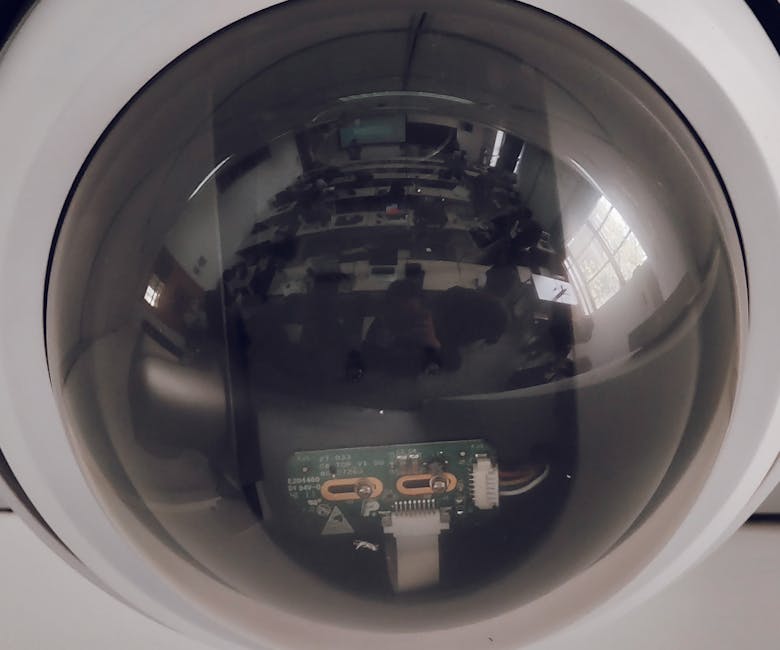
More Than Just Ads: The Grim Realities of Constant Surveillance
While targeted advertisements are often the most visible and annoying consequence of our phones constantly listening, the implications of pervasive surveillance extend far beyond mere commercial nudges. The grim realities of having an always-on digital ear in your pocket delve into fundamental questions of personal autonomy, security, and the very nature of privacy in an increasingly connected world. We’re not just talking about seeing an ad for that obscure gadget you mentioned; we’re talking about the erosion of trust, the potential for exploitation, and the chilling effect on free expression. This isn't just an inconvenience; it's a systemic shift in how our personal information is gathered, used, and potentially abused, fundamentally altering our relationship with technology and with each other.
Consider the cumulative effect of having every aspect of your life digitized and analyzed. Your location data reveals your daily routines, your social interactions expose your network, and your spoken words hint at your deepest thoughts and vulnerabilities. When all this information is aggregated, it creates an incredibly detailed and intimate profile, a digital doppelgänger that knows more about you than you might even know about yourself. This comprehensive profile, built on a foundation of continuous data streams, becomes a powerful tool that can be wielded for various purposes, not all of them benign. It shifts the power dynamic significantly, placing immense control in the hands of those who possess and analyze this data, whether they are corporations seeking profit or more malicious actors seeking leverage.
The normalization of this constant monitoring also desensitizes us to its dangers. What once seemed futuristic and alarming is now accepted as the price of convenience, a shrug-worthy feature of modern life. This complacency is perhaps the greatest danger, as it allows the boundaries of privacy to be pushed further and further without significant public outcry or regulatory intervention. The long-term societal impact of living in a world where private conversations are always potentially overheard, where every action is logged, and every preference is cataloged, is profound. It can lead to a society where genuine spontaneity and unfiltered expression are stifled, replaced by a cautious self-awareness that constantly considers the digital audience, even in the most private moments. This isn't just about ads; it's about the fundamental right to an unobserved life.
When Your Data Falls into the Wrong Hands: The Breach Beyond Your Bubble
The collection of vast quantities of personal data, including sensitive audio information, inherently creates a massive security risk. Every piece of data stored on a server, no matter how well-protected, represents a potential target for cybercriminals, state-sponsored actors, and malicious insiders. When your conversations, preferences, and even emotional states are captured and stored, the stakes of a data breach skyrocket. It’s no longer just about compromised credit card numbers; it’s about the exposure of your most intimate details, the breach extending far beyond your personal digital bubble and potentially impacting your real-world safety, financial stability, and emotional well-being.
Imagine the consequences if a database containing recordings of your private conversations, perhaps discussing sensitive health issues, financial struggles, or personal relationships, were to be leaked. This isn't theoretical; we've seen countless data breaches expose everything from medical records to private messages. If audio data is part of the trove, the potential for identity theft becomes more sophisticated, as voice biometrics could be compromised. Beyond that, the information gleaned from such recordings could be used for highly targeted phishing scams, blackmail, or even real-world stalking. The value of such deeply personal data to criminals is immense, offering avenues for exploitation that go far beyond what a stolen password might enable.
