Building Your Digital Fortress Practical Steps to Fortify Your Phone
While the threat of zero-click attacks can feel overwhelmingly sophisticated and beyond the control of the average user, it's crucial not to succumb to fatalism. While complete immunity might be an elusive ideal, there are concrete, actionable steps you can take to significantly harden your device against these and many other forms of cyber threats. Think of it as building a multi-layered digital fortress around your most personal device. Each layer of defense, even if seemingly small, adds to the overall resilience, making you a much less attractive and far more difficult target. The goal isn't just to stop zero-click attacks, but to elevate your overall digital hygiene, making your device a much tougher nut to crack for any adversary, from opportunistic hackers to state-sponsored actors. It's about empowerment through proactive measures, taking back some control in a landscape often defined by unseen dangers.
The first and arguably most critical defense against zero-click exploits is keeping your device's operating system and all applications meticulously updated. Software updates are not just about new features or aesthetics; they are primarily about security. When a vulnerability is discovered, whether by ethical hackers or in the wild by malicious actors, the software vendor (Apple, Google, etc.) works diligently to develop and release a patch. These patches close the security holes that zero-click exploits often leverage. Running outdated software is akin to leaving your front door wide open after the locksmith has already fixed the lock. Make it a habit to install updates as soon as they become available, don't postpone them. Turn on automatic updates if your device supports it, and regularly check for system and app updates manually. This simple, often overlooked step is your absolute frontline defense, patching known weaknesses before they can be exploited by an invisible intruder.
Elevating Your Digital Hygiene and App Scrutiny
Beyond core system updates, cultivate a rigorous approach to your installed applications. Every app on your phone represents a potential attack surface. Regularly review your installed apps and remove any that you no longer use or that seem suspicious. Less is often more when it comes to security. Be incredibly selective about what you download, sticking to official app stores (Apple App Store, Google Play Store) and scrutinizing developer reputations and user reviews. While even official stores aren't entirely foolproof, they offer a significantly higher level of vetting than third-party sources. Pay close attention to the permissions requested by apps during installation or first use. Does a flashlight app really need access to your microphone, camera, and contacts? Probably not. Deny unnecessary permissions, and regularly review and revoke permissions for existing apps via your phone's settings. This limits the data an app can access, even if it were to be compromised by an exploit.
Your network security practices also play a vital role in fortifying your phone. Be extremely cautious when connecting to public Wi-Fi networks, which are often unsecured and can be fertile ground for attackers to intercept data or even launch local network-based exploits. Consider using a reputable Virtual Private Network (VPN) whenever you're on an untrusted network. A VPN encrypts your internet traffic, creating a secure tunnel that makes it much harder for eavesdroppers to intercept your data or for attackers to identify your device as a target. While a VPN won't stop a zero-click exploit that leverages an OS vulnerability directly, it adds a crucial layer of privacy and protection against network-level attacks and surveillance. Furthermore, disable Wi-Fi and Bluetooth when you're not actively using them. This reduces your device's exposure to potential proximity-based exploits and limits the avenues an attacker could use to gain initial access.
"In the face of sophisticated threats like zero-click attacks, a robust security posture isn't a luxury, it's a necessity. It involves a combination of technical safeguards and a profound shift in user behavior towards constant vigilance and proactive defense." - Bruce Schneier, renowned security technologist.
