Remember that fleeting moment of joy, the sheer delight when you first unboxed your new smart speaker, the sleek lines of your smart TV, or the reassuring glow of your smart thermostat? It felt like stepping into the future, a seamless world where technology anticipated your needs, managed your home, and simplified your life. We embraced these gadgets with open arms, eager for the convenience they promised, often overlooking the fine print, the hidden permissions, and the silent, ever-present question lurking beneath their polished surfaces: what if this marvel of modern engineering isn't just listening to commands, but actively listening to everything else? What if the devices we invite into our most intimate spaces are not just helpful assistants but unwitting accomplices in a grand, often insidious, game of digital surveillance? It’s a chilling thought, isn't it, that the very tools designed to make our lives easier could be subtly, systematically, and relentlessly gathering data about our habits, our conversations, even our deepest secrets, turning our homes into unwitting data mines for corporations, advertisers, and, potentially, far more malicious entities?
For over a decade, I’ve been immersed in the labyrinthine world of online privacy and cybersecurity, witnessing firsthand the relentless cat-and-mouse game between those who build our digital future and those who seek to exploit its vulnerabilities. What started as a trickle of connected devices has exploded into an avalanche, with billions of Internet of Things (IoT) gadgets now permeating every facet of our existence, from smart toothbrushes to industrial control systems. This exponential growth, while undeniably transformative, has created a sprawling, interconnected web teeming with security gaps, backdoors, and design flaws that are often overlooked by manufacturers in their rush to market, and tragically, ignored by us, the end-users, in our pursuit of convenience. The truth is, many of these devices, from the moment they connect to your Wi-Fi, become potential portals into your private life, broadcasting details about your routines, your preferences, and even your physical presence to an unseen audience, transforming the very concept of "home" from a sanctuary into a meticulously monitored showroom.
The Silent Sentinels in Your Living Room
Take a moment to look around your home. How many devices are connected to your internet? Your smart TV, perhaps a streaming stick, a security camera, a voice assistant, a smart thermostat, maybe even a smart refrigerator or a robotic vacuum cleaner. Each one of these is a tiny computer, equipped with sensors, microphones, cameras, and network connectivity, all designed to make your life smoother. But this functionality comes at a price, often paid in the currency of your personal data and, disturbingly, your security. These devices, innocent as they may seem, are often built with minimal security protocols, making them incredibly attractive targets for cybercriminals, data brokers, and even state-sponsored actors seeking to gain a foothold in your network, not just to steal your identity, but to paint an incredibly detailed picture of your life, your habits, and your vulnerabilities.
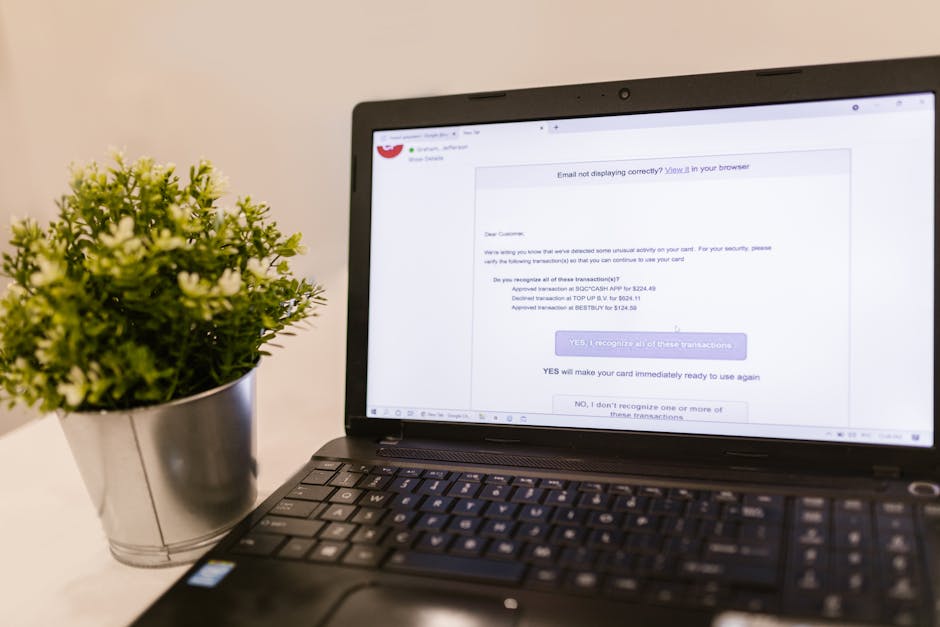
The problem isn't just theoretical; it's a stark, unsettling reality playing out in homes across the globe every single day. We've seen countless reports of smart cameras being hacked, allowing strangers to peer into nurseries and bedrooms, or even speak directly to children through the device's two-way audio. Smart speakers, designed to respond to a wake word, have sometimes been found to record conversations even when not actively prompted, sending snippets of private dialogue back to corporate servers for "analysis" or "improvement." My own experience, digging through privacy policies and network traffic logs, has revealed just how aggressively some of these devices vacuum up data, often far more than is necessary for their stated function. It's a digital land grab, and your personal information is the most valuable commodity being plundered, often without your explicit, informed consent, leaving you exposed in ways you might not even begin to imagine.