Furthermore, the aggregation of data from multiple sources amplifies the risk. Even if a single app only collects seemingly innocuous audio snippets, when combined with your location data from another app, your browsing history from yet another, and your social media activity, a powerful and exploitable profile emerges. This is the reality of the data broker industry, where information is bought, sold, and traded, often without your direct knowledge or consent. A breach at one of these brokers could expose a comprehensive dossier of your life, including insights derived from your spoken words, making you vulnerable to a wide array of sophisticated attacks. The breach beyond your bubble isn't just a hypothetical concern; it's a persistent, looming threat that underscores the critical importance of minimizing data collection at every possible turn.
The Chilling Effect: How Constant Monitoring Changes Who You Are
The insidious nature of constant digital monitoring isn't just about the immediate threat of targeted ads or data breaches; it's about the profound psychological impact, often referred to as the "chilling effect." When individuals feel that their conversations, actions, and even thoughts are subject to perpetual surveillance, whether by algorithms or human reviewers, it subtly yet significantly alters their behavior. This isn't an overt, conscious decision to self-censor, but rather a subconscious shift, a gradual erosion of spontaneity and genuine expression, replaced by a cautious, curated persona, even in supposedly private spaces. This chilling effect can fundamentally change who you are, how you interact with others, and how you perceive your own autonomy.
Think about the freedom of speaking openly, without filters, about controversial topics, personal struggles, or even just silly, private jokes. In a world where your phone is perceived as constantly listening, that freedom diminishes. You might find yourself pausing before discussing sensitive topics, opting for text messages over spoken words, or even leaving your phone in another room during important conversations. This isn't just about protecting your privacy from corporations; it's about protecting the integrity of your personal relationships and the authenticity of your self-expression. The constant awareness of potential surveillance can lead to a state of hyper-vigilance, where every utterance is weighed, every opinion considered in the context of how it might be interpreted or used by unseen algorithms, or worse, by human agents.
This self-censorship can extend beyond spoken words to broader aspects of your life. If you know your location is constantly tracked, you might avoid certain places or activities. If your browsing history is logged, you might shy away from researching sensitive topics. The cumulative impact is a narrowing of your personal space and a reduction in your willingness to explore, experiment, or express yourself authentically. Dr. Evelyn Reed, a prominent digital ethics researcher, once articulated this beautifully:
"When the walls of privacy crumble, so too does the courage to truly be oneself. The chilling effect isn't just about data; it's about the slow suffocation of human spontaneity and the erosion of the very essence of individual freedom."This profound observation underscores the critical importance of addressing pervasive digital surveillance, not just for the sake of data protection, but for the preservation of human spirit and genuine interaction in an increasingly monitored world.
The Murky Waters of Consent: Reading Between the Lines of Terms and Conditions
The cornerstone of data collection, at least in theory, is user consent. However, in practice, the concept of consent in the digital realm often navigates incredibly murky waters, leaving users confused, uninformed, and ultimately disempowered. We've all encountered those endless, jargon-filled "Terms and Conditions" and "Privacy Policies" that pop up when we install an app or sign up for a service. These documents, often hundreds or thousands of words long, are designed more for legal protection than for user comprehension, effectively creating a scenario where explicit consent is technically obtained, even if the user has absolutely no real understanding of what they've agreed to. This deliberate opacity is a major enabler of pervasive data collection, including the potential for microphone access and audio processing.
The language used in these documents is frequently vague and broad, allowing companies significant leeway in how they collect and utilize your data. Phrases like "to improve our services," "for personalized experiences," or "to deliver relevant advertising" can encompass a wide range of data collection activities, including the processing of audio inputs, without explicitly stating "we will listen to your conversations." This ambiguity is intentional, as it allows companies to operate within the letter of the law while circumventing the spirit of true informed consent. Users are left to guess at the specifics, or more commonly, to simply click "Accept" because the alternative is to forgo using the app or service altogether, a choice that feels increasingly impossible in our digitally integrated world.
Furthermore, consent often isn't a one-time event but an ongoing, evolving process. Policies can change, and new data collection methods can be introduced, often with a simple notification that users might easily overlook. The burden then falls on the user to constantly review and re-evaluate their permissions and the terms they've agreed to, a task that is impractical for most. This creates a power imbalance where the tech companies hold all the cards, setting the rules of engagement in a way that prioritizes their data needs over individual privacy. Until regulations mandate clearer, more concise, and truly comprehensible privacy policies, or until platform providers enforce stricter controls over app permissions, users will continue to navigate these murky waters of consent, unknowingly trading their privacy for convenience, one "Accept" button at a time.