Crafting Your Digital Doppelgänger: Building Detailed User Profiles
All these individual pieces of data – your browsing history, bandwidth usage, device information, app activity, and geolocation – aren't just collected in isolation. Your ISP aggregates them, correlates them, and meticulously pieces them together to construct incredibly detailed and comprehensive user profiles. Think of it as a digital doppelgänger, a shadow self created from every digital interaction you make. This profile isn't just a list of facts; it's an evolving narrative of your life, interests, habits, and even your potential vulnerabilities. It can include your assumed gender, age, income bracket, political leanings, health concerns, purchasing habits, and even your family status, all inferred from your online behavior.
These profiles are then used for a multitude of purposes, primarily targeted advertising, but also for market research, service development, and even risk assessment. An ISP might use your profile to recommend specific internet plans or bundled services, or they might sell segments of these profiles to advertisers looking for very specific demographics. The scary part is that you rarely, if ever, get to see this profile yourself, nor do you have much say in how it's constructed or used. It exists as a proprietary asset of your ISP, a digital representation of you that is constantly being refined and leveraged for profit, often without your direct knowledge or meaningful consent. It’s a powerful testament to the value of data in the modern economy, and a sobering reminder of how much of ourselves we unwittingly give away.
The Legal Imperative: Responding to Government Requests and Subpoenas
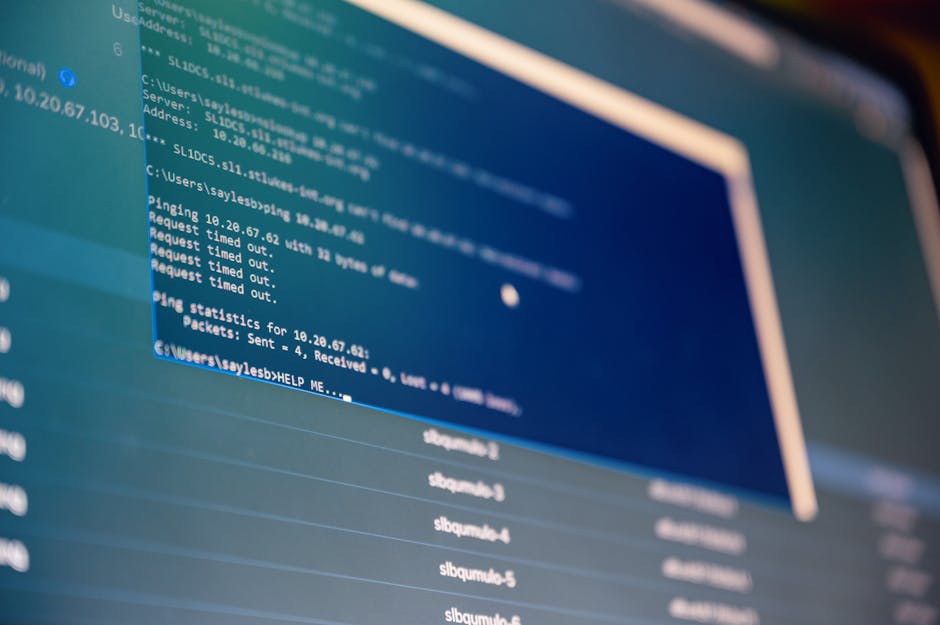
Beyond commercial motivations, ISPs also operate under legal obligations that compel them to hand over your data to government agencies and law enforcement. In many jurisdictions, including the United States, ISPs are subject to subpoenas, warrants, and national security letters that require them to disclose customer information, browsing history, connection logs, and even real-time communications. While there are typically legal processes involved, the sheer volume of these requests is often astounding, and the extent to which ISPs push back on them varies widely.
This means that even if your ISP itself isn't actively "spying" on you for commercial gain at a particular moment, they are still a potential conduit for state surveillance. Your data, diligently collected and stored, can be accessed by authorities without your knowledge, provided they follow the proper legal channels. While these powers are often justified for national security or criminal investigations, the potential for abuse or overreach is a constant concern for privacy advocates. The fact that your ISP holds such a treasure trove of your personal data makes them an attractive target for these requests, turning them into unwilling (or sometimes willing) partners in state-sponsored surveillance. It underscores the critical need for individuals to take proactive steps to protect their data, knowing that it can be accessed by powerful entities far beyond their control.
Reclaiming Your Digital Freedom: The VPN Solution
After dissecting the myriad ways your ISP can peer into your digital life, the question naturally arises: what can be done? Is online privacy an unattainable myth in this era of pervasive surveillance? Thankfully, no. While no single solution offers a complete panacea, one of the most powerful and accessible tools at your disposal is a Virtual Private Network, or VPN. Think of a VPN as a highly secure, encrypted tunnel that you create between your device and the internet. Instead of your internet traffic going directly from your device to your ISP and then to its destination, it first travels through this encrypted tunnel to a VPN server, and only then emerges onto the open internet. This simple rerouting and encryption fundamentally changes the game.
