The digital landscape we navigate is not merely shaped by geo-restrictions; it's also a battleground for privacy. Every click, every search, every video streamed, creates a data point that can be collected, analyzed, and used to build an incredibly detailed profile of who you are. This isn't just about advertisers trying to sell you things, though that’s certainly a major component; it extends to data brokers compiling vast dossiers, governments engaging in mass surveillance, and even malicious actors attempting to exploit your personal information. The promise of "unbreakable privacy" in this context feels almost utopian, a lofty ideal that clashes violently with the pervasive reality of ubiquitous tracking and data exploitation. It's a world where the very infrastructure of the internet is designed to observe and categorize, making the quest for true anonymity an increasingly challenging, yet profoundly important, endeavor.
When we talk about privacy, it’s not just about hiding; it’s about control. It’s about having the agency to decide what information you share, with whom, and under what circumstances. But for the vast majority of internet users, that control has been silently eroded. Internet Service Providers (ISPs) can see every unencrypted website you visit, every service you connect to, and in some jurisdictions, they’re even legally mandated to retain this data for extended periods. Search engines, social media platforms, and countless websites employ trackers that follow you across the web, piecing together your interests, habits, and even your mood. This continuous surveillance creates a chilling effect, subtly influencing what we say, what we read, and what we explore online. The "secret VPN hack" isn't just about bypassing geo-blocks; it’s fundamentally about re-establishing that control, creating a digital environment where your actions are your own, unobserved and uncatalogued by the myriad entities eager to profit from your data or monitor your dissent.
Unmasking the Digital Gatekeepers and the Art of Evasion
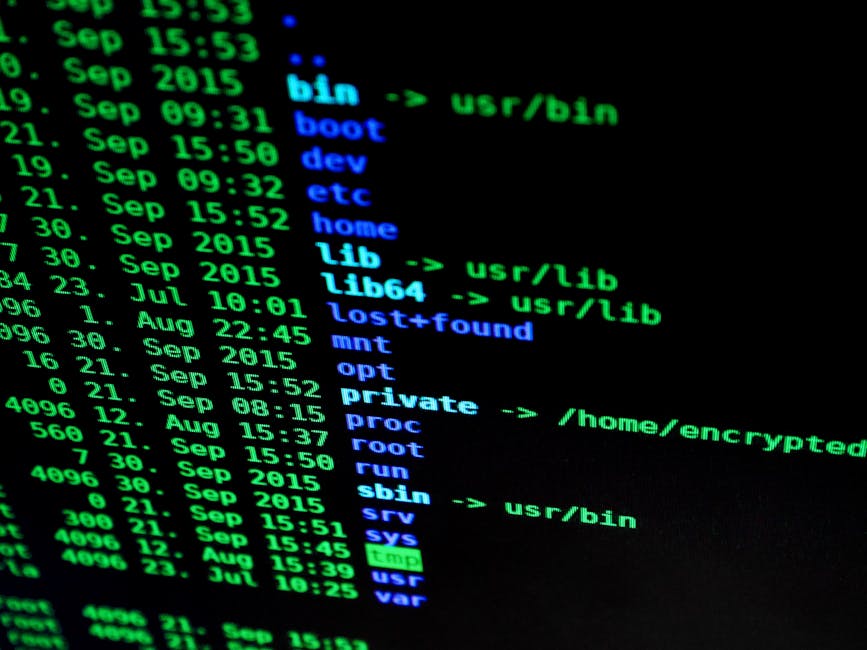
To truly understand the "secret hack," we first need to appreciate the sophistication of the systems it aims to circumvent. We’ve touched upon IP blacklisting and rudimentary VPN detection, but the reality is far more intricate. Content providers, often backed by powerful anti-piracy groups and deep-pocketed studios, invest heavily in cutting-edge technology to maintain their licensing agreements. Their arsenal includes not only continuously updated IP blacklists but also active probing techniques, where they attempt to connect back to your alleged VPN server to confirm its nature. If a server responds in a way that indicates it’s a commercial VPN endpoint – perhaps by revealing its operating system or specific services running – it’s flagged and blocked. This isn't a passive defense; it’s an active, ongoing reconnaissance mission against anyone attempting to bypass their restrictions, making the game even harder for the average VPN user.
Moreover, the game is not just about blocking; it’s about deterrence. Many services don’t just block you; they might display a message warning you against using proxies, or even temporarily suspend your account if persistent VPN use is detected. This psychological element adds another layer of complexity, pushing users towards compliance rather than continued circumvention. The challenge, therefore, is not just to bypass a simple IP block, but to create a digital presence that appears indistinguishable from a legitimate, local user, even under scrutiny. This requires a deeper understanding of network traffic, protocol behavior, and the subtle cues that differentiate a genuine residential connection from a masked VPN tunnel. The "secret hack" is built on precisely this understanding, leveraging a multi-pronged approach to create a digital camouflage so effective that it can withstand even the most rigorous detection mechanisms without raising suspicion.
