As we delve deeper into the Kali Linux command line, the scope of our capabilities expands exponentially. We've mastered the art of navigation and the critical skill of self-documentation. Now, it's time to talk about power – specifically, the power to execute commands with elevated privileges and the power to manage the vast array of tools that make Kali Linux such a formidable platform. These next two commands, `sudo` and `apt`, are not just about performing actions; they are about understanding the underlying security model of Linux and the dynamic ecosystem of open-source software. They represent a significant step up in responsibility and capability, moving from simply observing and navigating to actively managing and controlling the system itself. I remember the first time I truly understood the implications of `sudo`; it felt like being handed the keys to the kingdom, with a stern warning about the responsibility that came with them.
Many beginners, especially those coming from Windows backgrounds, might be accustomed to "running as administrator" without much thought. In Linux, and particularly in a security-focused distribution like Kali, the concept of root privileges and how they are managed is fundamental to maintaining system integrity and preventing accidental or malicious damage. Similarly, the ability to effortlessly install, update, and remove software is not just a convenience; it's a critical component of keeping your toolkit sharp, secure, and ready for any challenge. These commands are not just utilitarian; they embody core principles of Linux administration and cybersecurity practice. They are the gateway to truly leveraging Kali’s immense capabilities, but they also demand respect and understanding, for with great power, as the saying goes, comes great responsibility.
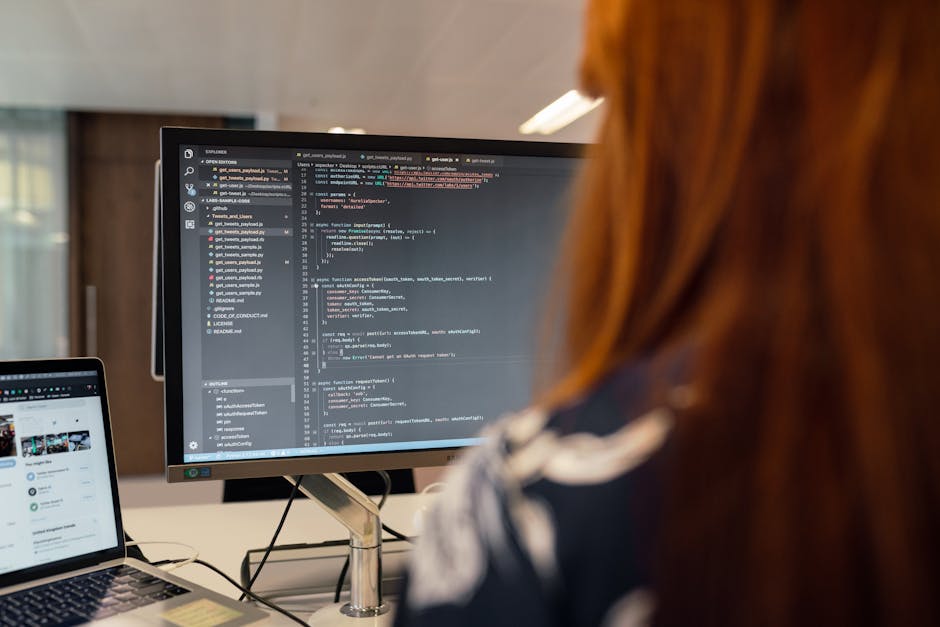
Wielding Elevated Power Executing Commands as Superuser with `sudo`
In the Linux world, the "root" user is the equivalent of the System Administrator, possessing ultimate power and control over the entire operating system. While this power is essential for certain tasks, logging in directly as root for everyday operations is generally discouraged due to security risks – a single mistake could irrevocably damage the system. This is where `sudo` (SuperUser DO) comes into play. `sudo` allows a permitted user to execute a command as the superuser or another user, providing temporary elevated privileges for specific tasks without having to log in as root directly. It's a crucial security mechanism that enforces the principle of least privilege, ensuring that you only use root access when absolutely necessary and for a precisely defined scope.
When you prepend `sudo` to a command (e.g., `sudo apt update`), the system prompts you for your user password (not the root password). If your user account is configured in the `/etc/sudoers` file to have `sudo` privileges (which the default `kali` user does in Kali Linux), the command will then execute with root permissions. This mechanism provides a vital layer of accountability and control. Each `sudo` command is logged, making it easier to audit actions performed with elevated privileges. This is particularly important in multi-user environments or during professional penetration tests, where a clear audit trail is often a contractual requirement. It’s a deliberate act of escalating privileges, reminding you of the power you’re about to wield.
