When Algorithms Decide Who You Are The Perils of Automated Identity Verification
As the digital realm expands and the sheer volume of online interactions skyrockets, the need for efficient and scalable identity verification has become paramount. Enter automated identity verification systems, powered by sophisticated algorithms and artificial intelligence. From opening a new bank account online to verifying your age for an e-commerce purchase, these systems are increasingly making decisions about who we are, based on a combination of document scans, facial recognition, and data cross-referencing. The promise is speed, accuracy, and a reduction in human error and bias. However, this reliance on algorithms to make critical judgments about our identities introduces a new set of terrifying vulnerabilities and ethical dilemmas. What happens when the algorithm gets it wrong? What if a sophisticated attacker learns to bypass these automated checks, creating a digital identity that the machines deem legitimate, even if it's entirely fabricated or stolen? The shift from human-centric verification to algorithmic gatekeeping fundamentally alters the battleground for identity theft, presenting new challenges that we are only beginning to grapple with.
The core of automated identity verification often involves comparing a user's live biometric data (like a selfie or a video scan) with an official government ID document (passport, driver's license). AI algorithms analyze facial features, document authenticity, and liveness detection to confirm identity. While seemingly robust, these systems are not infallible. They can be vulnerable to sophisticated deepfake technology, where a generated face is presented as live, or to expertly forged documents that pass initial algorithmic scrutiny. The problem is that these algorithms are trained on vast datasets, and if those datasets contain biases or are not comprehensive enough to account for all variations in human appearance or document types, they can produce false positives or false negatives. Imagine being denied access to a critical service because an algorithm incorrectly flagged your authentic document as fraudulent, or worse, because it couldn't recognize your face due to lighting conditions or a subtle difference from your ID photo. The lack of human oversight in these initial stages can lead to frustrating and even debilitating consequences for legitimate users, while simultaneously creating new pathways for determined fraudsters.
Furthermore, the data used by these automated systems is often sourced from multiple databases, some public, some private, some government-held. This aggregation of data, while intended to bolster verification, also creates a complex web of potential vulnerabilities. A breach in any one of these interconnected databases could provide identity thieves with the information needed to construct a synthetic identity that passes algorithmic checks. If an attacker can obtain a high-quality scan of a legitimate ID and pair it with a deepfake video of the person, they could potentially bypass even advanced automated systems. The terrifying aspect is that once an algorithm "believes" a fake identity is real, it can grant access to a multitude of services, creating a legitimate digital footprint for a completely fraudulent persona. This means that the future of identity theft isn't just about stealing your existing identity; it's about manipulating the very systems designed to verify identity, convincing the machines that a lie is the truth, and thereby gaining access to the digital keys to your kingdom, or to an entirely new kingdom built on deception.
The Data Broker Bazaar Your Identity on the Open Market
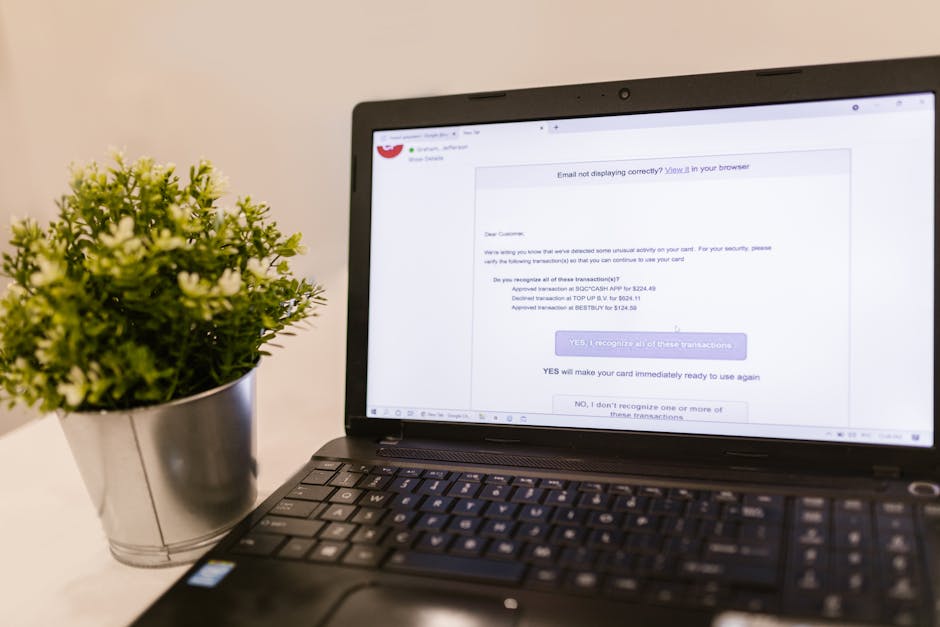
