The digital drawbridge is down, the portcullis rusted open, and the guards are… well, they’re still arguing about whether the moat needs more piranhas or just better signage. For years, we’ve been told that "Zero Trust" was the answer, the impenetrable fortress in a world teeming with cyber barbarians. It was the security mantra whispered in boardrooms, shouted in tech conferences, and dutifully implemented (or so we thought) across enterprises of all shapes and sizes. The promise was alluring: never trust, always verify. Every user, every device, every application, every connection – scrutinized, authenticated, and authorized, no matter where it originated. It was supposed to eliminate the dangerous assumption of trust within our network perimeters, effectively turning every access request into a skeptical interrogation. We bought into the vision, poured billions into solutions, and breathed a collective sigh of relief, believing our networks were finally secure.
But let’s be brutally honest with ourselves, looking past the glossy whitepapers and the enthusiastic vendor presentations: that dream, that seemingly ironclad defense, has largely crumbled. The stark reality is that despite the widespread adoption, or at least the *attempted* adoption, of Zero Trust principles, organizations are still getting breached with alarming regularity. We're talking about sophisticated, deeply impactful attacks that bypass layers of security, exfiltrate mountains of sensitive data, and disrupt critical operations, often from within what was supposed to be a "Zero Trust" environment. This isn't just a minor oversight; it's a fundamental disconnect between the theoretical ideal and the messy, complex, human-driven reality of network security. The emperor, it turns out, is wearing very few clothes, and our 'secure' networks are still, distressingly, an open door for those determined enough to walk through it.
The Folly of Trust and The Rise of a Misunderstood Messiah
Before Zero Trust became the industry's darling, the prevailing security model was largely perimeter-based. Think of it like a medieval castle: strong outer walls, a moat, and heavily guarded gates. Once inside, however, anyone was generally assumed to be safe and could move relatively freely. This worked reasonably well when applications and data resided almost exclusively within an organization's physical data center, and users primarily accessed resources from company-issued devices on the corporate network. You built a firewall, set up intrusion detection, and felt reasonably secure. The problem, as we all painfully discovered, was that once an attacker managed to breach that outer wall – perhaps through a phishing email, a compromised laptop, or an unpatched vulnerability – they had free rein. They could move laterally, escalate privileges, and explore the network at their leisure, often undetected for months. This "trust but verify" (or often, "trust implicitly once inside") model was a catastrophic failure in the face of an increasingly sophisticated threat landscape, especially with the advent of cloud computing, remote work, and mobile devices.
The concept of Zero Trust emerged from this crucible of failure, championed most notably by Forrester Research in 2010. Its core tenets were revolutionary at the time: assume breach, verify explicitly, and enforce least privilege access. Instead of a single, hard outer shell, Zero Trust proposed a granular, segment-of-one approach where every single access request, regardless of origin, was treated as if it were coming from an untrusted network. This meant continuous authentication, authorization, and validation of users, devices, applications, and data flows. It was an elegant solution to a growing problem, promising to confine breaches, prevent lateral movement, and drastically reduce the attack surface. For many, it represented a paradigm shift, a necessary evolution from a failing model to one that finally acknowledged the brutal realities of modern cyber warfare. The industry embraced it with open arms, eager for a fresh narrative and a new set of tools to combat the relentless tide of digital threats.
The Dangerous Illusion of the "Zero Trust Product"
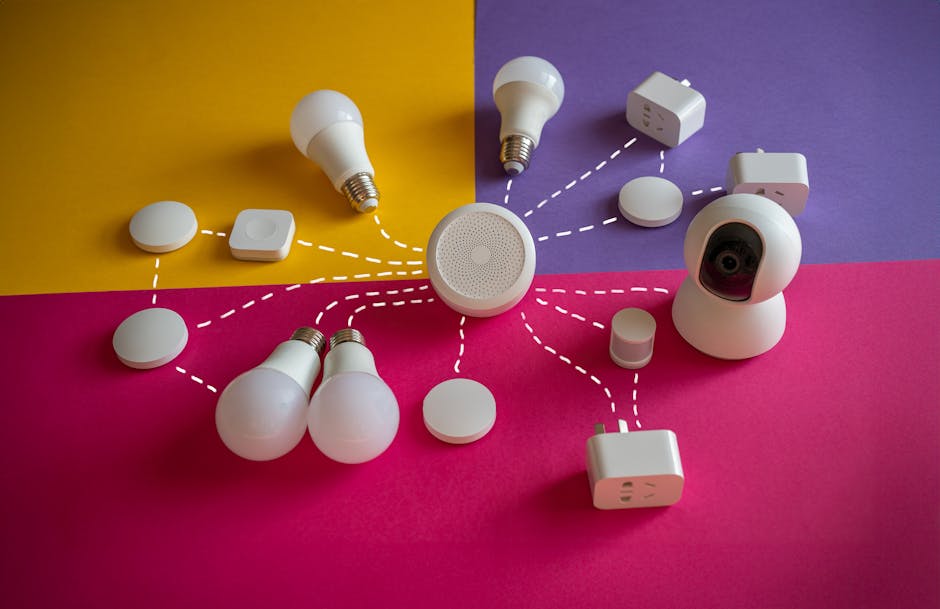
One of the most significant pitfalls that led to the current state of disillusionment with Zero Trust is the pervasive misconception that it is a product you can simply buy, install, and check off a compliance box. Vendors, ever eager to capitalize on market trends, quickly rebranded their existing tools – firewalls, identity providers, network access controls, endpoint detection and response solutions – as "Zero Trust ready" or "Zero Trust solutions." This created a dangerous illusion for many organizations, particularly those with limited cybersecurity budgets or expertise. They would invest in a shiny new piece of software, perhaps a next-gen firewall or a sophisticated identity management system, and declare their network "Zero Trust compliant." The reality, however, is far more complex and nuanced. Zero Trust is not a single technology; it's a strategic framework, a philosophical approach to security design and operations that permeates every layer of an organization's digital infrastructure. It requires a fundamental shift in thinking, a comprehensive overhaul of policies, processes, and technologies working in concert, rather than a standalone purchase.
This "product-centric" view often leads to fragmented implementations where organizations deploy a few Zero Trust-labeled tools without integrating them effectively or aligning them with the overarching principles. They might implement strong multi-factor authentication (MFA) for user logins, which is indeed a critical component, but then fail to apply least-privilege principles to application access or neglect micro-segmentation within their cloud environments. The result is a patchwork of controls that might look good on paper but leaves significant gaps for attackers to exploit. Imagine trying to build a secure castle by simply buying a stronger gate, but leaving the back wall crumbling and the windows unlocked. It’s an incomplete and ultimately ineffective strategy. The true power of Zero Trust lies in its holistic application, where every component of the security architecture reinforces the "never trust, always verify" ethos. Without this integrated approach, these standalone "Zero Trust products" often become little more than expensive window dressing, providing a false sense of security while the underlying vulnerabilities persist, ready to be exploited.