Having explored the psychological underpinnings and the sheer scale of the "invisible hack," it's time to pull back the curtain further and examine precisely how these master manipulators operate. This isn't about random luck; it's about meticulous planning, deep research, and a profound understanding of human behavior. The attackers aren't just sending out generic spam anymore; they're crafting bespoke digital weapons designed to exploit specific individuals within specific contexts. It’s an art form of digital deception, honed over years, constantly evolving with new technologies and new insights into what makes us tick. They understand that the most effective disguise is not one that stands out, but one that blends in so perfectly it becomes indistinguishable from the genuine article, leveraging our inherent trust in familiar patterns and figures of authority.
The journey from initial reconnaissance to a successful compromise is often a long and patient one for these threat actors. They don't rush; they observe. They gather fragments of information from every available public source, piecing together a comprehensive profile of their targets. This isn't just about finding an email address; it’s about understanding the organizational hierarchy, identifying key decision-makers, learning about ongoing projects, understanding payment processes, and even discerning personal habits or relationships. This wealth of detail allows them to create a narrative that is not only believable but also deeply resonant with the recipient's daily reality, making the malicious intent virtually undetectable. It’s a game of psychological chess, where every move is calculated to elicit a desired, often disastrous, response.
The Art of Digital Deception Crafting the Perfect Trap
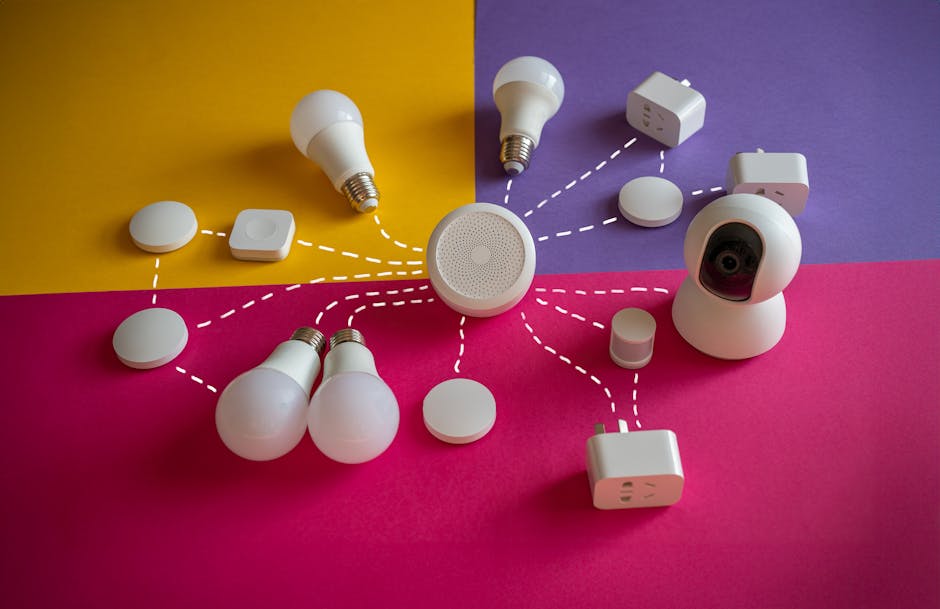
The foundation of any successful "invisible hack" lies in the attacker's ability to craft a narrative that resonates deeply with the target's specific circumstances. This isn't about a generic email promising millions from a Nigerian prince; it’s about an email that appears to come from your CFO, asking for an urgent wire transfer related to a critical, ongoing acquisition that you know about. It’s about a text message from your child’s school, referencing a specific event or teacher, and asking you to update payment information through a provided link. The meticulous detail in these attacks is what makes them so terrifyingly effective. Attackers invest significant time in open-source intelligence (OSINT) gathering, scouring corporate websites, social media profiles (LinkedIn, Facebook, X), news articles, and even public records to build a comprehensive dossier on their targets.
This reconnaissance phase is crucial. They might identify key personnel, understand reporting structures, learn about current projects, upcoming events, or even recent company news. For example, if a company has just announced a major merger or acquisition, attackers will leverage this information to create highly believable scenarios involving urgent financial transactions or data transfers related to the deal. They'll study email signature blocks, company letterheads, and communication styles to mimic them flawlessly. The goal is to create a sense of absolute authenticity, making the malicious communication indistinguishable from legitimate internal or external correspondence. This level of personalization bypasses many automated defenses that look for generic patterns, because the attack is anything but generic; it's a custom-built weapon tailored specifically for you.
Furthermore, these digital deceivers are masters of psychological manipulation, employing principles like urgency, authority, scarcity, and familiarity. They create situations that demand immediate action, often under the guise of an executive directive or a critical system alert, leaving little time for critical thought. By impersonating a CEO, a senior manager, or a trusted vendor, they invoke a sense of authority that discourages questioning. The threat of missed opportunities or severe consequences (scarcity) can also push victims to act without proper verification. And by mimicking familiar contacts or services, they tap into our inherent trust. This combination of detailed contextual knowledge and psychological manipulation is the true art of the invisible hack, turning what might seem like a simple request into a sophisticated, almost irresistible trap.
When Your Boss's Voice Isn't Your Boss's Voice The Rise of Deepfake Scams
The advent of artificial intelligence, particularly in the realm of synthetic media, has added an entirely new, chilling dimension to the invisible hack: deepfake scams. No longer are attackers limited to text-based impersonation; they can now synthesize voices, and increasingly, even video, that are virtually indistinguishable from real individuals. Imagine receiving a phone call, not just from a number you recognize, but hearing the actual voice of your CEO, sounding stressed and urgent, instructing you to initiate an immediate, off-book wire transfer. This isn't science fiction; it's a terrifying reality that has already cost companies millions. In 2019, a UK-based energy firm was tricked into transferring €220,000 after its CEO’s voice was deepfaked, instructing an employee to send funds to a Hungarian supplier. The employee recognized the CEO's "German accent and the melody of his voice," making the deception incredibly convincing.
