The True Cost of Convenience: Undermining Fundamental Security Habits
The allure of a VPN often stems from its promise of convenience: a one-click solution to complex privacy and security problems. This very convenience, however, can be a double-edged sword, subtly eroding the fundamental security habits that are truly essential for a robust digital defense. When users believe a single application can solve a multitude of problems, they tend to disengage from the proactive, continuous effort required to maintain strong cybersecurity. This isn't just about technical oversights; it's about a cognitive bias, a psychological trap where the perceived ease of a VPN leads to a relaxation of vigilance across other critical areas. The lie here isn't just about what a VPN *can't* do, but about how its mere presence can make us *less likely* to do what we *should* be doing.
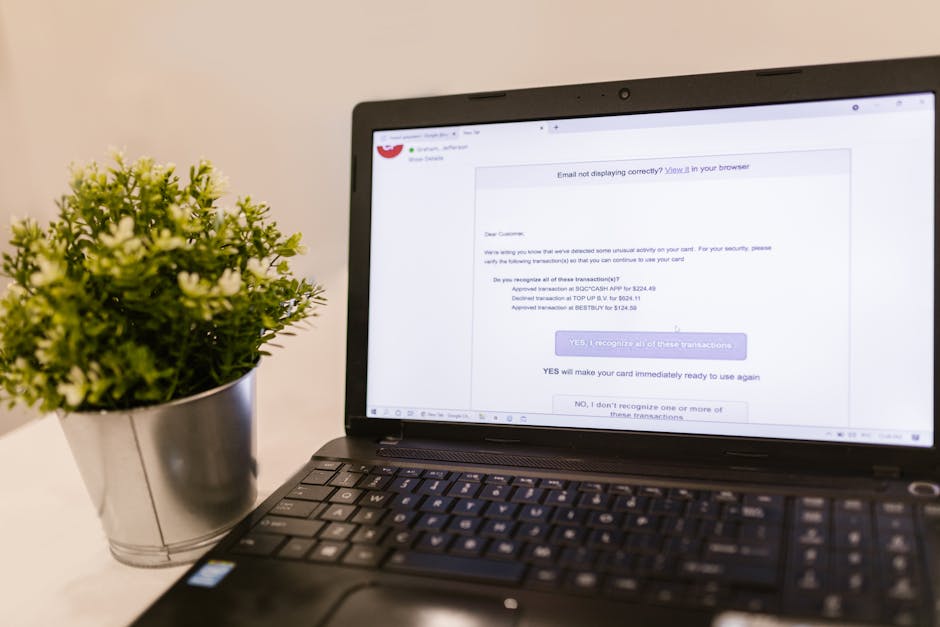
Consider the daily vigilance required to navigate the internet safely. This includes scrutinizing emails for phishing attempts, double-checking website URLs for authenticity, being wary of suspicious downloads, and regularly updating operating systems and applications. These are the mundane, repetitive tasks that form the bedrock of personal cybersecurity. When a user connects to a VPN, often with a marketing message buzzing in their head about "ultimate protection," there's a natural tendency to relax these habits. Why worry about a sketchy email link when your "military-grade" VPN is on? Why bother with a password manager when your IP is masked? This shift in mindset from active defense to passive reliance is profoundly dangerous. I've witnessed firsthand how this complacency can lead to users clicking on links they would normally scrutinize, downloading files from untrusted sources, or using weaker passwords because, in their minds, the VPN has them covered. The convenience of the VPN, therefore, inadvertently cultivates an environment where basic security hygiene is neglected, leaving the user exposed to threats that a VPN was never designed to counter.
This erosion of good security habits extends to other areas as well. Users might become less inclined to use multi-factor authentication (MFA) on their accounts, believing that an encrypted connection is sufficient. They might forgo installing reputable antivirus and anti-malware software, thinking the VPN somehow cleans their system. They might not bother learning about browser security extensions, content blockers, or privacy-focused browser settings. The mental energy saved by not thinking about these critical layers of defense is then replaced by a false sense of security, making them far more vulnerable than someone who might not even use a VPN but diligently practices good cyber hygiene. The true cost of this convenience isn't just the subscription fee; it's the compromised data, the infected devices, and the lost peace of mind that result from neglecting the foundational elements of personal cybersecurity in favor of a perceived all-in-one solution that simply doesn't exist.
