We’ve meticulously dissected the theoretical underpinnings of robust password creation, understanding the paramount importance of length, the strategic role of complexity, the necessity of true randomness, and the non-negotiable principle of uniqueness. However, theoretical knowledge, no matter how profound, is only half the battle. In the real world, managing dozens, if not hundreds, of unique, long, complex, and random passwords for every online service is an insurmountable task for the human mind. This is where technology steps in, not as a replacement for good password hygiene, but as an indispensable enabler, transforming best practices from an arduous chore into a seamless, almost invisible layer of protection. This segment of our deep dive will focus on the unsung heroes of modern cybersecurity: password managers and two-factor authentication (2FA). These aren't just convenient tools; they are fundamental components of any truly robust digital defense strategy, acting as both the secure vault for your digital keys and the impenetrable second lock on your most critical accounts. Ignoring them in today's threat landscape is akin to building a magnificent fortress but leaving the drawbridge permanently down.
The beauty of these tools lies in their ability to automate the most challenging aspects of password security, freeing us from the cognitive burden of remembering complex strings while simultaneously elevating our protection to levels unattainable through manual effort alone. A password manager, at its core, is a highly encrypted digital vault that stores all your unique, randomly generated passwords, accessible only by a single, incredibly strong master password or passphrase. It’s the central nervous system of your digital security. Two-factor authentication, on the other hand, adds a crucial second layer of verification, ensuring that even if an attacker somehow bypasses your password, they still cannot gain access without possessing a physical device or biometric attribute that only you control. Together, these two technologies form a formidable barrier, making your digital life significantly more resilient against a vast array of cyber threats. We'll explore their inner workings, discuss their diverse forms, and highlight why their implementation is not just recommended, but absolutely essential for anyone serious about protecting their online identity and assets.
Your Digital Vault The Indispensable Role of Password Managers
Imagine a world where you never have to remember a single password again, yet every one of your online accounts is protected by a unique, cryptographically strong, and utterly random string of 20+ characters. This isn't a futuristic dream; it's the reality offered by a reputable password manager. At its heart, a password manager is a highly encrypted database that securely stores all your login credentials, sensitive notes, and other digital secrets. It's protected by a single, master password (or passphrase) that only you know. This master key is the only thing you need to remember, and its strength is paramount, as it guards the entire vault. Once unlocked, the manager can automatically fill in your usernames and passwords on websites and applications, generate new strong passwords on demand, and even audit your existing passwords for weaknesses or reuse. It transforms the impossible task of managing hundreds of unique, complex passwords into an effortless, secure routine.
The benefits of adopting a password manager are multifaceted and profound. Firstly, it enables true uniqueness for every account. No more reusing "MyFavoritePet1!" across your bank, email, and social media. The password manager generates a fresh, random, and strong password for each new service you sign up for, storing it instantly. Secondly, it drastically improves password strength. These generators are designed to produce strings with maximum entropy, incorporating a balanced mix of uppercase, lowercase, numbers, and symbols in a truly unpredictable fashion, often exceeding the 20-character mark with ease. Thirdly, it mitigates phishing risks; since the password manager typically auto-fills credentials only on legitimate, recognized websites, it helps prevent you from accidentally typing your login details into a fake, malicious site. This subtle but powerful feature acts as an additional layer of defense against sophisticated social engineering attacks that try to trick you into revealing your secrets.
Choosing the right password manager is a crucial decision, as you're entrusting it with the keys to your entire digital life. Popular and well-regarded options include LastPass, 1Password, Bitwarden, and KeePass. Each has its own set of features, pricing models (some offer free tiers), and approaches to security, but all reputable options employ robust encryption (like AES-256) to protect your data. When considering a password manager, look for features like cross-device synchronization, built-in password auditing (to identify weak or reused passwords), secure sharing capabilities (for family or team use), and, critically, support for two-factor authentication for the manager itself. While the initial setup and migration of existing passwords can seem daunting, the long-term peace of mind and enhanced security it provides are invaluable. The question isn't whether you *should* use a password manager, but rather, *which one* you'll choose to finally take control of your digital security landscape.
