Have you ever felt that unsettling prickle, the sensation of unseen eyes tracking your every move online? It’s not paranoia; it's the stark reality of our hyper-connected world. Every click, every search, every purchase leaves an indelible mark, a digital breadcrumb trail leading straight back to you. We navigate the internet under the illusion of anonymity, blissfully unaware that we are, in fact, walking billboards, our most intimate details harvested, analyzed, and traded by an invisible industry. This isn't just about targeted ads for that pair of shoes you briefly glanced at; it’s about a profound erosion of personal privacy, a systematic dismantling of our right to simply exist without constant scrutiny. The very fabric of our digital lives is woven with threads of surveillance, spun by corporations, governments, and malicious actors alike, transforming our online experience into a transparent exhibition.
For too long, we’ve accepted this as the unavoidable cost of convenience, a necessary evil in an increasingly digital landscape. But what if there was another way? What if you could reclaim your digital sovereignty, pulling back the veil of visibility and truly vanishing from the prying eyes that monetize your existence? Imagine browsing, communicating, and transacting online with the quiet confidence that your identity, your location, and your preferences remain yours alone. This isn't about becoming a ghost in the machine in some dramatic, cloak-and-dagger sense; it's about making conscious, informed choices to protect your privacy, to minimize your digital footprint, and to take back control from the pervasive surveillance economy. It’s about building a fortress around your online self, not just a flimsy fence, and understanding the tools and strategies that empower you to do so.
The Invisible Chains We Wear Understanding Our Digital Imprint
Our digital footprint is not a single, static entity; it’s a sprawling, dynamic network of data points that collectively paint an incredibly detailed picture of who we are. From the moment we first signed up for an email account or a social media profile, we began contributing to this ever-growing dossier. Every website visit logs our IP address, browser type, and often, our geographic location. Cookies, those seemingly innocuous bits of data, follow us across the web, remembering our preferences but also serving as powerful tracking beacons for advertisers. Beyond that, sophisticated techniques like browser fingerprinting can uniquely identify your device based on its specific configuration, installed fonts, and even screen resolution, making it incredibly difficult to truly hide, even when you think you're being careful. This constant data collection isn’t just for showing you relevant ads; it builds profiles that can influence everything from your loan applications to your eligibility for certain services, often without your explicit knowledge or consent.
The sheer scale of this data collection is staggering. Data brokers, a multi-billion dollar industry, exist solely to aggregate, analyze, and sell our personal information. They meticulously piece together fragments from public records, social media, online purchases, and even offline activities, creating comprehensive profiles that include your age, income, political leanings, health conditions, and even your probable interests. These profiles are then sold to marketers, political campaigns, insurance companies, and even government agencies, creating an intricate web of information exchange where your privacy is the ultimate commodity. It’s a relentless, automated process that operates largely in the shadows, leaving most internet users completely unaware of the extent to which their lives are being cataloged and commodified. The consequences range from merely annoying spam to more insidious forms of manipulation and discrimination, making the need to understand and mitigate this exposure more urgent than ever before.
The Illusion of Online Anonymity
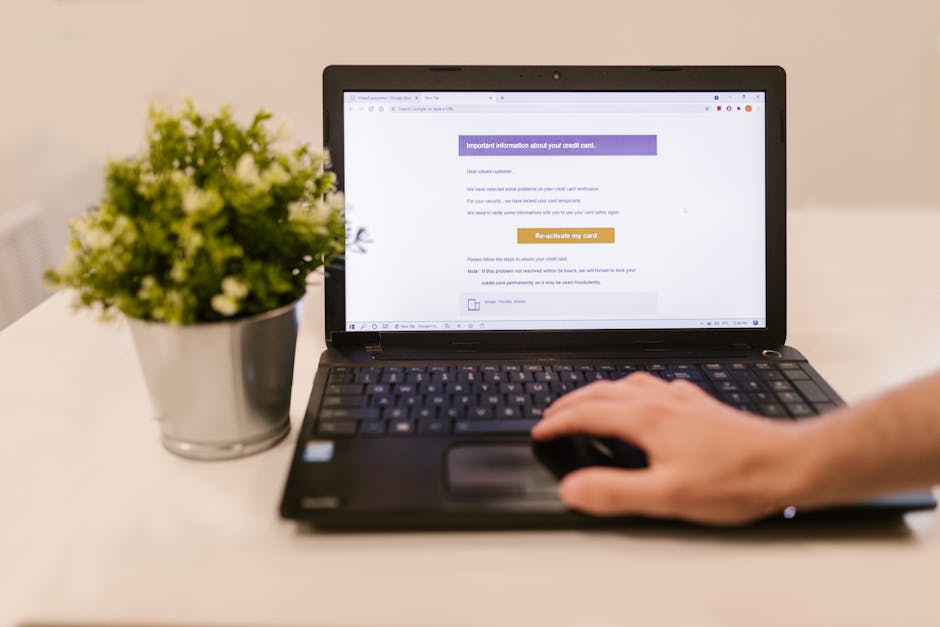
Many believe that simply using "incognito mode" or "private browsing" offers a shield against surveillance. While these modes prevent your browser from saving your local browsing history, cookies, and site data, they offer a false sense of security regarding true anonymity. Your internet service provider (ISP) can still see every website you visit, every search query you make, and every piece of data you send or receive. The websites themselves still record your IP address, and third-party trackers embedded on those sites continue to collect information about your browsing habits. It's akin to closing your blinds but leaving your front door wide open; you might feel a bit more private, but the outside world can still clearly see you walking through your living room. The fundamental mechanisms of internet identification remain active, making incognito mode largely ineffective against sophisticated tracking and surveillance.
Even more concerning is the increasing sophistication of tracking technologies that go far beyond simple cookies. Cross-device tracking, for instance, allows companies to link your activity across your smartphone, tablet, and desktop computer, creating a unified profile regardless of which device you're using. This is often achieved through shared login credentials, unique device identifiers, or even probabilistic matching based on your browsing patterns and IP addresses. The goal is always the same: to create a complete, 360-degree view of your digital life. This pervasive data collection means that even if you take steps to clear cookies on one device, your online persona can still be stitched together through other identifiers. The battle for online privacy isn't just about individual websites; it's about understanding and dismantling the entire ecosystem of digital surveillance that has become deeply embedded in the internet's infrastructure, requiring a multi-layered, proactive approach to truly vanish from its grasp.
The journey to digital disappearance isn't a single, magical act; it's a deliberate, multi-faceted strategy that combines technological tools with a fundamental shift in mindset. It demands vigilance, patience, and a willingness to adapt your online habits. But the payoff is immense: the peace of mind that comes from knowing your personal information isn't constantly being harvested, the freedom to explore the internet without fear of judgment or manipulation, and the profound satisfaction of reclaiming your digital self. This guide will walk you through five essential steps, offering a practical roadmap to achieve a level of online privacy and anonymity that many believe is simply unattainable. We'll delve into the nuances of each step, providing not just what to do, but why it's crucial, empowering you to make informed decisions on your path to becoming a ghost in the machine, visible only when you choose to be.