Who's Pulling the Strings? The Architects of Chaos
To truly grasp the gravity of the looming digital apocalypse, we must first understand the diverse and increasingly sophisticated actors who are actively shaping this threat landscape. It's not a monolithic enemy; rather, it’s a complex ecosystem of state-sponsored entities, highly organized criminal syndicates, ideologically driven hacktivists, and even disgruntled insiders, all operating with varying motives and capabilities. The lines between these groups are often blurred, with nation-states sometimes employing or tolerating criminal groups, and hacktivists occasionally leveraging tools developed by more powerful adversaries. Dissecting their motivations, methods, and targets is crucial to comprehending the multi-faceted nature of the digital threats we face, and why a global, coordinated attack is not just a theoretical exercise.
For years, the cybersecurity community has categorized these actors into distinct groups, but the reality on the ground is far messier and more dynamic. Imagine a shadowy global marketplace where zero-day exploits are traded like commodities, where sophisticated malware is rented out as a service, and where the intelligence gathered from one operation can be leveraged by another, seemingly unrelated group. This interconnectedness amplifies the danger, as techniques and tools perfected by one actor can quickly proliferate and be adopted by others. Understanding who is behind the keyboard, what drives them, and what resources they command is the first step in building effective defenses against a threat that is constantly evolving and adapting, much like a super-virus mutating to bypass our immunological responses.
My own journey through the labyrinthine world of digital forensics and threat intelligence has revealed the sheer ingenuity and patience of these adversaries. I've seen evidence of state-sponsored groups meticulously planning operations for years, patiently gathering intelligence, and developing custom tools tailored to specific targets. I've also witnessed the brutal efficiency of ransomware gangs, who operate like well-oiled corporations, complete with customer support, negotiation teams, and even internal HR departments. It's a sobering realization that some of the most innovative and persistent entities in the world are not always working for the common good. Their collective efforts, whether coordinated or coincidental, contribute to the relentless pressure on our digital infrastructure, pushing us closer to a potential breaking point.
The Shadowy Hand of Nation-States
At the apex of the threat landscape sit nation-states, wielding cyber capabilities as powerful instruments of foreign policy, espionage, and warfare. Countries like Russia, China, North Korea, and Iran have invested heavily in developing sophisticated cyber armies, deploying them to achieve a wide array of strategic objectives. Their motives extend far beyond financial gain, encompassing intelligence gathering, intellectual property theft, political interference, and the pre-positioning of capabilities for potential future kinetic conflicts. These are not opportunistic hackers; these are strategic actors with long-term goals and seemingly endless resources, making them arguably the most dangerous players in the global cyber arena.
Russia, for instance, has a long and well-documented history of aggressive cyber operations. Groups like APT28 (Fancy Bear) and APT29 (Cozy Bear), widely attributed to Russian intelligence agencies, have been implicated in some of the most significant cyber incidents of the past decade. From the DNC hacks during the 2016 U.S. presidential election to the devastating NotPetya attack (which, while targeting Ukraine, spread globally and caused billions in damages), Russian state-sponsored actors have demonstrated a willingness to push boundaries, often blurring the lines between espionage and outright sabotage. Their operations frequently aim to sow discord, destabilize adversaries, and gather intelligence that can be leveraged for geopolitical advantage, proving that the battlefield can indeed be entirely digital, yet with tangible real-world consequences.
China's cyber activities, on the other hand, are often characterized by large-scale economic espionage, aimed at stealing intellectual property and technological secrets to bolster its own industries and military capabilities. Groups like APT41 and APT10 have been linked to campaigns that target a vast array of sectors, from aerospace and defense to healthcare and technology. Their systematic approach to data exfiltration represents an immense transfer of wealth and innovation, posing a long-term threat to global competitiveness. North Korea, a nation under heavy international sanctions, leverages its cyber capabilities primarily for financial gain, engaging in cryptocurrency theft and bank heists to fund its weapons programs, as evidenced by the notorious Lazarus Group's activities, including the WannaCry ransomware outbreak and attacks on financial institutions like Bangladesh Bank. Iran, too, has emerged as a significant cyber power, often engaging in disruptive attacks against perceived adversaries, particularly in the Middle East, as well as espionage campaigns targeting critical infrastructure and government entities.