The sheer scale of this issue is staggering. Industry analysts estimate that by 2025, there will be over 27 billion IoT devices worldwide, each one a potential entry point for an attacker. Many of these devices are manufactured by companies with little to no cybersecurity expertise, prioritizing low cost and quick deployment over robust protection. They often ship with default passwords like "admin" or "12345," unpatched vulnerabilities that are common knowledge among hackers, and insecure communication protocols that broadcast your data in plain text, making it child's play for someone with even rudimentary technical skills to intercept and exploit. It’s a ticking time bomb in many households, and the fuse is burning faster than most people realize, threatening not just individual privacy but the very integrity of our connected infrastructure, from smart cities to critical utilities.
The Unseen Hand of Data Collection
What exactly are these devices collecting? The answer is often far more comprehensive and invasive than you might expect. Your smart TV, for instance, isn't just displaying your favorite shows; it might be tracking every channel you watch, every app you open, and how long you spend on each. It could be listening for voice commands and, in some cases, even passively listening to background conversations to "improve" its advertising targeting. Your smart vacuum cleaner isn't just cleaning your floors; it's mapping your home's layout, identifying furniture, and potentially even detecting the presence of people, all of which constitutes incredibly sensitive data about your living space and daily routines. This isn't just about targeted ads; it's about building comprehensive profiles of individuals and households, profiles that can be bought, sold, and misused in ways that extend far beyond simple marketing, venturing into the realm of social engineering and even physical security risks.
The insidious nature of this data collection lies in its often-invisible operation. Unlike a website that asks for cookie consent, many IoT devices simply start collecting data from the moment they're powered on and connected. The terms of service, if you bothered to read them (and let's be honest, who truly reads those endless legal disclaimers?), often grant the manufacturer broad rights to collect, store, and share your data with third parties. This creates a vast ecosystem of data brokers, advertisers, and analytics firms that feast on the digital crumbs left by your smart devices, piecing together an incredibly detailed mosaic of your life. Imagine a scenario where your health insurer knows exactly how many times you opened your smart fridge door for a late-night snack, or your smart bed tracks the quality of your sleep, influencing your premiums or even future medical care decisions. The implications are profound, touching upon issues of autonomy, discrimination, and the fundamental right to privacy in one's own home.
"The biggest risk with IoT devices isn't just what they can do, but what they reveal about us. Every connected gadget becomes a data point, contributing to an ever-growing digital dossier that paints a complete picture of our lives for anyone willing to pay for it." – A leading cybersecurity analyst.
The urgency of addressing these vulnerabilities cannot be overstated. We are not just talking about minor inconveniences or spam emails. We are talking about potential vectors for sophisticated cyberattacks, identity theft, financial fraud, and even physical harm. A compromised smart lock could grant an intruder access to your home. A hacked baby monitor could turn into a tool for child predators. An exploited smart medical device could literally endanger a patient's life. The interconnectedness that brings us convenience also brings unprecedented risks, and our collective ignorance or apathy towards these dangers is, frankly, alarming. It’s time to pull back the curtain on these digital spies and arm ourselves with the knowledge and tools necessary to reclaim our privacy and secure our smart homes, transforming them from vulnerable targets back into the safe havens they were always meant to be, and thankfully, many of these crucial steps can be taken in a surprisingly short amount of time, giving you back a significant measure of control.