Beneath the surface of our everyday internet usage, a sprawling, opaque industry thrives: the data broker market. These companies collect, aggregate, and sell vast quantities of personal information, often without our explicit knowledge or consent. Every click, every purchase, every search query, every public record – it all contributes to an incredibly detailed digital profile that is then bought and sold like a commodity. This isn't just about advertising; it's about assembling the puzzle pieces of your entire life, making it a terrifyingly efficient resource for identity thieves. Your name, address, phone number, email, age, gender, marital status, income level, political affiliations, hobbies, health conditions, purchasing habits, and even your approximate net worth can all be found in this digital bazaar. It’s an open market for the very ingredients that make up your digital identity, making it a primary breeding ground for advanced identity theft.
The sheer volume and granularity of data available from data brokers are staggering. Imagine a fraudster purchasing a dossier on you that includes not just your contact information, but also your past addresses, relatives' names, vehicle information, and even court records. This level of detail provides an unparalleled advantage for social engineering attacks. With enough personal context, a scammer can craft a phishing email so convincing, or a vishing call so persuasive, that it becomes almost impossible to distinguish from a legitimate interaction. They can reference specific events in your life, mention mutual acquaintances, or mimic the communication style of institutions you interact with regularly. This isn't random guessing; it's a precisely targeted psychological operation, made possible by the legal, albeit ethically questionable, trade in personal data. The data broker industry, while often claiming to operate within legal boundaries for marketing and risk assessment purposes, inadvertently fuels the engine of identity theft by making personal information so readily accessible to anyone willing to pay.
The insidious nature of the data broker market is that it often operates in the shadows, making it incredibly difficult for individuals to ascertain what data is being collected about them, by whom, and for what purpose. Opt-out mechanisms, where they exist, are often cumbersome and ineffective, requiring individuals to contact dozens or even hundreds of brokers individually. This asymmetry of information and power leaves us vulnerable. Our digital identities are being meticulously mapped and cataloged, creating a persistent risk profile that we have little control over. When this wealth of data falls into the wrong hands – whether through direct purchase by criminals or through breaches of data broker databases themselves – the consequences are profound. It means that even if you are diligent about your personal security, your identity is still being exposed and monetized in ways you can't see or easily prevent. This ubiquitous trade in personal information fundamentally undermines our ability to protect our digital selves, transforming our lives into open books for anyone with malicious intent and a credit card.
Quantum Computing's Shadow The Threat to Encryption and Digital Identity
For decades, the bedrock of digital security has been cryptography, the science of secure communication. Our online banking, secure messaging, VPN connections, and indeed, the very integrity of our digital identities, all rely on complex mathematical algorithms that are practically impossible for conventional computers to break. The keys to our digital kingdoms are protected by the strength of these algorithms, ensuring that our data remains confidential and authentic. However, a seismic shift is on the horizon, one that threatens to shatter the very foundations of modern encryption: quantum computing. While still in its nascent stages, the development of quantum computers capable of solving problems far beyond the reach of classical supercomputers poses an existential threat to current cryptographic standards. If these machines become powerful enough, they could render our most robust encryption algorithms obsolete, exposing every piece of encrypted data and every digital identity to unprecedented levels of compromise. This isn't a distant science fiction scenario; it's a looming threat that demands immediate attention and a radical rethinking of our digital security posture.