The Profit-Driven Empires of Cybercrime
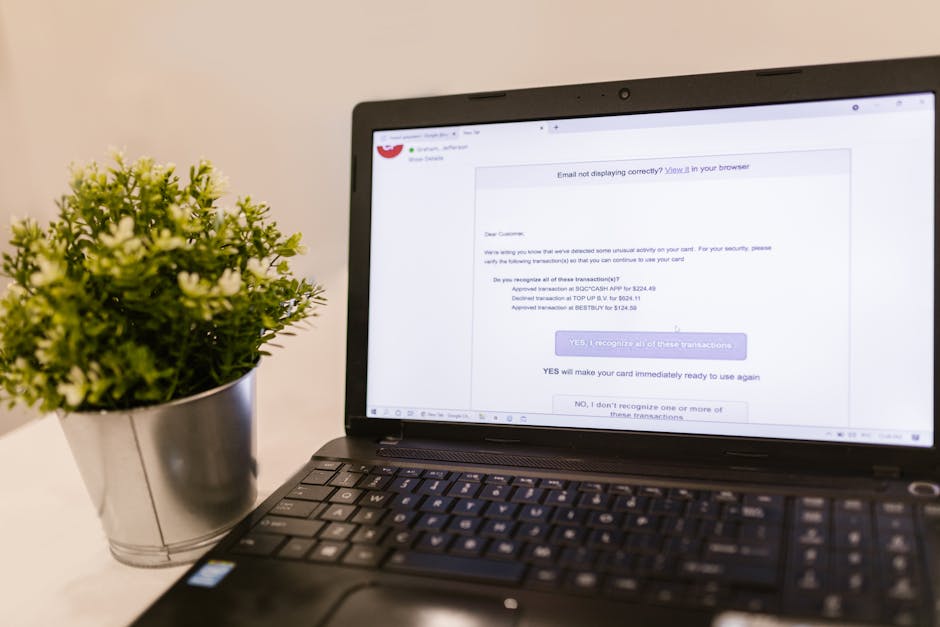
While nation-states pursue strategic objectives, organized cybercrime groups are driven by one primary motive: profit. These are not disparate individuals operating in isolation; they are often highly structured, well-resourced organizations that rival legitimate businesses in their operational sophistication. They specialize in a variety of illicit activities, including ransomware, data theft for resale, credit card fraud, business email compromise (BEC) scams, and sophisticated phishing operations. The sheer volume of money flowing through these criminal enterprises fuels a continuous cycle of innovation and expansion, making them incredibly resilient and adaptable to law enforcement efforts.
The ransomware ecosystem, in particular, has evolved into a highly specialized industry. We've seen the rise of "ransomware-as-a-service" (RaaS) models, where developers create the malicious software and then lease it to "affiliates" who handle the actual deployment and negotiation, taking a cut of the ransom payments. Groups like Conti, REvil (Sodinokibi), and DarkSide have operated with impunity for extended periods, extorting hundreds of millions of dollars from victims worldwide. Their operations often involve double extortion, where not only is data encrypted, but it's also exfiltrated and threatened to be leaked if the ransom isn't paid, adding immense pressure on victims. The professionalism of these groups, sometimes even offering "customer support" to help victims pay, is both disturbing and a testament to their business acumen.
The dark web serves as the unregulated marketplace for these criminal enterprises, facilitating the trade of stolen data, exploits, and illicit services. Here, compromised credentials, credit card numbers, and even entire corporate networks are bought and sold. This underground economy provides the infrastructure and liquidity that sustains the cybercrime industry, making it incredibly difficult for law enforcement to dismantle effectively. The global reach of these networks means that a criminal operation based in one country can easily target victims anywhere in the world, exploiting jurisdictional complexities and the inherent anonymity of the internet. It's a truly global threat, requiring a coordinated international response that is often hampered by political realities and technical challenges.
Hacktivists and the Insider Threat: Unpredictable Wildcards
Beyond the state-sponsored giants and the profit-driven syndicates, two other categories of threat actors add layers of complexity and unpredictability to the digital landscape: hacktivists and insider threats. Hacktivists are individuals or groups who use hacking techniques to promote a political, social, or ideological cause. While their methods might sometimes be less sophisticated than state actors, their impact can still be significant, especially in generating public awareness, disrupting services, or exposing sensitive information to achieve their goals. Groups like Anonymous, for example, have engaged in numerous high-profile operations targeting governments, corporations, and organizations they perceive as unjust or oppressive. Their motivations are often driven by a strong sense of morality, however subjective, and a desire to effect change through digital protest.
The danger with hacktivism lies in its unpredictable nature and the potential for unintended consequences. A DDoS attack meant to temporarily disrupt a website can inadvertently take down critical services. A data leak intended to expose corruption might inadvertently reveal personal information of innocent individuals, leading to further harm. Furthermore, hacktivist operations can sometimes be co-opted or even initiated by state actors seeking to mask their own involvement, adding another layer of deception to the already murky waters of cyber attribution. Their actions, while sometimes lauded by supporters, often operate outside the bounds of law and ethics, contributing to the overall instability of the digital environment and making it harder to distinguish legitimate digital protest from malicious cyber operations.
"The insider threat is often the hardest to detect because it comes from within, from someone who already has legitimate access. Trust, once broken, creates the most dangerous vulnerabilities." - Detective Inspector Anya Sharma, Cybercrime Unit.
Finally, we must not overlook the insider threat – individuals within an organization who use their authorized access to intentionally or unintentionally cause harm. This could be a disgruntled employee seeking revenge, a financially motivated individual selling corporate secrets, or simply a negligent employee who falls victim to a sophisticated phishing scam. While often less dramatic than nation-state attacks, insider threats can be incredibly damaging because they bypass many external security controls. They already have the keys to the kingdom, making detection and prevention particularly challenging. The motivations vary widely, from financial gain to ideological alignment with an external group, or even just pure malice. Mitigating insider threats requires a multi-faceted approach that combines technical controls, robust HR policies, continuous monitoring, and fostering a culture of trust and awareness. The human element, both as a weakness and a strength, remains one of the most critical factors in determining our collective digital resilience.