This article is not just a warning; it's a call to action, a comprehensive guide to understanding the profound privacy and security implications of your smart devices and, crucially, a roadmap to fortifying your digital perimeter. We will delve deep into the most common vulnerabilities, explore real-world examples of devastating breaches, and, most importantly, provide you with clear, actionable steps that you can implement, many of them in a matter of minutes, to transform your smart home from a potential surveillance hub into a bastion of security and privacy. You've embraced the future; now it's time to secure it, understanding that the convenience of smart technology should never come at the expense of your fundamental right to privacy and safety within your own four walls. The journey to a more secure smart home begins with awareness, and that awareness starts right here, right now, as we peel back the layers of marketing hype to reveal the stark realities of our connected world.
We’ve all been there: excitedly unboxing a new smart gadget, plugging it in, connecting it to the Wi-Fi, and then, with a satisfied sigh, moving on to enjoy its features. The setup process is usually designed to be as frictionless as possible, often requiring little more than a few taps on a smartphone screen. This ease of use, however, frequently comes at a significant cost to security, a cost that is rarely transparent until it’s too late. The very design philosophy that prioritizes user experience above all else often leaves gaping holes in the digital defenses of these devices, turning them into low-hanging fruit for anyone with malicious intent. It’s a paradox of modern technology: the simpler something is to set up, the more likely it is to harbor hidden dangers, making it imperative for us, the users, to become proactive guardians of our own digital ecosystems, rather than relying solely on manufacturers who often have conflicting priorities.
Unmasking the Digital Wiretappers: Common Vulnerabilities Exploited
The landscape of IoT security vulnerabilities is vast and varied, but certain weaknesses appear with alarming regularity, making them prime targets for exploitation. These aren't obscure, highly sophisticated flaws; rather, they are often fundamental security oversights that continue to plague even the latest smart devices. Understanding these common chinks in the armor is the first crucial step towards building a more resilient digital defense for your home. It’s not about being a cybersecurity expert, but about recognizing the patterns of negligence that leave so many devices exposed, allowing us to take simple, yet profoundly effective, countermeasures that can make a world of difference in safeguarding our personal information and our privacy from prying eyes and nefarious actors, both corporate and criminal, looking to exploit these easily identifiable weaknesses for their own gain.
One of the most persistent and frustrating vulnerabilities is the widespread use of weak, default, or easily guessable passwords. It sounds almost comically amateurish in an age of advanced cyber threats, yet countless IoT devices still ship with generic login credentials like "admin/admin," "user/password," or even no password at all. Many users, understandably, never bother to change these defaults, either because they're unaware of the risk, find the process cumbersome, or simply forget. This negligence creates an open invitation for hackers. Automated bots constantly scan the internet for devices using these well-known default credentials, and once found, they can gain full control in seconds, turning your smart camera into a surveillance tool for strangers or enrolling your smart speaker into a botnet without you ever knowing. It's a fundamental security lapse that continues to underpin a disturbing number of IoT breaches, proving that sometimes, the simplest weaknesses are the most devastatingly effective, because they prey on human oversight and convenience.
Beyond default passwords, the issue of unpatched firmware and software vulnerabilities looms large. Just like your computer or smartphone, IoT devices run on software – often referred to as firmware. This firmware, inevitably, contains bugs and security flaws that are discovered over time. Reputable manufacturers release updates to patch these vulnerabilities, but many IoT devices either don't receive regular updates, or the update process is so convoluted that users simply don't bother. This leaves devices permanently exposed to known exploits, essentially like leaving your front door unlocked after the police have issued a public warning about a surge in burglaries in your neighborhood. The infamous Mirai botnet, for example, primarily leveraged known vulnerabilities in unpatched IoT devices, specifically insecure telnet ports and default credentials, to create a massive network of compromised cameras and DVRs that then launched devastating denial-of-service attacks against major websites, demonstrating the cascading impact of such seemingly minor oversights.