The technology behind these deepfake audio attacks is becoming increasingly accessible and sophisticated. With just a few minutes of publicly available audio – from conference calls, public speeches, or even social media videos – AI models can be trained to generate highly realistic speech in a target's voice. The implications for social engineering are profound. Vishing (voice phishing) attacks, already effective, become exponentially more dangerous when the caller genuinely sounds like a trusted colleague, superior, or client. This bypasses the visual cues we might rely on in an email (like checking the sender's address) and directly attacks our auditory trust mechanisms. Our brains are hardwired to process and trust familiar voices, making it incredibly difficult to discern a synthetic voice from a genuine one, especially when coupled with a believable, urgent narrative.
The threat extends beyond just voice. As deepfake video technology improves, we can anticipate more sophisticated attacks involving video calls or recorded messages. While still computationally intensive and less common in mainstream attacks, the potential for a threat actor to impersonate someone in a video conference, giving "face-to-face" instructions, is a looming concern. This technological leap means that the "invisible hack" is becoming less about what you see or read, and more about what you hear and perceive as authentic. It requires a fundamental shift in how we verify digital identities and requests, moving beyond simple recognition to proactive, multi-channel verification, because what sounds or looks real, might in fact be a meticulously crafted digital phantom designed to steal your money or data. The human element, once again, becomes the crucial vulnerability, amplified by cutting-edge AI.
The CEO's Urgent Email A Deep Dive into Business Email Compromise
Business Email Compromise (BEC) is arguably the most financially devastating form of the "invisible hack," costing businesses globally billions of dollars annually. It’s not a technical hack in the traditional sense; it’s a masterclass in social engineering that exploits trust, authority, and often, a sense of urgency. The core premise is simple: an attacker impersonates a high-ranking executive, often the CEO or CFO, and sends an email to an employee responsible for finances, instructing them to make an urgent wire transfer to a fraudulent account. The brilliance of BEC lies in its simplicity and its reliance on human psychology, making it incredibly difficult to detect with automated tools alone, and often leaving no trace of malware or compromised systems.
A typical BEC scenario unfolds with meticulous reconnaissance. The attacker first identifies key players within an organization: the CEO/CFO (the impersonated authority figure) and an employee in finance or accounts payable (the target who can execute the transfer). They'll research company structure, email conventions, and even typical communication patterns. The fraudulent email itself will often mimic the legitimate executive's writing style, signature block, and even their usual time of sending emails. It might contain subtle pressure tactics, such as claiming the transfer is for a highly confidential acquisition, a sensitive vendor payment, or an urgent legal matter, often stressing that it needs to be completed "immediately" and "discreetly." The email address itself is usually spoofed or a lookalike domain (e.g., `companyy.com` instead of `company.com`), designed to be overlooked in a quick glance.
The psychological leverage in BEC is immense. The finance employee receives an urgent, seemingly legitimate request from their highest superior. The natural inclination is to comply, especially when the message emphasizes confidentiality and speed. Questioning the CEO, especially in an urgent situation, can feel like insubordination or a delay that could jeopardize a critical business deal. This creates a powerful internal conflict, where the desire to follow instructions and be a good employee overrides any nascent suspicion. The attacker is essentially hijacking the internal chain of command and leveraging the inherent power dynamics within an organization. Once the transfer is made, the funds are quickly moved through multiple international accounts, making recovery incredibly difficult, if not impossible. This deep exploitation of trust and organizational hierarchy is why BEC remains such a pervasive and costly threat, constantly evolving to find new ways to bypass our vigilance and exploit our human nature.
The Information Advantage How OSINT Fuels the Invisible Hack
At the heart of every truly successful "invisible hack" lies a treasure trove of information, meticulously gathered and strategically deployed. This is where Open-Source Intelligence (OSINT) plays a pivotal, often underappreciated, role. OSINT refers to any information that is publicly available – from corporate websites and press releases to social media profiles, news articles, academic papers, and government records. While seemingly innocuous on its own, when aggregated and analyzed by a skilled social engineer, this data becomes the blueprint for crafting highly personalized and devastatingly effective attacks. Attackers don't need to 'hack' anything to get this data; they simply need to know where to look and how to connect the dots, transforming seemingly disparate pieces of information into a cohesive narrative for deception.
Consider the wealth of information available on platforms like LinkedIn. A quick search can reveal an employee's job title, their responsibilities, their connections, their past employers, and even their professional interests. This allows attackers to identify potential targets, understand their roles within an organization, and even craft emails that appear to be related to their professional sphere. A finance manager might receive a phishing email disguised as an invoice from a vendor they frequently interact with, or an HR professional might receive a message posing as a job applicant with a malicious attachment. The details gleaned from LinkedIn, combined with information from a company's "About Us" page (organizational structure, executive names) and news sections (recent projects, partnerships), provide a rich tapestry for impersonation.
Social media platforms like Facebook, Instagram, and X (formerly Twitter), while often considered personal, can inadvertently provide attackers with crucial insights into an individual's life outside of work. Vacation plans, family details, hobbies, political leanings, and even complaints about work can all be leveraged. For instance, an attacker might send a phishing email related to a specific airline if they know you're traveling, or impersonate a friend asking for help if they've gleaned enough personal context. The attacker’s goal is to build a comprehensive psychological profile, understanding not just what you do, but who you are, what you care about, and what might prompt you to act without thinking. This deep understanding of the target, built almost entirely from publicly available information, is the invisible engine that powers the most sophisticated and successful social engineering attacks, making OSINT a critical, yet often underestimated, weapon in the cybercriminal's arsenal.