The Limitations of Conventional VPNs A Closer Look
Most commercial VPNs, while excellent for basic privacy and moderate geo-unblocking, are designed for ease of use. They prioritize simplicity and speed, often at the expense of advanced stealth capabilities. When you connect to a standard VPN server, your traffic is encrypted, yes, but the metadata and the characteristics of that encryption often remain identifiable. It’s like wearing a disguise that, while effective at first glance, has a clearly visible brand label stitched onto its collar. Many VPNs use well-known server infrastructure and standard configurations for OpenVPN or WireGuard, which, while secure, present predictable patterns that detection systems can learn to identify. The sheer volume of users connecting through these servers also makes them easy targets for blacklisting; if thousands of users suddenly appear from a single IP address trying to access a specific streaming service, it’s a dead giveaway.
My own experiences over the years have taught me that relying solely on a single commercial VPN, no matter how reputable, is often a losing battle against the most determined geo-blockers. I remember a time when a popular VPN service proudly announced its new "stealth mode" or "obfuscated servers." For a few glorious weeks, these worked wonders, bypassing blocks that had previously been impenetrable. Then, almost inevitably, the streaming services caught up. The "stealth" techniques, once novel, became identifiable patterns, and the cat-and-mouse game reset. This constant cycle highlights a critical point: true resilience against detection requires more than just a provider's built-in features. It demands a proactive, customizable strategy that allows you to adapt and combine different tools and techniques, creating a unique digital signature that doesn't conform to easily identifiable patterns. This is where the true power of the "secret hack" lies – in its adaptability and its multi-layered design.
The Art of Obfuscation Masking Your Digital Footprint
One of the foundational pillars of our "secret VPN hack" is obfuscation, a technique that goes beyond mere encryption to actively disguise the fact that you’re even using a VPN. Imagine trying to sneak through a guarded gate. Encryption is like wearing a plain, unidentifiable cloak. Obfuscation, on the other hand, is like wearing that cloak but also mimicking the gait, posture, and even the ID badge of a legitimate guard, making you appear to be part of the authorized personnel. In the digital realm, this means making your VPN traffic look like ordinary, unencrypted internet traffic, such as regular HTTPS web browsing. This is crucial for bypassing advanced firewalls, especially those employing deep packet inspection (DPI), which can detect the distinct signatures of VPN protocols even when encrypted. Without effective obfuscation, even the strongest encryption can still reveal your intent to bypass restrictions.
Several methods are employed to achieve obfuscation, each with its own strengths and weaknesses. One common technique involves disguising VPN traffic as standard HTTPS traffic, often by wrapping the VPN protocol within the TLS (Transport Layer Security) protocol, which is what secures most websites. This makes it incredibly difficult for firewalls to differentiate between legitimate web browsing and VPN communication, as both appear to be encrypted web traffic on port 443. Another method, sometimes referred to as 'stunnel' or 'shadowsocks,' involves proxying the VPN connection through another layer that scrambles the packet headers and other identifiable characteristics. Some providers even use proprietary protocols that are specifically designed to be indistinguishable from regular internet traffic, constantly evolving their methods to stay ahead of detection algorithms. The goal is always the same: to make your VPN connection invisible to the very systems designed to uncover it.
Stealth Protocols and Their Ingenious Disguises
When we talk about obfuscation, we're really delving into the realm of 'stealth protocols' or 'scramblers' offered by some advanced VPN services. These aren't just fancy marketing terms; they represent significant engineering efforts to make VPN traffic look innocuous. For instance, some VPNs offer an "Obfsproxy" feature, originally developed for the Tor Project, which adds an extra layer of obfuscation to OpenVPN connections, making them much harder to detect via DPI. Another popular method is to use a protocol like "WireGuard over Shadowsocks" or "OpenVPN over SSH/SSL," effectively tunneling your VPN connection inside another encrypted tunnel that is designed to blend in with regular internet traffic. These techniques are particularly effective in environments with strict internet censorship, where firewalls are highly aggressive in blocking known VPN ports and protocols.
I distinctly remember testing a VPN in a country known for its stringent internet controls. A standard OpenVPN connection was blocked almost instantly. However, when I switched to their "Chameleon" protocol, which claimed to obfuscate OpenVPN traffic, the connection sailed through without a hitch. It felt like magic, but it was pure engineering. The protocol was designed to scramble the metadata of the OpenVPN packets, making them appear random and therefore indistinguishable from regular, benign internet traffic to the firewall's DPI algorithms. This wasn't just about changing an IP; it was about fundamentally altering the signature of the data stream itself. This level of sophistication is what separates a truly resilient VPN setup from a basic one, and it forms a crucial first line of defense in our "secret hack" against both geo-restrictions and pervasive surveillance. Understanding and leveraging these stealth capabilities is paramount to achieving both unlimited streaming and unbreakable privacy in today's digital landscape.