The Perilous Path of Insecure Data Transmission and Storage
Imagine sending your most sensitive personal information – your health data from a fitness tracker, your voice commands to a smart assistant, or live video feeds from your security camera – across the internet in a plain, unencrypted format, like shouting it across a crowded room. That's essentially what happens with many IoT devices due to insecure data transmission and storage practices. Data in transit should always be encrypted using robust protocols like TLS (Transport Layer Security) to prevent eavesdropping. However, many manufacturers, again prioritizing cost and speed over security, fail to implement proper encryption, or they use outdated, easily breakable encryption methods. This means that anyone with access to your local network, or even someone on a public Wi-Fi network if your device connects insecurely, could potentially intercept and read the data your devices are sending and receiving, gaining access to incredibly intimate details of your life without your knowledge.
Furthermore, the way data is stored, both locally on the device and on cloud servers maintained by the manufacturer, often presents another critical vulnerability. If the data stored on the device itself isn't encrypted, a physical breach could expose sensitive information. More commonly, however, the problem lies with the cloud infrastructure. Many IoT companies are not cybersecurity specialists; they are product developers. Their cloud servers might be poorly configured, lack proper access controls, or fall victim to their own software vulnerabilities, leading to massive data breaches. We've seen numerous instances where databases containing user IDs, passwords, and even personal recordings from smart devices were left exposed on the internet, accessible to anyone who knew where to look. This isn't just a hypothetical threat; it's a recurring nightmare for privacy advocates and a goldmine for identity thieves, who can piece together fragments of your digital life from various breaches to construct a complete profile.
Another often-overlooked area of concern is the lack of proper authentication and authorization mechanisms. Beyond just login credentials, many IoT devices don't adequately verify the identity of users or other devices attempting to interact with them. This can lead to various attacks, such as impersonation, where an attacker pretends to be a legitimate device or user to gain unauthorized access. For example, some smart home hubs might not properly authenticate commands, allowing an attacker who has gained a foothold in your local network to send commands to your smart lights, locks, or other connected appliances without proper verification. This vulnerability extends to API (Application Programming Interface) security as well. Many IoT devices rely on APIs to communicate with companion apps and cloud services. If these APIs are poorly secured, they can be exploited to bypass authentication, extract data, or even control devices remotely without ever needing to guess a password. It's a sophisticated attack vector that leverages the underlying architecture of interconnected systems, making it particularly dangerous because it bypasses the more obvious security measures.
"The rush to market has left a gaping hole in IoT security. Manufacturers prioritize features and cost over fundamental safety, leaving consumers to bear the brunt of insecure design choices. It's a digital Wild West, and our personal data is the bounty." – Dr. Evelyn Reed, Cybersecurity Ethicist.
Finally, we cannot ignore the pervasive issue of supply chain risks in IoT manufacturing. The journey of a smart device from concept to your living room is incredibly complex, often involving components and software from dozens of different suppliers across the globe. Each link in this supply chain represents a potential point of compromise. A malicious actor could inject malware into a component during manufacturing, or a vendor could inadvertently use insecure third-party libraries in their software. This "Trojan horse" approach means that a device could arrive in your home with pre-existing vulnerabilities or backdoors, completely unbeknownst to the manufacturer or the end-user. The opaque nature of global supply chains makes auditing these risks incredibly difficult, creating a fertile ground for sophisticated, nation-state level attacks that can compromise devices before they even leave the factory floor. This level of compromise is particularly insidious because it's almost impossible for the average consumer to detect or mitigate, highlighting the systemic challenges we face in securing our increasingly interconnected world, where trust must be placed in a long chain of anonymous entities.
These vulnerabilities are not isolated incidents; they are systemic problems baked into the very fabric of the IoT ecosystem. They represent a fundamental disconnect between the rapid pace of technological innovation and the often-slower, more deliberate process of implementing robust security standards. As consumers, we are often left holding the bag, unknowingly exposing ourselves to risks that could have been mitigated with better design and more stringent security practices from the outset. But understanding these common pitfalls is the first major step towards empowering ourselves. Knowledge is power, and in the realm of cybersecurity, it's the most effective shield you have against the unseen forces that seek to exploit your connected world. By being aware of these weaknesses, we can begin to take proactive measures, transforming ourselves from passive victims into active participants in the defense of our digital lives, ensuring that our smart devices serve us, rather than inadvertently serving as spies for others, turning our convenience into a dangerous liability that could have far-reaching and deeply personal consequences.
