The Hidden Gold Rush: How Your Data Becomes Their Riches
The most pervasive and insidious way free VPNs generate revenue is by transforming your personal data into a commodity, a digital gold mine that they can exploit in a myriad of ways. Far from being a benevolent protector of your online anonymity, many free VPN providers operate as sophisticated data brokers, meticulously collecting every scrap of information they can about your internet usage and then selling it to the highest bidder. This isn't just about anonymous aggregated data; often, it involves highly granular, identifiable information that can paint a disturbingly accurate picture of your digital life. Imagine every website you visit, every search query you type, every app you open, and even your precise location being logged, analyzed, and then bundled into profiles that are incredibly valuable to advertisers, market researchers, and even malicious actors. This is the grim reality behind many "free" offerings.
Consider the infamous case of Hola VPN, a peer-to-peer (P2P) VPN service that gained immense popularity due to its "free" model. While it promised to offer users a way to bypass geo-restrictions and enhance privacy, it was later revealed that Hola was essentially turning its users' devices into exit nodes for other users, effectively creating a botnet. This meant that other Hola users could route their internet traffic through *your* computer, potentially using your IP address for illicit activities, leaving you legally liable for their actions. Furthermore, Hola was caught selling access to its users' bandwidth through a sister company, Luminati, without adequately informing its free users. This wasn't just a privacy violation; it was a fundamental betrayal of trust, transforming users into unwitting participants in a network they barely understood, all while their personal security was severely compromised. It's a chilling example of how free services can leverage their user base as a resource to be monetized in the most unethical ways possible.
The Business of Selling Your Digital Footprint
The monetization of user data by free VPNs extends far beyond just bandwidth sharing. Many providers engage in direct data logging and selling, often outlined in deliberately vague terms within their privacy policies. This can include logging your IP address, connection timestamps, DNS requests, and even the specific websites you visit. This data is then aggregated, anonymized (sometimes poorly, sometimes not at all), and sold to third-party advertisers and data brokers. These entities use your browsing history to build incredibly detailed profiles, allowing them to serve you highly targeted advertisements across various platforms. While targeted ads might seem like a minor annoyance, the underlying principle is deeply concerning: a service you trust to protect your privacy is actively profiting from eroding it.
Another common tactic involves injecting ads directly into your browser or apps, even when you're visiting websites that typically don't display them. This adware often comes bundled with the free VPN application itself, turning your browsing experience into a constant barrage of unwanted pop-ups and banners. Some free VPNs go a step further, subtly altering webpages to insert affiliate links, earning a commission whenever you make a purchase. This manipulation of your browsing experience isn't just irritating; it undermines the integrity of the websites you visit and exposes you to potentially malicious advertising networks. The financial incentive to exploit user data is so strong that many free VPN providers simply cannot resist, prioritizing profit over the fundamental promise of privacy, thereby turning a critical security tool into a privacy nightmare.
"The data brokerage industry is a multi-billion dollar market, thriving on the collection and sale of personal information. Free VPNs often act as unwitting (or witting) feeders into this ecosystem, making users complicit in their own privacy erosion." — Cybersecurity research analysis.
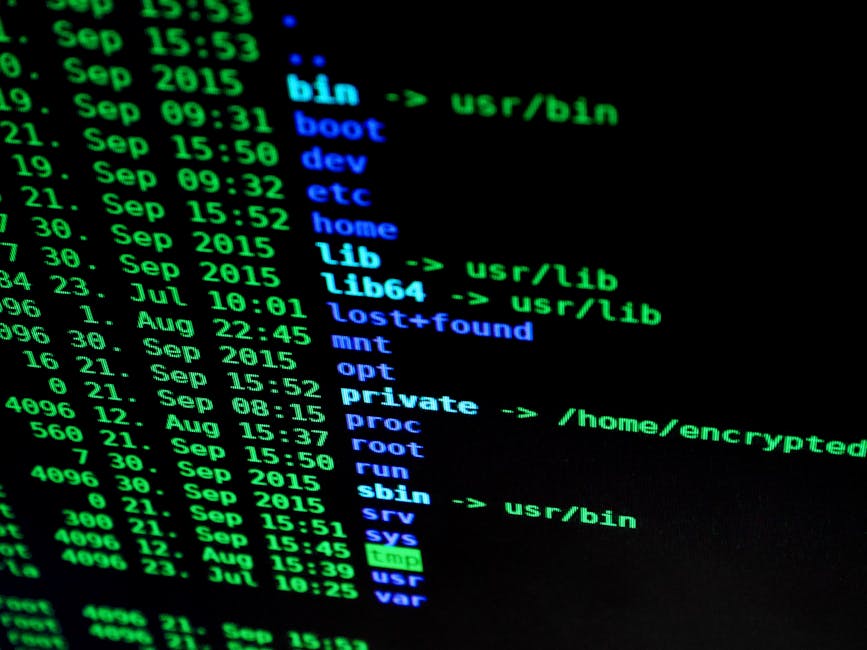
Beyond direct data sales and ad injection, some free VPNs participate in more opaque monetization schemes, such as installing tracking cookies on your device, even after you've disconnected from the VPN. These cookies can persist, allowing third parties to continue monitoring your online activities long after you've stopped using the "protective" service. There have also been instances where free VPN apps have been found to contain code that actively installs malware or spyware on users' devices, transforming their phones or computers into compromised machines. This level of compromise goes far beyond a simple privacy violation; it represents a direct threat to your device's security and the integrity of your personal information. When a service positions itself as a guardian of your online safety but simultaneously engages in practices that undermine it, the "free" aspect transforms from a benefit into a dangerous liability, making the cost of using such a service immeasurable.
