Having established the foundational pillars of password strength – the paramount importance of length, the strategic inclusion of diverse character types, and the crucial role of true randomness – we now pivot to explore a more human-friendly, yet equally robust, approach: the passphrase. This strategy represents a significant evolution in password philosophy, moving away from the often-frustrating requirement of memorizing seemingly arbitrary strings of characters and towards a method that leverages our natural linguistic abilities. It’s a recognition that while true randomness is ideal, human beings still need a way to interact with and, in some cases, recall their master keys. This section will delve into the profound advantages of passphrases, explain why they offer a superior balance of security and usability compared to traditional passwords, and crucially, highlight the common pitfalls to avoid when crafting these extended verbal shields. We'll also underscore the non-negotiable principle of using a unique identifier for every single online service, an essential layer of defense that complements any strong password strategy.
The journey from a short, complex password to a long, memorable passphrase is not just a stylistic change; it's a paradigm shift in how we approach digital security. It acknowledges that the weakest link in any security chain is often the human element, and by designing systems that work *with* human nature rather than against it, we can achieve significantly better outcomes. The passphrase revolution isn't about making things easier at the expense of security; it's about making security *more accessible* and *more sustainable* for the average user. It's about empowering individuals to create credentials that are both incredibly difficult for machines to crack and surprisingly simple for a human to recall, albeit with careful construction. This approach allows us to achieve the desired length for maximum entropy without resorting to the brain-bending gymnastics required to memorize a truly random string of symbols. So, let’s unlock the potential of words and phrases as our most formidable digital guardians, understanding how to harness their power effectively while sidestepping the common traps that can still render them vulnerable.
Embracing the Passphrase Revolution A More Secure and Manageable Approach
The concept of a passphrase has emerged as a powerful counter-narrative to the traditional password paradigm, offering a compelling blend of robust security and human memorability. Instead of a single, short, convoluted string of characters, a passphrase consists of multiple, often unrelated, words strung together, potentially with some minor modifications. The genius of the passphrase lies in its ability to achieve immense length, and thus formidable entropy, without requiring the user to memorize an arbitrary jumble of symbols. A passphrase like "correct horse battery staple," famously popularized by an XKCD comic, might seem simple, but its 28 characters make it astronomically more difficult to crack via brute force than an 8-character password like "P@$$w0rd!", even with all its forced complexity. The sheer length of the passphrase dramatically increases the number of possible combinations, pushing the time required for a brute-force attack into the realm of geological epochs, even for the most powerful supercomputers.
The primary advantage of passphrases is their capacity to combine high entropy with relative memorability. While a truly random string like `Fq&7*mPj@c9#Xz4!rLw` is virtually impossible for a human to commit to memory, a sequence of four or five common, unrelated words can often be remembered with relative ease. The trick here is the *unrelatedness* of the words. A phrase like "The quick brown fox jumps over the lazy dog" is too common and would be easily cracked by dictionary attacks that incorporate common idioms and literary phrases. However, "purple elephant toaster cloud" is a string of words that are individually common but collectively nonsensical, making them much harder for an attacker to guess using a dictionary or common phrase list. This approach leverages the human brain's capacity for semantic memory – remembering concepts and ideas – rather than its weakness for rote memorization of arbitrary symbols. It’s a clever hack that makes strong security genuinely achievable for the average user, without the mental gymnastics traditionally associated with complex passwords.
Beyond simple word concatenation, passphrases can be further strengthened by judiciously incorporating numbers, symbols, and varied capitalization, much like traditional passwords. However, the key here is *judiciously* and *randomly*. Instead of predictable substitutions, consider inserting a number or symbol in an unexpected place, or capitalizing a letter in the middle of a word rather than just the first letter of each word. For example, "purple elephant toaster cloud" could become "PuRp1e_ELeph@nt_Toa5ter-Cl0ud!" This level of modification, while adding complexity, still retains a degree of memorability because the underlying word structure is preserved. The beauty of this method is that it allows for a flexible approach to security, where users can dial up the complexity as needed for their most critical accounts, while still enjoying the benefits of length and relative ease of recall. It’s a significant step forward in making robust password practices not just a technical aspiration, but a practical reality for everyone navigating the digital landscape.
Dodging the Dictionary Bullet The Peril of Predictable Word Combinations
While passphrases offer immense security benefits due to their length, they are not entirely immune to attack, especially if constructed carelessly. The primary vulnerability lies in dictionary attacks, which, as the name suggests, involve an attacker trying every word, phrase, and combination of words found in vast linguistic databases. These databases go far beyond simple English dictionaries; they include common idioms, movie quotes, song lyrics, famous speeches, literary passages, and even compilations of billions of passwords leaked from previous data breaches. If your passphrase consists of words that are commonly found together or are part of well-known cultural references, you might inadvertently be handing the keys to your digital kingdom to an attacker. A passphrase like "may the force be with you" might seem long and complex, but it would be among the first combinations tried by a sophisticated dictionary attack, given its widespread recognition.
The critical distinction for a secure passphrase is the *randomness and unrelatedness* of the chosen words. Imagine picking four or five words completely at random from a dictionary, without any logical connection or semantic relationship. "Banana stapler purple cloud galaxy" is a perfect example. Individually, each word is common. Collectively, they form a nonsensical, unpredictable sequence. This unpredictability is what makes it resistant to dictionary attacks. Attackers' algorithms are incredibly efficient at testing common word sequences and permutations, but they struggle immensely when faced with truly arbitrary combinations. The space of possible four-word combinations from a large dictionary is so vast that even with immense computing power, trying every single one becomes an infeasible task within a human lifetime, especially if the words are not commonly associated with each other.