The sheer volume of data collected by our smart devices is staggering, often far exceeding what's necessary for their advertised functions. This data isn't just ephemeral digital dust; it's a rich, detailed tapestry woven from the threads of your daily life. Every interaction, every command, every movement, every environmental change detected by your smart gadgets contributes to an ever-expanding profile of who you are, what you do, and even how you feel. This isn't some dystopian future scenario; it's the present reality, quietly unfolding within the walls of our homes, turning our most private spaces into bustling data factories. The implications of this pervasive data harvest extend far beyond targeted advertisements, touching upon fundamental questions of privacy, autonomy, and the very definition of personal space in an increasingly connected world that constantly demands more and more information from us, often without truly explaining the depth and breadth of what is being taken.
The Data Harvest: What Your Devices Are Really Collecting and Why It Matters
Let's peel back the layers and examine the true extent of the data vacuum. It's not just about what you explicitly tell your smart speaker; it's about the ambient information, the inferences, and the sheer volume of incidental details that are constantly being logged. This data, once collected, rarely stays within the confines of your device or even the manufacturer's secure servers; it often embarks on a complex journey through a network of third-party partners, advertisers, and data brokers, each adding another piece to the puzzle of your digital identity. Understanding the types of data being collected and the ecosystem that profits from it is crucial to grasping the true scope of the privacy challenge posed by our smart homes, shifting our perspective from one of passive acceptance to active, informed concern about the invisible hands that are constantly sifting through the digital detritus of our daily lives.
The most obvious categories of data collected are voice, video, and location. Your smart speaker, with its always-on microphone, is designed to listen for wake words, but its capabilities extend far beyond that. Researchers have repeatedly demonstrated that these devices can pick up snippets of background conversations, even when not actively invoked, which are then sent to the cloud for processing. While manufacturers claim these are only used to "improve service," the potential for abuse and unintended exposure of private discussions is immense. Similarly, smart cameras, whether for security or baby monitoring, capture high-definition video feeds of your home, often uploading them to cloud storage. While the primary purpose is security, the potential for unauthorized access by hackers or even employees of the service provider raises serious privacy concerns. Imagine a stranger peering into your living room or a data analyst reviewing footage of your intimate family moments. This isn't the stuff of science fiction; it's a documented reality, reminding us that every lens and every microphone in our homes is a potential gateway for unwanted intrusion.
Beyond the sensory data, your devices are also voraciously collecting biometrics and usage patterns. Fitness trackers monitor your heart rate, sleep cycles, steps taken, and even skin temperature, creating a detailed health profile. Smart beds track your movements, breathing, and sleep stages. While this data offers personalized health insights, it's incredibly sensitive. What happens if this data is breached or sold to health insurance companies, potentially impacting your premiums or access to care? Furthermore, every smart device tracks your usage patterns: when you turn lights on and off, what temperature you prefer, which doors are locked or unlocked, what appliances you use and when. This seemingly innocuous data can be aggregated to build a remarkably accurate profile of your daily routines, your presence or absence from home, and even your lifestyle choices. This level of granular insight is a goldmine for targeted advertising, but also a significant security risk, as it could be used by criminals to determine optimal times for a break-in or by unscrupulous entities for social engineering attacks, turning your predictable habits into exploitable vulnerabilities.
The Invisible Hands: Who is Collecting and How They Profit
So, who exactly is harvesting all this incredibly personal data? The immediate answer is the device manufacturers themselves. They collect data to "improve" their products, offer personalized services, and troubleshoot issues. However, the ecosystem extends far beyond the original vendor. A complex web of advertisers, data brokers, and analytics firms are often granted access to, or purchase, this data. Manufacturers frequently embed third-party trackers and software development kits (SDKs) into their devices and companion apps, allowing these external entities to collect data directly. Data brokers then aggregate this information from various sources – your smart devices, your online browsing, your social media, public records – to construct incredibly detailed profiles, which they then sell to anyone willing to pay, from marketing companies to political campaigns, and sometimes, even less scrupulous actors.