The primary concern revolves around Shor's algorithm, a theoretical quantum algorithm proven to efficiently factor large numbers. The security of widely used public-key cryptographic systems, such as RSA and ECC (Elliptic Curve Cryptography), relies on the computational difficulty of factoring large prime numbers or solving discrete logarithm problems. A sufficiently powerful quantum computer, leveraging Shor's algorithm, could break these encryption schemes in a matter of minutes, effectively nullifying the security of virtually all current encrypted communications and stored data. This means that any data encrypted today, from your personal financial records to your biometric templates, could be decrypted by a future quantum computer. This "harvest now, decrypt later" threat is particularly terrifying for digital identity, as sensitive information like Social Security numbers, passport details, and even private keys used for digital signatures could be exposed. The very trust mechanisms that underpin our digital economy would crumble, leaving individuals and institutions alike vulnerable to wholesale identity theft and manipulation on an unimaginable scale.
The implications for digital identity are profound. If the encryption protecting our identity databases, our authentication protocols, and our digital certificates becomes compromised, the integrity of our entire digital presence is at risk. Imagine a world where your digital signature, once legally binding, could be forged with ease, or where secure channels used to verify your identity could be intercepted and manipulated. The transition to "post-quantum cryptography" (PQC) – new cryptographic algorithms designed to withstand quantum attacks – is already underway, but it's a massive undertaking. It requires updating countless systems, protocols, and devices globally, a process that will take years, if not decades. In the interim, the window of vulnerability grows. This quantum threat isn't just about breaking a password; it's about dismantling the very mathematical scaffolding that protects our digital identities, ushering in an era where the concept of secure online identity, as we know it, could become a relic of the past, unless we act decisively and swiftly to prepare for this paradigm shift.
The Deep Web's Dark Bazaar Your Identity for Sale
While the surface web is where we conduct our daily digital lives, beneath it lies the deep web, and within that, the dark web – a hidden corner of the internet accessible only through specialized software like Tor. This shadowy realm, often associated with illicit activities, plays a terrifyingly central role in the ecosystem of digital identity theft. It operates as a vast, unregulated marketplace where stolen personal data, credentials, and even entire digital identities are bought and sold like commodities. For identity thieves, it's a one-stop shop for acquiring the raw materials needed to impersonate individuals, commit fraud, and unravel lives. The dark web's anonymity and lack of oversight provide a fertile ground for criminals to operate with impunity, making it a persistent and growing threat to our digital identities.
In the dark web's hidden forums and marketplaces, you can find virtually any piece of personal information imaginable. Stolen credit card numbers, complete with CVVs and expiration dates, are sold for as little as a few dollars. "Fullz" – comprehensive dossiers containing names, addresses, Social Security numbers, dates of birth, and even mothers' maiden names – command higher prices, often hundreds of dollars, because they provide enough information to open new accounts or commit sophisticated fraud. You can buy hacked login credentials for streaming services, online banking, and social media accounts. Even more disturbing, some sellers offer "identity packages" that include scanned copies of passports, driver's licenses, and utility bills, essentially providing a complete toolkit for impersonation. The ease with which these sensitive data points can be acquired makes the dark web a critical enabler for various forms of identity theft, transforming what might have been a minor data breach into a full-blown identity crisis for the victims.
The existence of this dark bazaar means that even if you are meticulous about your personal security, your identity could still be compromised through no fault of your own. A data breach at a seemingly unrelated company could lead to your personal information appearing for sale on the dark web, ready to be exploited by the highest bidder. The anonymity provided by the dark web also makes it incredibly difficult for law enforcement to track down and prosecute these criminals, perpetuating a cycle of theft and exploitation. The sheer volume of compromised data available, combined with the low barrier to entry for buyers, means that the threat of identity theft is no longer just about individual hackers; it's about an organized, global criminal enterprise. Understanding the role of the dark web in this ecosystem is crucial, as it underscores the need for proactive monitoring of our personal information and a recognition that our digital identities are constantly under threat, not just from direct attacks, but from a pervasive, hidden market that profits from our stolen selves.