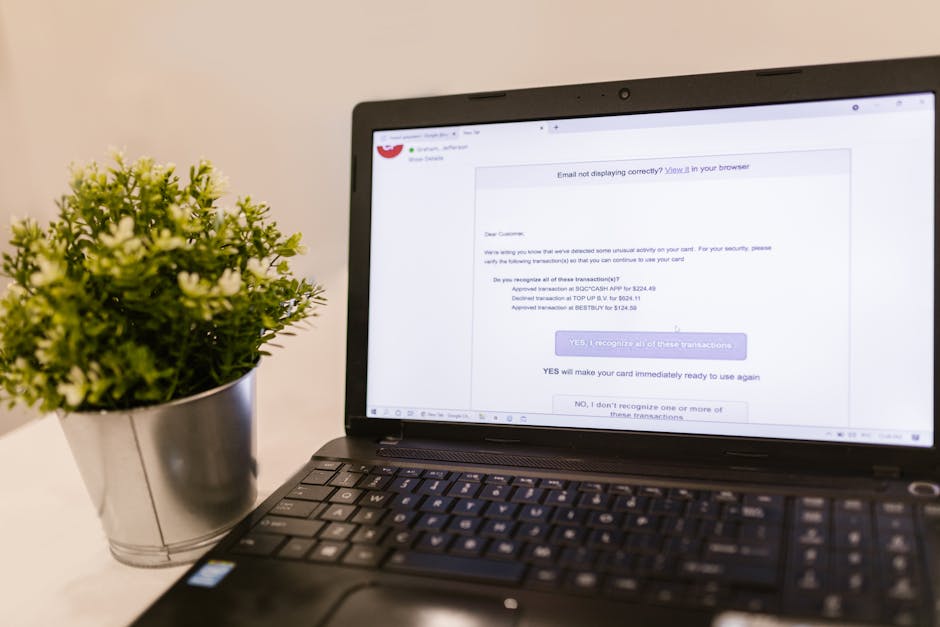
Strong authentication is another non-negotiable aspect of your digital fortress. While zero-click attacks aim to bypass user interaction, strong authentication can limit the damage if an attacker gains access or if your device is physically stolen. Always use a strong, unique passcode for your phone, preferably an alphanumeric one rather than a simple PIN. Enable biometric authentication (fingerprint, face ID) for convenience, but ensure a passcode is always a fallback. Crucially, enable Two-Factor Authentication (2FA) or Multi-Factor Authentication (MFA) on all your online accounts, especially email, banking, and social media. Use authenticator apps (like Authy or Google Authenticator) or hardware security keys (like YubiKey) over SMS-based 2FA, as SMS can be vulnerable to SIM-swapping attacks. Even if an attacker gains control of your phone and tries to log into your accounts, strong 2FA can act as a critical barrier, preventing them from accessing your sensitive data across other services.
Advanced Safeguards and Mindset Shifts
For individuals who might be at higher risk – such as journalists, activists, government officials, or business executives – additional, more advanced safeguards might be necessary. Consider using a "burner" phone for highly sensitive communications or travel, keeping your primary device as clean as possible. Regularly back up your essential data to a secure, encrypted cloud service or an external drive, so that in the event of a compromise, you can wipe your device without significant data loss. For those with extremely high-risk profiles, periodic forensic analysis of their devices by specialized security firms or human rights organizations can help detect sophisticated spyware, although this is expensive and not readily available to the general public. Apple's Lockdown Mode, introduced in iOS 16, offers an extreme, though restrictive, level of security for individuals who believe they may be targeted by state-sponsored spyware. It disables certain features, reduces attack surfaces, and offers additional hardening, but at the cost of some functionality and convenience.
Ultimately, defending against zero-click attacks requires more than just technical measures; it demands a fundamental shift in mindset. It means moving beyond the passive assumption of security and embracing a proactive, vigilant approach to your digital life. Understand that no system is 100% impervious, and the threat landscape is constantly evolving. Stay informed about the latest cybersecurity threats and best practices. Be skeptical of anything that seems too good to be true, and always question the digital interactions you have. While the thought of an invisible threat can be unsettling, knowledge is your most powerful weapon. By adopting a layered security strategy, maintaining meticulous digital hygiene, and fostering a healthy skepticism, you significantly reduce your attack surface and make yourself a far less appealing target for even the most sophisticated digital predators. This isn't about eliminating risk entirely, but about managing it intelligently, empowering you to navigate the complex digital world with greater confidence and resilience.