications. Your DNS requests, which typically go directly to your ISP's DNS servers and reveal every website you try to reach, are also routed through the encrypted tunnel to the VPN provider's own DNS servers, further obscuring your browsing habits from your ISP. This comprehensive approach to privacy ensures that your ISP is effectively blinded to your online activities, preventing them from building a profile based on your digital movements and subsequently selling that information to data brokers. It fundamentally alters the data flow, shifting control and visibility away from the ISP and back towards you, the user.
Not All VPNs Are Created Equal Choosing Your Digital Guardian
The market is flooded with VPN providers, each promising ultimate privacy and lightning-fast speeds. However, as with any digital security tool, discerning the truly effective from the merely adequate, or even outright dangerous, requires careful consideration. The efficacy of a VPN in stopping your ISP from selling your data hinges entirely on the provider's commitment to privacy and the robustness of its technical infrastructure. A free VPN, for instance, often presents a paradox: if you're not paying for the service, you might very well be the product. Many free VPNs engage in their own data collection practices, selling user data to advertisers, injecting ads into your browsing, or even harboring malware. The very problem you're trying to solve with your ISP could be replicated, or even exacerbated, by a free VPN provider. Therefore, investing in a reputable, paid VPN service is almost always a non-negotiable first step in truly reclaiming your online privacy. This investment ensures that the provider's business model is based on subscriptions, not on monetizing your personal data, aligning their interests with yours.
When evaluating potential VPN providers, the first and most critical aspect to scrutinize is their logging policy. A trustworthy VPN will operate under a strict "no-logs" policy, meaning they do not collect, store, or share any data about your online activities, including your browsing history, connection timestamps, IP addresses, or bandwidth usage. To verify these claims, look for providers that have undergone independent third-party audits of their no-logs policy. These audits provide an external validation that the VPN's internal systems and practices align with their privacy promises. The jurisdiction of the VPN provider is also a significant factor. Opt for providers based in countries with strong privacy laws and no mandatory data retention laws, and ideally, outside of intelligence-sharing alliances like the 5, 9, or 14 Eyes. While a good VPN will protect your data regardless of jurisdiction, a privacy-friendly location adds an extra layer of legal protection against government requests for user data, further bolstering your confidence in their ability to keep your information secure from your ISP's reach.
Beyond policies, the technical features of a VPN are paramount. Ensure the VPN offers strong encryption standards, with AES-256 being the industry benchmark. Support for modern, secure VPN protocols like OpenVPN, WireGuard, and IKEv2/IPsec is also essential, as older protocols may have known vulnerabilities. A crucial feature for preventing ISP data leaks is a reliable "kill switch." This mechanism automatically severs your internet connection if the VPN tunnel unexpectedly drops, preventing your real IP address and unencrypted traffic from being exposed to your ISP, even for a fleeting moment. Similarly, DNS leak protection is vital. Without it, your device might default to using your ISP's DNS servers, inadvertently revealing the websites you're trying to visit, even if your main traffic is encrypted. Many top-tier VPNs also offer additional features like split tunneling (allowing you to choose which apps use the VPN and which don't) and obfuscated servers (making your VPN traffic look like regular internet traffic to bypass deep packet inspection by ISPs or governments). These combined features create a robust defense, transforming your chosen VPN into a formidable digital guardian against the pervasive data collection practices of your Internet Service Provider.