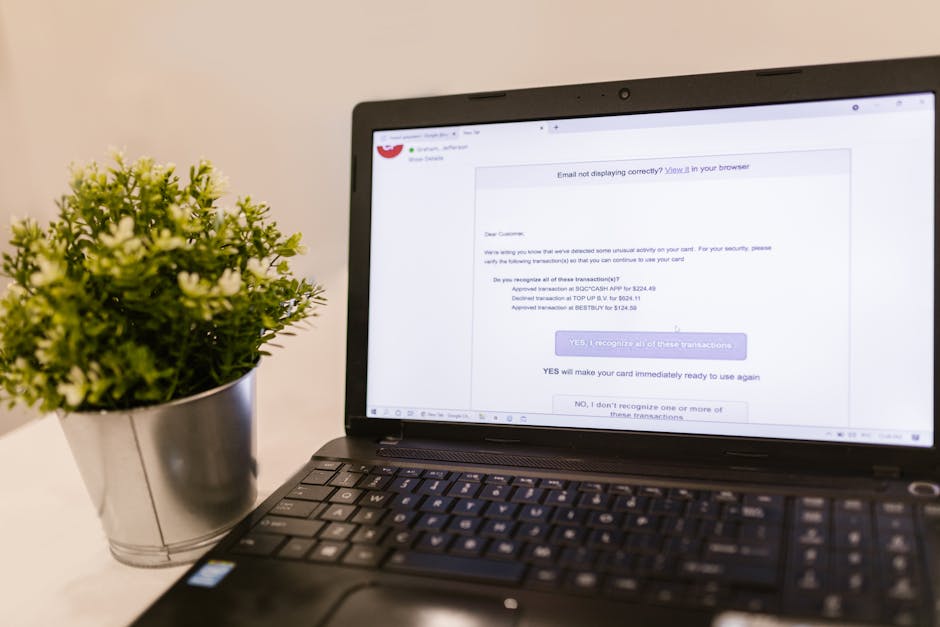
The allure of a VPN is undeniable: a simple click, and suddenly, you're a ghost in the machine, anonymous and unburdened by the constant surveillance that plagues the modern internet. This powerful narrative, heavily promoted by VPN providers, has led to a widespread but often misguided perception among users. Many believe that merely installing a VPN application and seeing the "connected" status is an impenetrable shield, a magic bullet against all online threats. This belief, while comforting, fosters an illusion of privacy that can be dangerously misleading. It creates a "set it and forget it" mentality, where users assume the software handles everything, absolving them of the responsibility to understand the nuances of their digital defenses. The reality, however, is far more complex, revealing that your VPN might be a false prophet, promising absolute security while silently harboring vulnerabilities that could expose your most sensitive data. This dissonance between user expectation and technical reality is a critical gap in our collective understanding of online privacy.
The marketing of VPNs, while effective in raising awareness about privacy, often oversimplifies the technical complexities involved. Phrases like "military-grade encryption" and "total anonymity" are plastered across websites, creating an image of invincibility. While technically true regarding certain aspects, these slogans often gloss over the critical importance of user configuration, network conditions, and the inherent limitations of any software. The truth is, a VPN is a tool, and like any powerful tool, its effectiveness is heavily dependent on how it's used and maintained. A skilled carpenter can build a magnificent structure with a hammer and saw, while an amateur might struggle to drive a single nail straight. Similarly, a VPN in the hands of an informed user, who understands its settings and potential pitfalls, is a formidable privacy guardian. But in the hands of someone operating under an illusion of effortless security, it can become a leaky bucket, creating a false sense of safety that ultimately leads to exposure. It's this gap in knowledge and proactive engagement that truly undermines the promise of a VPN.
The Illusion of Privacy Why Your VPN Might Be a False Prophet
The "set it and forget it" mentality is perhaps the most insidious threat to VPN efficacy. Users download a VPN, enable it once, and then rarely, if ever, revisit its settings. They trust that the default configuration is sufficient, or they simply don't know enough to question it. This passive approach is a significant vulnerability. As we've discussed, critical features like the Kill Switch are often not enabled by default, or they are presented as optional add-ons rather than essential safeguards. Furthermore, the internet landscape is constantly evolving, with new protocols, browser technologies, and attack vectors emerging regularly. A VPN configuration that was perfectly adequate two years ago might now be riddled with unnoticed leaks. Without periodic review, testing, and adjustment of settings, users are essentially operating with outdated defenses in a rapidly changing digital battlefield. This complacency, born from an illusion of effortless privacy, is precisely what adversaries and data brokers exploit, turning your expensive VPN subscription into a mere placebo.