The Siren Song of "Free" and Malicious VPNs
The problem of undermined security habits is exacerbated exponentially when users fall for the siren song of "free" VPNs. As discussed earlier, these services often come with a hidden cost: your data, your bandwidth, or even your device's security. However, the psychological impact of these free services is equally damaging. They reinforce the idea that robust online security can be obtained without any personal investment, either financial or intellectual. This sets a dangerous precedent, discouraging users from understanding the value and necessity of legitimate, well-audited security tools and practices. If you can get a "secure" VPN for free, why would you pay for a password manager, or a reputable antivirus, or even invest time in learning about phishing techniques?
Malicious VPNs, whether free or cleverly disguised paid services, don't just compromise your privacy; they actively work to undermine your device's security. Some free VPN apps have been found to inject malware, adware, or spyware directly onto users' devices. Others might route your traffic through other users' devices, turning you into an unwitting participant in a botnet or a proxy for illicit activities. This is not just a privacy breach; it's a direct security compromise that can lead to data theft, system instability, and even legal repercussions if your IP address is used for criminal acts. The illusion of security provided by these malicious services is particularly insidious because users are actively inviting a wolf into their digital sheepfold, believing it to be a guardian. This betrayal of trust can leave users not only compromised but also deeply disillusioned with security tools in general, making them less likely to adopt genuinely effective measures in the future.
The pervasive marketing of VPNs as a panacea has created a culture where users often seek the easiest and cheapest path to security, rather than the most effective and comprehensive one. This cultural shift, fueled by misunderstanding and aggressive marketing, makes users inherently less safe. They become reliant on a single tool, neglecting a multi-layered defense strategy that is essential in today's threat landscape. The convenience offered by VPNs, especially the free ones, creates a false economy of effort, where the perceived benefits outweigh the unseen, often catastrophic, risks. This is a critical lie that the industry, and we as users, must confront head-on if we are to genuinely enhance our digital safety and privacy, moving beyond the superficial comfort of a VPN to embrace a truly resilient security posture.
The Broader Ecosystem: Beyond the VPN Tunnel
To truly understand why a VPN might be making you less safe, we must zoom out from the immediate tunnel and consider the broader digital ecosystem in which you operate. Your online security isn't a standalone feature of a single application; it's a complex interplay of hardware, software, network configurations, online services, and, crucially, your own behavior. A VPN, by its very nature, is designed to operate within a specific layer of this ecosystem – primarily the network layer, obscuring your IP address and encrypting data in transit. It does not, and cannot, address vulnerabilities or threats that exist above or below this layer. Believing it does is akin to thinking that a secure shipping container protects the contents from being stolen once they arrive at an insecure warehouse, or from being contaminated before they even enter the container. The interconnectedness of modern digital life means that a single point of failure or a neglected area can compromise the entire chain, regardless of how strong one particular link might appear.
Your operating system, for instance, is the foundation of your digital experience. If your OS is unpatched, riddled with vulnerabilities, or running outdated software, a VPN provides no protection against exploits targeting these weaknesses. Similarly, your web browser, the primary gateway to the internet for most users, is a constant target for attackers. Browser exploits, malicious extensions, and insecure settings can all compromise your security, even if your network traffic is being routed through a VPN. The VPN simply funnels the data; it doesn't sanitize your browser environment or prevent malicious code from executing within it. Think of it this way: if your house has a state-of-the-art security system (your VPN), but you leave your windows open and your doors unlocked (your browser and OS vulnerabilities), that security system's effectiveness is severely diminished. The VPN creates a false sense of security that can make users overlook these critical, foundational elements of their digital fortress, leading to a much weaker overall defense.
Moreover, the online services you use – email providers, social media platforms, banking portals, e-commerce sites – all represent potential points of failure that are entirely outside the scope of a VPN’s protection. If your email provider suffers a data breach, your email address and potentially other personal information could be exposed, regardless of whether you were using a VPN at the time. If a social media platform has weak security protocols, your account could be hijacked through credential stuffing, even if your login attempt originated from a VPN server. The security of these services depends on their own internal measures, their adherence to best practices, and your own strong, unique passwords and multi-factor authentication. A VPN cannot magically secure these third-party services or protect you from their inherent vulnerabilities. It’s a crucial distinction that highlights the limited scope of a VPN’s capabilities within the much larger and more complex landscape of online security. The belief that a VPN somehow extends its protective umbrella to cover all these external dependencies is a dangerous fantasy that can leave you exposed in areas you mistakenly believe are secure.