The monetization of your personal data is a multi-billion-dollar industry, and your smart devices are key contributors to this revenue stream. The data collected from your smart TV, for instance, might be used to serve you highly specific ads across all your devices, based on your viewing habits. Your location data from a smart security camera's app could be sold to retail analytics companies to understand foot traffic patterns. The true value of this data lies in its ability to predict behavior and influence decisions. It's not just about selling you a product; it's about understanding your vulnerabilities, your preferences, and your routines with a level of detail that was unimaginable just a decade ago. This deep understanding can then be leveraged for highly persuasive, and sometimes manipulative, purposes, eroding your free will and autonomy in subtle, often undetectable, ways.
"We're living in a world where data is the new oil, and our smart homes are the wells. Every device is a drill, extracting valuable insights about our lives, often without our explicit knowledge or consent, fueling an industry built on profiling and prediction." – Privacy Advocate and Tech Journalist.
Beyond commercial exploitation, the specter of government surveillance also looms. In many jurisdictions, law enforcement agencies can compel manufacturers to hand over data from smart devices, often without requiring a warrant, particularly in cases involving national security or serious crime. While the intent might be to protect public safety, the potential for overreach and the erosion of civil liberties is a constant concern. Imagine your smart speaker recordings being used as evidence in a legal dispute, or your smart home's occupancy data being accessed by authorities without your knowledge. The line between legitimate investigation and pervasive surveillance becomes increasingly blurred when every aspect of your private life is being digitally documented and stored by third parties, creating a chilling effect on free expression and the fundamental right to be left alone in one's own home, a sanctuary that is increasingly under digital siege.
The dark side of this data harvest extends to more nefarious uses as well. Compromised data, whether through breaches or insider threats, can be used for identity theft, blackmail, or even physical targeting. If a hacker gains access to your smart home data, they could learn your work schedule, when you're away from home, and even the layout of your house, making you a prime target for burglary. Intimate data from smart sex toys or health devices, if exposed, could lead to severe emotional distress, reputational damage, and even blackmail. The cumulative effect of these various data points, when stitched together, creates a remarkably accurate and exploitable digital avatar of you, a shadow self that lives in the cloud, constantly being analyzed, traded, and potentially weaponized against you. It's a sobering thought that the very technology designed to enhance our lives can, through its inherent vulnerabilities and aggressive data collection practices, inadvertently become the tools of our own undoing, turning our conveniences into catastrophic liabilities in the blink of an eye.
The implications of this pervasive data collection are not just theoretical; they manifest in real-world consequences that can range from unsettling invasions of privacy to outright physical danger. We've moved beyond the realm of simple data breaches; now, the very fabric of our daily lives, as recorded by our smart devices, is being exploited, revealing a disturbing truth: convenience, when unchecked by robust security and ethical data practices, can pave a direct path to catastrophe. The stories that emerge from the front lines of cybersecurity are not just cautionary tales; they are stark warnings, illustrating in vivid detail how easily our trust in technology can be betrayed, turning our supposed digital assistants into unwitting agents of chaos and compromise. It's a wake-up call, urging us to look beyond the sleek design and clever marketing, and truly understand the profound risks we invite into our homes with every new connected gadget, risks that can materialize in the most unexpected and devastating ways, often with long-lasting repercussions that extend far beyond the digital realm.
When Convenience Becomes a Catastrophe: Real-World Tales of IoT Breaches and Their Fallout
Let's delve into some of the most prominent and unsettling examples of IoT security failures, not to instill fear, but to underscore the very real and tangible dangers lurking in our interconnected world. These aren't isolated incidents; they represent systemic weaknesses that continue to plague the IoT ecosystem, affecting millions of devices and countless individuals. By examining these case studies, we can better appreciate the urgency of the problem and understand why proactive security measures are not just advisable, but absolutely essential in safeguarding our personal lives from malicious exploitation. Each story serves as a chilling reminder that the line between innovative convenience and outright vulnerability is often perilously thin, and that our digital footprint can have very real-world, sometimes terrifying, consequences, proving that the abstract concept of a "cyber attack" can manifest in deeply personal and invasive ways.