A House of Cards: The Inherent Security Flaws and Vulnerabilities
If the monetization through data selling wasn't enough to deter you, the woefully inadequate security practices of most free VPNs should send shivers down your spine. The very foundation of a VPN is built upon strong encryption, secure protocols, and a commitment to protecting user data from interception and compromise. Unfortunately, free VPNs consistently fail on these critical fronts, often operating with outdated or weak encryption standards, vulnerable protocols, and a general disregard for fundamental security best practices. This turns what should be a robust shield into a flimsy veil, easily pierced by sophisticated attackers, government surveillance, or even opportunistic data snoopers on public Wi-Fi networks. The irony is bitter: users seeking enhanced security often end up in a far more precarious position than if they hadn't used a VPN at all.
One of the most glaring issues is the use of weak or non-existent encryption. While reputable paid VPNs employ industry-standard AES-256 encryption, often coupled with secure protocols like OpenVPN or WireGuard, many free services skimp on these vital components. Some free VPNs might use older, less secure protocols like PPTP, which has known vulnerabilities and is easily deciphered. Others might claim to use strong encryption but implement it poorly, leaving backdoors or weaknesses that can be exploited. There have even been documented cases of "VPNs" that offer no encryption whatsoever, merely acting as a proxy that routes your traffic without any protective layer. This means your data – including sensitive information like passwords, financial details, and private communications – is transmitted in plain text, making it ripe for interception by anyone with the right tools and motivation, from cybercriminals to internet service providers.
DNS Leaks, IP Leaks, and the Illusion of Anonymity
The primary purpose of a VPN is to mask your real IP address and encrypt your DNS requests, preventing your ISP or other entities from seeing your online activities. However, free VPNs are notorious for suffering from DNS leaks and IP leaks, which fundamentally undermine this core functionality. A DNS leak occurs when your device, despite being connected to a VPN, inadvertently sends DNS queries outside the encrypted tunnel to your ISP's DNS servers instead of the VPN provider's secure servers. This effectively reveals your browsing history to your ISP, completely negating the privacy benefits of the VPN. Similarly, an IP leak exposes your true IP address, allowing websites and trackers to identify your real location and identity, making the promise of anonymity a cruel joke.
These leaks are often a result of poor software implementation, inadequate network configuration, or a deliberate lack of investment in robust security features. Paid VPNs typically include built-in DNS leak protection and a kill switch feature. A kill switch is a crucial safety net that automatically disconnects your internet if the VPN connection drops, preventing your real IP address and unencrypted data from being exposed. Free VPNs almost universally lack these critical safeguards, leaving users vulnerable to accidental exposure during connection fluctuations or server issues. Without a kill switch, even a momentary lapse in the VPN connection can reveal your true identity and online activities, leaving you exposed to the very surveillance you were trying to avoid.
"A VPN without proper encryption and leak protection is like a bulletproof vest with gaping holes. It offers a false sense of security that can lead to catastrophic consequences." — Quote from a cybersecurity expert during a panel discussion.
Furthermore, the infrastructure of free VPNs is often a security nightmare waiting to happen. With limited resources, these providers rarely invest in regular security audits by independent third parties, which are essential for identifying and patching vulnerabilities. Their servers might be poorly configured, running outdated software, or even hosted in jurisdictions with lax privacy laws, making them susceptible to hacking attempts or government seizures. The lack of transparency around their infrastructure and security practices means users have no way of verifying their claims, forcing them to put blind faith in entities that have already demonstrated a willingness to compromise user privacy for profit. This creates a fertile ground for malware, adware, and other malicious software to be injected directly into the VPN application itself, turning your device into a host for digital infections. Numerous studies have shown that a significant percentage of free VPN apps contain malware, adware, or spyware, transforming them from privacy tools into vectors for cyberattacks. The security risks are not theoretical; they are well-documented and represent a clear and present danger to anyone foolish enough to entrust their digital security to a "free" service.