The False Sense of Security Why We Keep Falling for the Trap
Despite the constant warnings from cybersecurity experts, the myriad news reports of data breaches, and the sheer common sense that tells us "free" often comes with a hidden cost, people continue to flock to public Wi-Fi networks with an almost unwavering trust. Why? What is it about our psychological makeup, or perhaps the modern digital landscape, that fosters this pervasive false sense of security? It’s a fascinating, and frankly, a bit frustrating, phenomenon for those of us who spend our days highlighting these very dangers. Part of it, undoubtedly, is the sheer convenience factor, but there are deeper cognitive biases and societal pressures at play that contribute to this collective digital amnesia when it comes to public network safety.
One major contributor is the 'out of sight, out of mind' mentality. Cyber threats are largely invisible. You don't see a hacker physically reaching into your laptop, nor do you see your data packets being intercepted. The danger is abstract, theoretical, until it becomes a devastating reality. This lack of immediate visual feedback means that the brain doesn't register the same level of threat as it would, say, a physical mugging. We tend to underestimate risks that are not tangible or immediately apparent. Furthermore, there's a herd mentality at play; if everyone else in the coffee shop is happily browsing on the public Wi-Fi, it must be safe, right? This social proof often overrides individual caution, leading people to believe that if no one else is panicking, there’s no real danger. It’s a collective delusion that’s incredibly difficult to break, even with hard evidence and expert warnings.
Another significant factor is the perceived invincibility of modern technology and the implicit trust we place in big tech companies. Many users operate under the assumption that their devices, operating systems, and popular apps are inherently secure enough to protect them, regardless of the network they're connected to. "My iPhone is secure," they might think, or "Gmail encrypts everything." While these statements hold some truth, they don't account for the fundamental vulnerabilities of an unencrypted network connection itself. HTTPS provides end-to-end encryption for specific website traffic, but it doesn't protect against DNS spoofing, malware injection from a rogue access point, or the exposure of other unencrypted data from non-HTTPS applications. This overreliance on perceived built-in security features, without understanding their limitations, creates a dangerous blind spot, fostering a false sense of impermeability that leaves users wide open to attacks.
The Myth of HTTPS as a Universal Shield
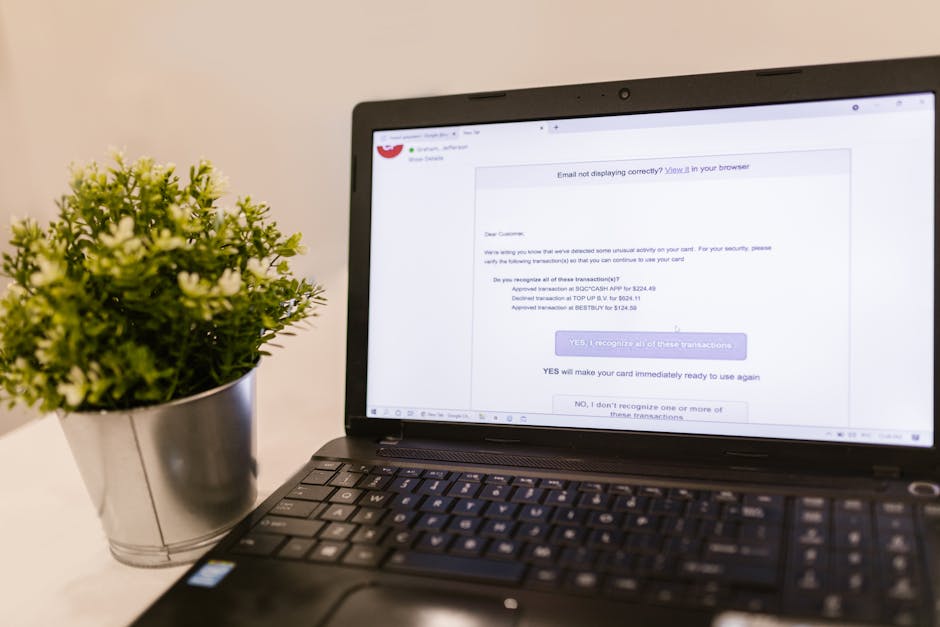
It’s true that the widespread adoption of HTTPS (the "S" stands for "Secure") has significantly improved online security. When you see that padlock icon in your browser's address bar, it means the connection between your browser and the website you're visiting is encrypted. This is a crucial layer of defense, scrambling your data so that even if it's intercepted, it's unreadable to a third party. Many people, myself included, will instinctively look for that padlock before entering sensitive information. However, relying solely on HTTPS as your shield on public Wi-Fi is a dangerously incomplete strategy, a myth that needs to be thoroughly debunked.
Firstly, not all websites and online services use HTTPS exclusively. While major sites like banking platforms, email providers, and social media giants have largely transitioned, countless smaller websites, older forums, and even some niche applications still operate over plain HTTP. The moment you navigate to one of these unsecured sites, even inadvertently, your data is exposed. Furthermore, even on an HTTPS-secured site, certain metadata about your browsing activity can still be gleaned by an attacker on an unsecured network. They might not see the content of your encrypted communication, but they can often see which websites you're visiting and the amount of data being transferred, which can still be used to build a profile or launch more targeted attacks. It's like seeing the outside of an envelope but not its contents; you still know who sent it and where it's going.
Secondly, HTTPS doesn't protect against all forms of public Wi-Fi attacks. As we discussed, DNS spoofing can redirect you to a malicious site that might even have its own valid-looking (but fake) HTTPS certificate, tricking you into believing you're on a secure, legitimate site. Rogue access points can also perform SSL stripping attacks, where they downgrade your connection from HTTPS to HTTP without your knowledge, making your "secure" session vulnerable. Even if the website itself is secure, the underlying network infrastructure can be compromised, leading to vulnerabilities that HTTPS simply isn't designed to address. It’s a vital tool, yes, but it’s just one tool in a much larger cybersecurity arsenal, and it's far from a foolproof solution for the inherent insecurity of public Wi-Fi. Understanding its limitations is just as important as appreciating its strengths, especially when navigating the treacherous waters of open networks.