Navigating the treacherous landscape of app-based data theft can feel like an overwhelming task, akin to trying to empty the ocean with a teacup. However, feeling powerless is precisely what the data-hungry corporations want. The good news is that you are not helpless. By understanding the mechanisms of data collection, you can adopt a proactive stance, implementing practical strategies and cultivating better digital hygiene habits to significantly reduce your exposure and reclaim a substantial degree of control over your personal information. It’s a continuous journey, not a one-time fix, but every step you take empowers you to build a stronger, more private digital life. Think of it as fortifying your digital home, brick by brick, against unwanted intrusion, making it a less appealing target for those who seek to profit from your personal data.
Mastering the App Permissions Grand Control over Your Digital Gatekeepers
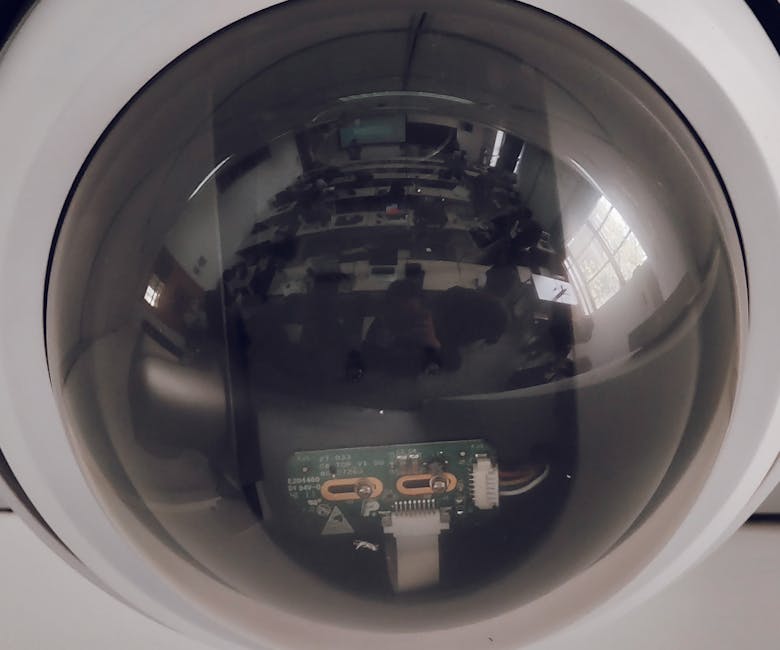
One of the most immediate and impactful actions you can take is to meticulously review and manage your app permissions. When you install an app, it often bombards you with requests for access to your microphone, camera, location, contacts, storage, and more. Too often, we mindlessly tap "Allow" to get to the app's functionality faster. This is your first line of defense, and it's surprisingly powerful. Take the time to understand why an app needs a particular permission. Does a flashlight app truly need access to your microphone? Does a simple game require your precise location at all times, even when not actively playing? Probably not. Modern operating systems, both iOS and Android, have made great strides in providing granular control over these permissions, allowing you to grant access only "while using the app" or to "ask every time," rather than a blanket "always allow."
To effectively manage these permissions, delve into your phone's settings. On iOS, navigate to "Settings" > "Privacy & Security," where you'll find categorized lists for Location Services, Contacts, Calendars, Photos, Microphone, Camera, and more. You can then review which apps have access to each category and revoke permissions as needed. For Android users, go to "Settings" > "Apps" (or "Apps & notifications") > "Permission manager." Here, you’ll see a list of permission types, such as "Location," "Microphone," and "Camera." Tapping on each will show you which apps have been granted that permission, and you can toggle them off. Make this a regular habit, perhaps once a month, to ensure no app has silently gained excessive permissions through updates or oversight. Remember, if an app ceases to function after you revoke a permission, it might actually need it, but if it continues to work fine, you’ve just taken back a piece of your privacy without sacrificing utility. It’s a small effort that yields significant returns in your personal data security.
Making Informed App Choices Your Personal Digital Curator
Before you even hit that "Install" button, pause and become a critical digital curator. The app stores are vast, but not all apps are created equal when it comes to privacy. A little research goes a long way. Start by reading reviews, not just for functionality, but for any mentions of privacy concerns or excessive data collection. Check the developer's reputation; are they a well-known, trusted entity, or an obscure company with a generic name? Prioritize apps from reputable sources and, whenever possible, consider open-source alternatives, as their code is publicly auditable, offering greater transparency regarding data practices. Be particularly wary of "free" apps that seem to offer premium functionality without any obvious revenue model. If an app is truly free and powerful, its developers are likely monetizing it through your data, which is the hidden cost you're paying.
