Having navigated the treacherous waters of browser fingerprinting, persistent trackers, data brokers, and the inherent vulnerabilities of the human element, it should be abundantly clear that a VPN, while invaluable, is merely the first line of defense, not the impenetrable fortress many perceive it to be. The alarming truth is that achieving genuine online privacy and security in today's digital landscape demands a multi-layered, holistic approach. It requires a fundamental shift in mindset, moving away from the simplistic notion of a single "fix" and embracing a comprehensive strategy that addresses every potential vector of attack and surveillance. This isn't about becoming a paranoid hermit; it's about being an informed, proactive participant in your own digital destiny, reclaiming control over your personal data one intelligent step at a time. Let's explore how to build that fortified digital sanctuary, starting with the very tools you use to interact with the web.
Building a Fortified Digital Sanctuary A Multi-Layered Approach
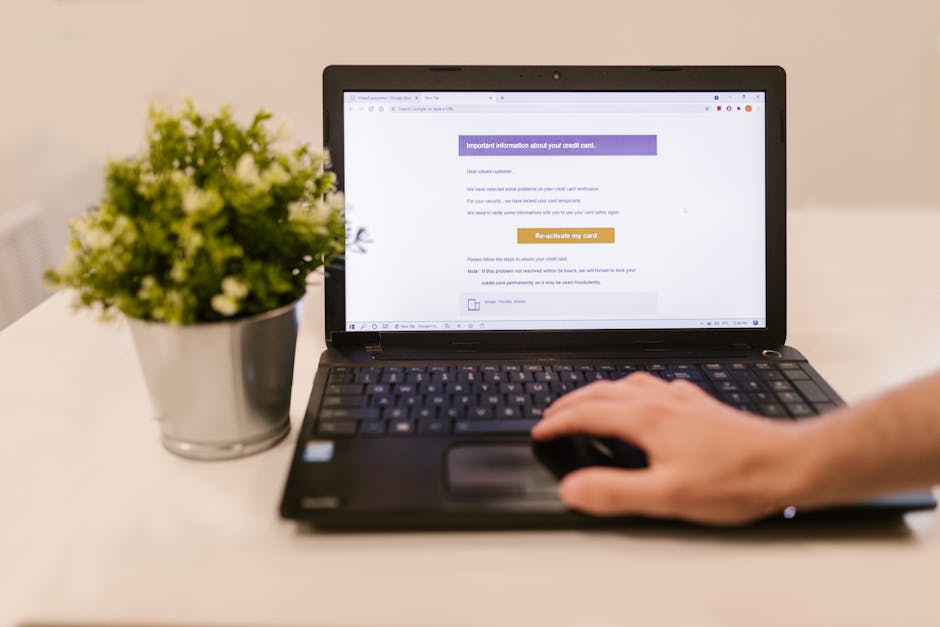
The journey towards enhanced online privacy begins with a critical assessment of your everyday browsing tools. Your web browser is the primary gateway to the internet, and as such, it's a major vector for tracking. Simply using a VPN won't stop your browser from leaking information. The first step is to choose a privacy-focused browser and then harden its settings. Browsers like Brave, which comes with built-in ad and tracker blocking, or Firefox, especially when configured with privacy-enhancing extensions and settings, are significantly better choices than default browsers like Chrome or Edge, which are often designed with data collection in mind. Taking the time to delve into your browser's privacy settings, disabling third-party cookies by default, and blocking unwanted pop-ups and notifications can dramatically reduce your exposure to tracking scripts and unwanted data collection. This proactive configuration is foundational, setting the stage for all subsequent privacy enhancements.
Beyond the browser choice, a suite of well-chosen browser extensions can provide an additional, crucial layer of defense. Tools like uBlock Origin are indispensable for blocking ads, trackers, and malicious domains, making your browsing experience faster, cleaner, and significantly more private. Privacy Badger, developed by the EFF, intelligently learns to block invisible trackers that follow you around the web. For those seeking even greater control, extensions like NoScript allow you to selectively enable JavaScript on websites, preventing potentially malicious scripts from running by default. The key is to be judicious; installing too many extensions can sometimes introduce new vulnerabilities or even make your browser fingerprint more unique. A minimalist approach, focusing on essential, reputable privacy tools, is often the most effective. These tools work hand-in-hand with your VPN, cleaning up the data exhaust that your network connection can't hide.
Securing Your Operating System and Devices
Your operating system (OS) and devices are the bedrock of your digital life, and any compromise at this level can render all other privacy efforts moot. Regularly updating your OS and all installed software is paramount. These updates often contain critical security patches that close vulnerabilities attackers could exploit to gain access to your system or data. Neglecting updates is like leaving a gaping hole in your digital fortress, inviting intruders. Furthermore, strong, unique passwords for all your accounts, ideally managed with a reputable password manager, are non-negotiable. Reusing passwords is an open invitation for credential stuffing attacks, where a breach on one service can compromise all your others. Enabling two-factor authentication (2FA) wherever possible adds another robust layer, requiring a second verification method beyond just your password, making it significantly harder for unauthorized access.
Consider also the physical security of your devices and their internal configuration. Full disk encryption, available on most modern operating systems (e.g., BitLocker on Windows, FileVault on macOS, LUKS on Linux), ensures that even if your device is stolen, your data remains inaccessible without the encryption key. On mobile devices, meticulously review app permissions. Does a flashlight app truly need access to your contacts or location? Probably not. Restrict unnecessary permissions to limit the data apps can collect about you. Furthermore, be wary of connecting to public Wi-Fi without a VPN, as these networks are often unsecured and ripe for eavesdropping. Even with a VPN, exercising caution about what sensitive information you access on such networks is a wise practice. Your device is the source of all your digital activity, so securing it at its core is fundamental to overall privacy.
Fortifying Your Network and Online Identity Management
Beyond your personal devices, your home network can also be a point of vulnerability. Taking steps to secure your router is crucial. Change the default administrator password immediately, and ensure your Wi-Fi uses strong encryption (WPA2 or WPA3). Consider setting up a separate guest network for visitors or IoT devices; this isolates them from your main network, preventing potential compromises of smart devices from affecting your primary computers. Using privacy-focused DNS servers (like Cloudflare's 1.1.1.1 or Quad9) and enabling DNS over HTTPS (DoH) or DNS over TLS (DoT) can further encrypt your DNS queries, preventing your ISP from seeing your browsing history even if there's a DNS leak from your VPN. These measures create a more secure perimeter around your entire digital household, complementing the protection offered by individual VPN connections.
Finally, a critical aspect of reclaiming privacy involves managing your online identity with intentionality. This means questioning every piece of information you share online and considering alternatives. For email, instead of using your primary address for every registration, explore email alias services (like SimpleLogin or AnonAddy) that forward emails to your real inbox without exposing your true address. For phone numbers, consider temporary or burner numbers for online verifications or services you don't fully trust. Avoid using "Login with Google" or "Login with Facebook" options, as these often grant third-party services extensive access to your social profiles and data. Each of these convenience features trades a small amount of ease for a significant chunk of your privacy. By consciously compartmentalizing your online identities and minimizing the data you expose, you make it exponentially harder for data brokers and trackers to build a comprehensive, unified profile of your digital self. True online privacy isn't a passive state; it's an active, ongoing commitment to vigilance, education, and strategic action.