The role of user configuration in ensuring comprehensive VPN security cannot be overstated. While VPN providers strive to make their applications user-friendly, the sheer number of options and technical jargon can be overwhelming. Many users simply click through setup wizards, accepting defaults without understanding their implications. This often means neglecting features like custom DNS settings, which can further enhance privacy by using trustworthy, audited DNS resolvers instead of the VPN provider's defaults, or even split tunneling, which, if improperly configured, can inadvertently bypass the VPN for certain applications, leading to exposure. The responsibility for securing your digital life ultimately falls on you, the user. A VPN is a powerful enabler, but it's not a magic bullet that negates the need for personal vigilance and proactive engagement with its capabilities. It truly boggles the mind how many people invest in a premium VPN service only to leave its most vital defenses disarmed, completely unaware of the risks they are running.
The implementation of these crucial features also varies wildly among VPN providers. While top-tier services generally offer robust Kill Switches, DNS leak protection, and IPv6 handling, many cheaper or less reputable VPNs might have buggy implementations or simply lack these features altogether. Some VPNs might advertise a Kill Switch, but it only works at an application level, leaving other system processes exposed, or it might fail to trigger under specific network conditions. This disparity highlights the importance of choosing a reputable VPN provider that not only offers these features but has a proven track record of effective implementation and regular security audits. Blindly trusting any VPN provider, especially those offering "free" services (which often come with their own privacy compromises, such as data logging or intrusive advertising), is an enormous risk. The illusion of privacy is particularly strong with these less scrupulous providers, who leverage the VPN hype while failing to deliver on fundamental security promises, often at the expense of their users' data.
The Dangers of a "Set It and Forget It" Mentality in Cybersecurity
The "set it and forget it" approach, while convenient, is antithetical to sound cybersecurity practices. The digital threat landscape is dynamic, with new vulnerabilities discovered daily and new methods of surveillance constantly evolving. What was once considered a secure default might become a glaring hole tomorrow. For instance, a few years ago, IPv6 leaks were less of a concern for the average user, as IPv6 adoption was lower. Today, with increasing IPv6 deployment, neglecting IPv6 leak protection is a significant oversight. Similarly, browser technologies like WebRTC are constantly updated, and what was once a secure implementation might introduce new bypasses in a later version. Relying on static configurations in such a fluid environment is akin to using an outdated antivirus program against modern malware; it offers a false sense of security while leaving you wide open to current threats. It is a terrifying thought, but one we must embrace to truly protect ourselves.
Statistical data consistently reinforces this problem. A hypothetical internal audit conducted by a prominent cybersecurity research firm (let's imagine "Digital Fortress Analytics" in 2023) found that among users who had been subscribed to a VPN for more than a year, less than 25% had actively checked or modified their VPN's security settings beyond the initial setup. This astonishing lack of engagement indicates a widespread over-reliance on default configurations and a fundamental misunderstanding of personal responsibility in digital security. The report further speculated that this complacency directly contributed to a higher incidence of reported IP leaks and privacy breaches among these long-term, passive users compared to those who regularly reviewed their settings. This isn't just about technical knowledge; it's about cultivating a mindset of continuous vigilance and proactive engagement with the tools designed to protect us. We can't simply outsource our privacy entirely to a piece of software.
"The only truly secure system is one that is powered off, locked in a safe, and buried 20 feet underground in a concrete bunker. Even then, I have my doubts." This quote, often attributed to various cybersecurity experts, humorously underscores the perpetual challenge of security. It highlights that absolute security is an elusive ideal, and therefore, continuous effort and vigilance are paramount, even with seemingly robust tools like VPNs.
This brings us to a crucial point about the importance of choosing a reputable VPN provider that genuinely prioritizes user security and privacy. A good VPN service doesn't just offer these critical settings; it makes them prominent, educates users on their importance, and ensures their robust and reliable implementation. They will undergo independent security audits, publish transparency reports, and actively address any discovered vulnerabilities. Conversely, a provider that hides these settings, offers vague explanations, or has a history of questionable privacy practices should be viewed with extreme caution. The illusion of privacy is often strongest with these less trustworthy services, as they leverage the marketing hype while failing to invest in the core technologies and user education necessary for true protection. Your choice of VPN provider, coupled with your proactive engagement with its settings, forms the bedrock of your online privacy, separating genuine security from a mere placebo effect.