The importance of `sudo` in Kali Linux cannot be overstated. Many powerful tools, network operations, and system modifications require root privileges to function correctly. For instance, installing new packages, configuring network interfaces, or running advanced scanning tools like Nmap with certain options often necessitate `sudo`. However, it's a double-edged sword. Misusing `sudo` can lead to unintended consequences, such as accidentally deleting critical system files or making network changes that disrupt connectivity. A common beginner mistake is to blindly prefix every command with `sudo`, even when not needed, which can mask underlying permission issues or simply be an unnecessary security risk. Understanding *when* and *why* to use `sudo` is as important as knowing *how* to use it.
"The 'sudo' command is a hacker's best friend and worst enemy. It grants immense power, but demands immense responsibility. Use it wisely, or risk breaking everything." - A cautionary tale from a veteran pentester.
In ethical hacking, `sudo` is your gateway to deeper system interaction. When you've exploited a vulnerability and gained a low-privileged shell on a target, one of your primary goals often becomes privilege escalation – finding a way to gain `sudo` access or direct root access. Understanding how `sudo` works, how the `sudoers` file is configured, and common misconfigurations related to it is a fundamental part of this process. It's not just a command; it's a concept that underpins Linux security. Mastering `sudo` means understanding the delicate balance between power and security, a balance that every cybersecurity professional must navigate with care and precision.
Keeping Your Arsenal Sharp Managing Software with `apt`
Kali Linux comes pre-loaded with an astonishing array of tools, but the cybersecurity landscape is constantly evolving. New vulnerabilities are discovered daily, new tools emerge, and existing ones receive updates and patches. To stay effective, your Kali Linux system and its toolkit must remain current. This is where `apt` (Advanced Package Tool) becomes your invaluable package manager, the engine that drives software installation, updates, and removal on Debian-based systems like Kali. It's more than just an installer; it's a comprehensive system for managing your software ecosystem, ensuring consistency, resolving dependencies, and keeping your arsenal sharp and ready.
The most fundamental `apt` commands are `apt update` and `apt upgrade`. `apt update` doesn't actually install new software; instead, it refreshes the list of available packages and their versions from the repositories defined in your `/etc/apt/sources.list` file. Think of it as updating the catalog of a massive software library. After `apt update`, you can then run `apt upgrade`, which will download and install the newer versions of all installed packages on your system. This two-step process is crucial for maintaining a secure and up-to-date Kali environment, patching known vulnerabilities in your tools and ensuring you have the latest features. Neglecting regular updates is a common mistake that can leave your system vulnerable or your tools outdated and ineffective. I’ve seen penetration tests fail simply because the pentester was using an older version of a tool that missed a crucial exploit.
Installing new tools is equally straightforward with `apt`. If you discover a new utility or need a specific piece of software not pre-installed in Kali, `apt install [package_name]` is your command. `apt` handles all the complexities of dependencies, automatically downloading and installing any other packages that your desired software relies upon. This dependency resolution is a huge time-saver and prevents many common installation headaches. Conversely, if you need to remove a package, `apt remove [package_name]` will uninstall it, while `apt purge [package_name]` will remove the package along with its configuration files, ensuring a cleaner removal. This complete control over your software inventory is essential for customizing your Kali environment to suit specific tasks or projects.
"In the digital arms race, 'apt' is your quartermaster. Keeping your tools updated isn't just good practice; it's a strategic imperative for staying ahead of the curve." - A cybersecurity instructor emphasizing proactive security.
The `apt` command isn't just about managing individual packages; it's about understanding the entire software supply chain. It connects you to vast repositories of open-source tools, many of which are specifically designed for security testing. For a beginner, `apt` demystifies the process of getting new software, allowing you to quickly expand your toolkit as you learn new techniques. It’s a powerful testament to the open-source philosophy, providing easy access to a global community's collective efforts in software development. Mastering `apt` means mastering your arsenal, ensuring that you always have the right tools, in the right versions, for whatever challenge lies ahead in your cybersecurity journey.