To further fortify your passphrases against these sophisticated dictionary and pattern-matching attacks, consider adding elements of "salt" and "pepper" to your word salad. This means introducing numbers, symbols, and mixed capitalization in non-obvious ways, as discussed previously. Instead of simply appending a number or symbol to the end, try inserting them randomly within or between words. For example, "banana stapler purple cloud galaxy" could become "B@nanaSt@plerPurp1eCloudG@laxy!" or "banana!stapler@purple#cloud$galaxy%". The key is to avoid predictable patterns. The more unexpected and seemingly chaotic your modifications, the harder it becomes for an attacker to guess your specific combination. This strategy ensures that your passphrase not only benefits from its impressive length but also from a layer of unique, human-generated complexity that defies automated pattern recognition, pushing it into the realm of truly formidable digital keys.
The Unique Identity Principle Never Reuse Your Digital Keys
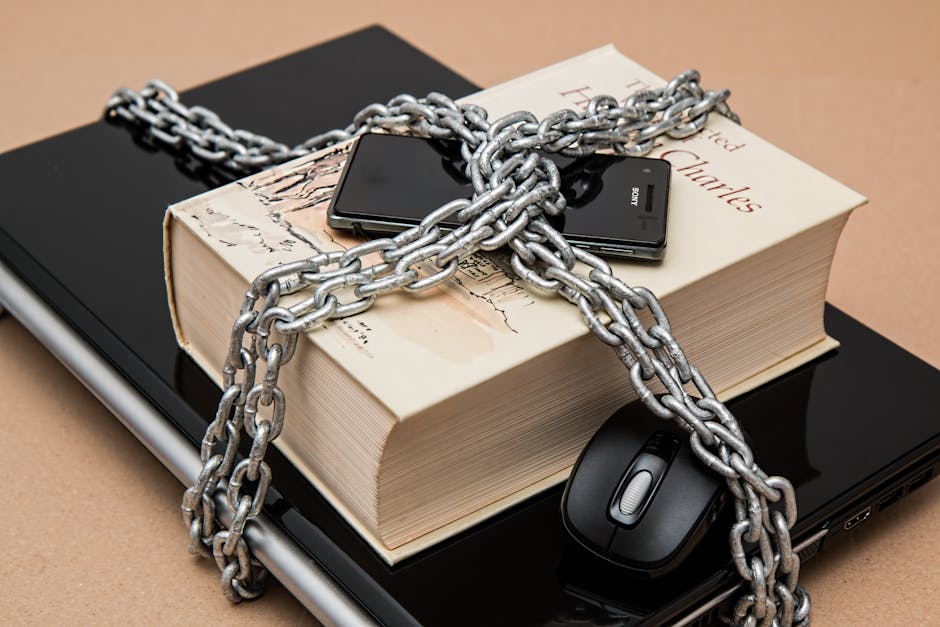
If there's one golden rule in cybersecurity that is absolutely non-negotiable, it is this: never, ever reuse passwords across different online accounts. This isn't merely a suggestion; it's a fundamental principle, the violation of which accounts for a staggering percentage of successful cyberattacks. Imagine having one physical key that opens your front door, your car, your safe deposit box, and your office. If a thief gets hold of that one key, your entire life is compromised. The digital world operates on precisely the same principle. Even if you meticulously craft an incredibly long, complex, and random password for your email, its strength is completely nullified if you use that exact same password for a less secure forum, an obscure online game, or a defunct social media site that subsequently suffers a data breach.
This vulnerability is exploited through a pervasive attack vector known as "credential stuffing." Here’s how it works: Cybercriminals amass vast databases of usernames and passwords, often hundreds of millions or even billions of entries, collected from countless data breaches around the globe. Instead of trying to crack your specific password, they take these leaked credentials and "stuff" them into login forms on popular, high-value websites like banking portals, major email providers, and social media platforms. If you've reused your password, even if it was a strong one for the breached site, it will work on these other services. This is a low-effort, high-reward strategy for attackers, as it bypasses the need for complex cracking and relies solely on human complacency and password reuse. The average success rate for credential stuffing attacks can be surprisingly high, turning one minor breach into a cascading nightmare for the affected individual, leading to account takeovers, financial fraud, and identity theft across their entire digital footprint.
"Password reuse is the digital equivalent of leaving a single master key under your doormat, hoping no one finds it. When a breach occurs, that doormat is lifted for everyone to see." - Troy Hunt, Creator of Have I Been Pwned
The consequences of password reuse are not theoretical; they are devastatingly real, as countless case studies attest. We've seen instances where a breach at a relatively obscure service like a food delivery app led to the compromise of a user's primary email, which then allowed attackers to reset passwords for their banking, investment, and social media accounts. The chain reaction is swift and brutal, often before the victim even realizes their initial, seemingly minor, account was compromised. This "one breach to rule them all" scenario highlights why every single account must have a unique, strong password. It acts as a firewall, containing any potential breach to just that single service, preventing the attacker from gaining access to your entire digital life. Managing hundreds of unique, strong passwords manually is an impossible task for any human, which is precisely why the next section will delve into the indispensable tools that make this critical security practice not just feasible, but effortless: password managers.