The Second Shield Why Two-Factor Authentication is Non-Negotiable
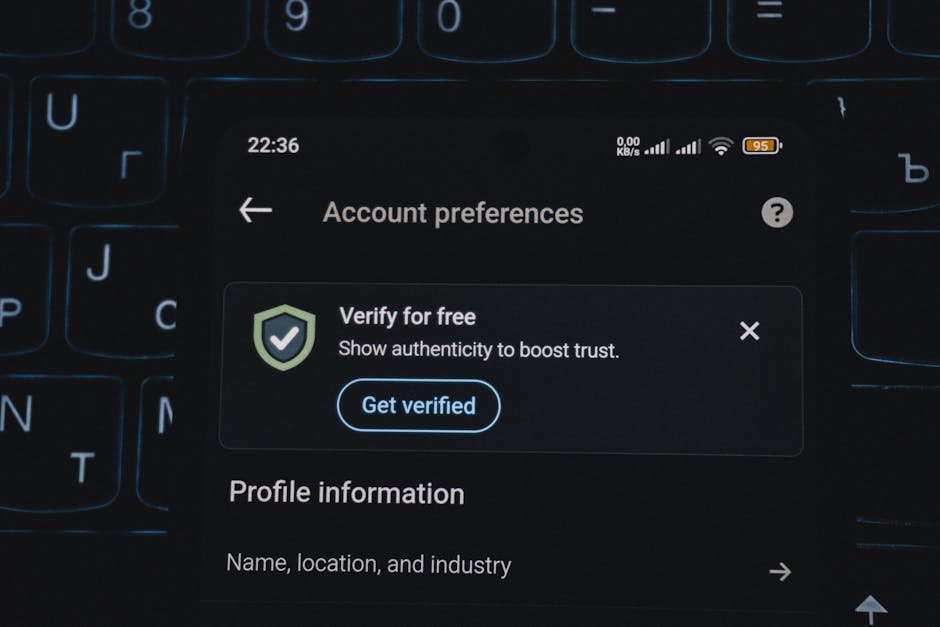
Even the strongest password, generated by a manager and unique to every site, can theoretically be compromised. Perhaps through a sophisticated zero-day attack on a service, a highly targeted phishing attempt that bypasses your vigilance, or even a rare instance of malware on your device. This is where two-factor authentication (2FA), also known as multi-factor authentication (MFA), steps in as the non-negotiable second shield. 2FA adds a crucial layer of security by requiring a second piece of evidence, beyond just your password, to verify your identity. It's based on the principle of requiring "something you know" (your password) combined with "something you have" (a physical device like your phone or a hardware key) or "something you are" (a biometric like a fingerprint or face scan). Even if an attacker somehow obtains your password, they still cannot access your account without that second factor, effectively rendering a stolen password useless.
Different types of 2FA offer varying degrees of security. The most common, and perhaps least secure, is SMS-based 2FA, where a code is sent to your registered phone number. While better than no 2FA, SMS is vulnerable to "SIM swapping" attacks, where criminals trick mobile carriers into transferring your phone number to their control, allowing them to receive your 2FA codes. A significantly more secure option is using an authenticator app (like Google Authenticator, Microsoft Authenticator, or Authy), which generates time-based one-time passwords (TOTP) directly on your device. These codes are generated locally and don't rely on cellular networks, making them immune to SIM swapping. The gold standard for 2FA, however, comes in the form of hardware security keys, such as YubiKey or Google Titan. These physical devices plug into your computer or connect wirelessly and use cryptographic protocols (like FIDO U2F/WebAuthn) to verify your identity, making them virtually impervious to phishing and sophisticated remote attacks. They are the most robust form of 2FA available to the average consumer.
The impact of 2FA cannot be overstated. Consider a scenario where a major social media platform suffers a data breach, and your email and password are leaked. If you have 2FA enabled, even though your password is now public, the attacker still cannot log into your account because they don't possess your phone or hardware key to generate the second code. This simple, yet incredibly powerful, mechanism has prevented countless account takeovers and financial frauds. Many tech giants, including Google, actively promote and even enforce 2FA because they understand its critical importance. Enabling 2FA on your most sensitive accounts – your primary email, banking, social media, and, crucially, your password manager – is perhaps the single most impactful step you can take to elevate your digital security beyond just a strong password. It's the ultimate fail-safe, the second line of defense that transforms a potential disaster into a minor inconvenience, ensuring that your digital fortress remains impenetrable even if one of your keys falls into the wrong hands.
Beyond the Obvious Other Layers of Digital Defense
While strong passwords and 2FA form the bedrock of personal cybersecurity, a truly comprehensive defense strategy extends beyond these core elements, encompassing a broader range of digital hygiene practices. One often-overlooked area is the security of your "security questions." These seemingly innocuous prompts ("What was your mother's maiden name?", "What was the name of your first pet?") are often treated casually, yet they can be the weakest link in an otherwise strong security chain. The problem is that answers to many common security questions are often publicly available through social media, public records, or simple deduction. Instead of providing truthful answers, treat your security questions as additional passwords. Use unique, random strings of characters or completely unrelated, memorable phrases that only you would know, and ideally, store these answers in your password manager. For example, if asked "What was the name of your first pet?", you might enter "PurpleCloudBanana!" rather than "Fido."
Another critical, yet frequently underestimated, aspect of digital defense is the security of your recovery email address. Your primary email account often serves as the master key to your entire digital life, capable of resetting passwords for almost every other service you use. If an attacker gains access to your email, they can effectively take over all your connected accounts. Therefore, it is absolutely paramount to secure your primary email with the strongest possible password and, crucially, with the most robust form of 2FA available (ideally a hardware security key or authenticator app). Regularly review your email’s recovery options, ensuring that any linked phone numbers or secondary email addresses are current and also highly secured. Think of your email as the control panel for your digital identity; its compromise is often the precursor to a full-scale digital disaster, making its protection a top priority.
Finally, maintaining robust device security and cultivating a healthy skepticism toward online interactions are vital, ongoing practices. Keeping your operating system, web browsers, and all software applications updated to the latest versions is essential, as these updates often include critical security patches that fix vulnerabilities exploited by attackers. A strong device password or PIN, coupled with biometric authentication (like fingerprint or facial recognition) for your phone and computer, adds another layer of local protection. Beyond the technical, developing a keen awareness of phishing tactics, suspicious links, and unsolicited communications is perhaps the most powerful defense against social engineering. Remember, the human element is often the weakest link in any security system. By combining strong technical measures with ongoing vigilance and critical thinking, we can build a comprehensive digital defense that stands resilient against the ever-evolving landscape of cyber threats, ensuring our online lives remain secure and private.