Another crucial step is to scrutinize the app's privacy policy, though I understand this can feel like reading legal jargon. While dense, some policies do offer clear statements about data collection and sharing. More recently, Apple has introduced "Privacy Nutrition Labels" in its App Store, which provide a quick, understandable overview of an app's data practices, detailing what data is collected and how it's used. Android has also been moving in a similar direction. Use these labels as a guide, but don't take them as gospel, as self-reporting can sometimes be less than perfectly accurate. When in doubt, err on the side of caution. If an app's data demands feel excessive for its stated purpose, or if its privacy policy is vague or non-existent, it's probably best to find an alternative. Your app choices are direct reflections of your privacy values, and choosing wisely is a powerful statement against pervasive data harvesting.
Fortifying Your Network with a Digital Cloak Using VPNs and Secure Browsers
Beyond app permissions, your network activity itself generates a wealth of metadata that can be exploited. This is where a robust Virtual Private Network (VPN) becomes an indispensable tool. A VPN encrypts your internet traffic and routes it through a server operated by the VPN provider, effectively masking your IP address and making your online activities much harder to trace back to you. When choosing a VPN, prioritize a reputable "no-logs" provider, meaning they don't keep records of your online activities. Look for strong encryption standards (like AES-256) and a clear, audited privacy policy. Using a VPN, especially when connected to public Wi-Fi networks, is non-negotiable. Public Wi-Fi is inherently insecure, making your data vulnerable to interception by anyone on the same network. A VPN acts as your personal digital cloaking device, protecting your browsing history, your communications, and your overall online identity from prying eyes.
Complementing a VPN, consider adopting privacy-focused browsers and search engines. Browsers like Brave, Firefox Focus, or DuckDuckGo are designed with privacy in mind, often blocking trackers, third-party cookies, and intrusive ads by default. DuckDuckGo, for instance, is a search engine that explicitly promises not to track your searches or build a profile of your interests, a stark contrast to the data-hungry practices of mainstream search providers. Furthermore, ensure your browser is configured to use secure DNS over HTTPS (DoH) or DNS over TLS (DoT), which encrypts your DNS queries, preventing your ISP or other entities from seeing which websites you're trying to access. These combined network-level protections create a formidable barrier against pervasive tracking, making it significantly harder for apps and websites to build a comprehensive profile of your online behavior, thus safeguarding your digital footprint from those who seek to exploit it.
Device Settings and Updates Building a Stronger Digital Foundation
Your phone's operating system and settings offer a multitude of privacy controls that are often overlooked. Regularly updating your OS and all your apps is paramount. Software updates frequently include security patches that fix vulnerabilities which could otherwise be exploited by malicious apps to gain unauthorized access to your data or sensors. Enabling strong passwords or passcodes for your device, along with multi-factor authentication (MFA) wherever available, adds crucial layers of security, making it much harder for unauthorized individuals to access your device and its contents, even if they somehow get hold of your login credentials.
Dive into your phone's privacy settings. On iOS, you can enable "App Tracking Transparency" (ATT), which forces apps to ask for your permission before tracking your activity across other companies’ apps and websites. This single feature has had a massive impact on the advertising industry, empowering users to opt out of cross-app tracking. On Android, you can reset your advertising ID periodically, which makes it harder for advertisers to link your activities across different apps. Ensure your device is encrypted, a standard feature on most modern smartphones, which scrambles your data, making it unreadable without your passcode. Disable features you don't use, like NFC or Bluetooth, when not needed, as these can sometimes be vectors for data collection or exploitation. These seemingly small adjustments to your device settings collectively build a much stronger digital foundation, reducing the attack surface for data theft and enhancing your overall privacy posture.
Cultivating Digital Hygiene Habits A Lifestyle of Awareness
Ultimately, protecting your privacy in the digital age requires more than just technical fixes; it demands a shift in mindset and the adoption of mindful digital hygiene habits. Regularly review and delete old apps you no longer use. Each app, even dormant ones, represents a potential data leak or an outdated permission you might have forgotten about. Clear your browser cache and cookies periodically to remove tracking data. Practice the principle of least privilege: only grant apps the minimum permissions absolutely necessary for their core function. Be skeptical of every permission request and question its necessity. Use unique, strong passwords for every online service, ideally managed by a reputable password manager, to prevent credential stuffing attacks from compromising multiple accounts if one service is breached.
Perhaps most importantly, cultivate an ongoing awareness of what you share online. Every post, every photo, every comment contributes to your digital footprint. Think before you share, especially when it comes to sensitive personal information. Educate yourself and those around you about these threats; privacy is often a collective effort. The landscape of online privacy is constantly evolving, with new threats and new defenses emerging regularly. Staying informed about the latest cybersecurity news and privacy best practices is not just for tech enthusiasts; it's a fundamental responsibility for anyone who carries a smartphone. By adopting these habits, you transform from a passive data subject into an active guardian of your digital self, making it significantly harder for unseen forces to turn your indispensable device into a tool for covert surveillance and data exploitation. Your phone might be listening, but with knowledge and action, you can make sure it hears only what you choose to tell it, reclaiming your digital autonomy one careful tap at a time.