When you connect to a reputable VPN service, your internet traffic is immediately encrypted, essentially scrambling it into an unreadable format. This encrypted data then travels through the secure tunnel to a VPN server, which could be located anywhere in the world. From the perspective of your ISP, all they can see is that you've connected to a VPN server, and that an encrypted stream of data is flowing between you and that server. They cannot see the contents of that data, nor can they see your ultimate online destination. It's like putting your entire digital life inside a locked, opaque box before handing it to your ISP, and then that box is delivered to a neutral third party before it's ever opened. This simple yet profound change in how your data travels online effectively neutralizes most of the ISP spying methods we’ve discussed.
Silencing the DNS Watchers and Thwarting Deep Packet Inspection
One of the most immediate benefits of a VPN is how it neutralizes your ISP's DNS logging capabilities. When you use a VPN, your device typically uses the VPN provider's DNS servers instead of your ISP's. This means your DNS queries, which reveal every website you visit, are handled by the VPN provider, not your ISP. A good, no-logs VPN provider will not keep records of your DNS queries, effectively erasing your browsing history from your ISP's view. Your ISP will only see encrypted traffic going to the VPN server, completely oblivious to the websites you're actually accessing. This single change dramatically enhances your browsing anonymity.
Furthermore, the robust encryption employed by quality VPNs renders Deep Packet Inspection (DPI) largely useless for your ISP. Since all your traffic is encrypted within the VPN tunnel, your ISP cannot "peek" into the packets to discern their content. They cannot identify the specific applications you're using, the content you're viewing, or keywords within your communications. All they see is an undecipherable stream of encrypted data. This means they can't use DPI to throttle specific services like streaming or P2P, because they simply cannot identify what those services are. The VPN essentially blinds your ISP to the nature of your online activities, restoring a significant degree of privacy and control over your internet experience. It's like speaking in a secret code that only you and your trusted confidante (the VPN server) understand.
Disrupting Ad Injection, Data Selling, and Geolocation Tracking
The encrypted tunnel provided by a VPN also acts as a powerful deterrent against ad injection and the sale of your "anonymized" data. If your ISP cannot see the websites you visit or the content of your traffic, they cannot inject their own ads into your browsing stream. The encrypted connection prevents them from manipulating the data packets to insert third-party content. Similarly, if your ISP cannot identify your activities or associate them directly with you, the data they collect becomes far less valuable for sale to data brokers. They might still collect metadata about your connection to the VPN server, but the rich, detailed behavioral data that makes you a valuable commodity simply isn't available to them.
When it comes to geolocation tracking, a VPN completely masks your true IP address. Instead of your ISP seeing your real IP, which is tied to your physical location, they only see the IP address of the VPN server you're connected to. From the perspective of any website or online service, your connection appears to originate from the location of the VPN server, not your actual home. This provides a powerful layer of anonymity, making it incredibly difficult for your ISP, or anyone else, to pinpoint your physical whereabouts based on your online activity. This is particularly useful for bypassing geo-restrictions on content, but its primary benefit is the enhanced privacy it offers against location-based surveillance. It's like wearing an invisibility cloak that makes your true location disappear from the digital map.
Beyond the VPN: Strengthening Your Digital Fortress
While a VPN is an indispensable tool in your privacy arsenal, it's important to remember that it's part of a broader strategy. No single tool is a silver bullet, and a multi-layered approach offers the best defense. Firstly, always prioritize websites and services that use HTTPS (Hypertext Transfer Protocol Secure). The "S" signifies an encrypted connection between your browser and the website, adding another layer of security. Look for the padlock icon in your browser's address bar. Many browsers even offer extensions like "HTTPS Everywhere" to automatically enforce secure connections where available.
Secondly, consider adopting privacy-focused browsers and search engines. Browsers like Brave, Firefox (with enhanced tracking protection), or Tor Browser are designed with privacy in mind, often blocking trackers and ads by default. Similarly, search engines like DuckDuckGo or Startpage offer anonymous search results, ensuring your queries aren't logged or used to build a profile. Disabling third-party cookies in your browser settings and regularly clearing your cache can also help reduce tracking. Finally, practice good digital hygiene: use strong, unique passwords for all your accounts, enable two-factor authentication wherever possible, and be extremely cautious about what information you share on social media. Your digital footprint is vast, and every conscious step you take to manage it contributes to a more private and secure online existence. The battle for digital sovereignty is ongoing, but with the right tools and knowledge, you can significantly tip the scales in your favor.