Perhaps one of the most widely cited examples of IoT weaponization is the Mirai Botnet. In 2016, this malicious software swept across the internet, infecting hundreds of thousands of insecure IoT devices, primarily IP cameras, DVRs, and routers, that were still using their default factory usernames and passwords. These compromised devices were then marshaled into a vast botnet, a network of zombie devices, which was subsequently used to launch massive Distributed Denial of Service (DDoS) attacks. One such attack famously took down significant portions of the internet, including major websites like Twitter, Netflix, PayPal, and CNN, by overwhelming their servers with traffic. The chilling aspect of Mirai was its simplicity: it didn't rely on zero-day exploits but rather on basic security negligence. It highlighted how easily everyday devices, meant to enhance our lives, could be repurposed into destructive digital weapons, demonstrating the profound collective vulnerability created by widespread user apathy towards fundamental security practices, and the devastating ripple effect that a single, easily exploited flaw can have across the entire digital landscape.
More recently, the rise of smart home security cameras has brought a new wave of privacy invasions. The Ring camera hacks became a particularly disturbing series of incidents, where attackers gained unauthorized access to Ring devices, often by exploiting weak or reused passwords. In numerous documented cases, strangers peered into homes, yelled at children through the cameras' two-way audio, harassed residents, and even made racist remarks. One family reported an intruder speaking to their 8-year-old daughter in her bedroom, while another had a hacker taunt them through their living room camera. These weren't sophisticated, targeted attacks by nation-states; they were often opportunistic exploits by individuals leveraging readily available tools and common password hygiene failures. The emotional distress and sense of violation experienced by victims were profound, shattering their sense of security within their own homes and revealing the deeply personal and terrifying consequences when digital vulnerabilities spill over into the physical world, turning a sense of safety into palpable fear and anxiety.
Beyond the Home: Intimate Data and Critical Infrastructure at Risk
The vulnerabilities extend beyond general surveillance to incredibly intimate and personal data. Consider the case of smart sex toys. In 2017, a popular smart vibrator was found to be collecting highly sensitive usage data, including vibration intensity and frequency, and transmitting it unencrypted to the manufacturer's servers. A class-action lawsuit followed, highlighting the egregious breach of privacy. The thought of such intimate data being stored, potentially breached, or even viewed by company employees is deeply unsettling. It underscores how devices designed for personal pleasure can become vectors for profound personal violation, demonstrating a shocking disregard for user privacy in the pursuit of data collection, regardless of how sensitive or private that data might be, ultimately eroding trust in technology designed for the most personal aspects of human life.
The realm of medical devices also presents a critical and life-threatening dimension to IoT vulnerabilities. Pacemakers, insulin pumps, and other connected health devices are increasingly common, offering life-saving monitoring and management. However, these devices have been found to contain serious security flaws. For instance, in 2017, the FDA issued a warning about St. Jude Medical pacemakers, identifying vulnerabilities that could allow hackers to remotely access and alter the devices, potentially leading to battery depletion or incorrect pacing. While no confirmed attacks occurred, the potential for malicious actors to directly endanger human life through compromised medical IoT is a chilling prospect. It highlights a category of IoT devices where security is not merely about privacy or property, but about life and death, demanding the absolute highest standards of cybersecurity, which are often, tragically, not met by manufacturers in their rush to market these innovative, yet potentially lethal, technologies.
"The true cost of convenience is often revealed only after a breach. We invite these devices into our lives for ease, but we rarely consider the catastrophic implications when that convenience is weaponized against us. The invisible hacks are often the most damaging, eroding trust and security from within." – Renowned Cybersecurity Strategist, speaking on IoT risks.
The risks escalate dramatically when we consider Industrial IoT (IIoT) attacks, which target critical infrastructure. Smart sensors and connected control systems are now integral to power grids, water treatment plants, manufacturing facilities, and transportation networks. A successful cyberattack on these systems could lead to widespread power outages, contamination of water supplies, industrial accidents, or severe economic disruption. The infamous Stuxnet worm, though predating the widespread use of IIoT, demonstrated the devastating potential of targeting industrial control systems. As our critical infrastructure becomes increasingly interconnected, the vulnerabilities inherent in poorly secured IoT devices pose a national security threat, making the need for robust, proactive cybersecurity measures not just a personal concern, but a matter of societal resilience and global stability, urging governments and industries to collaborate on securing these vital digital arteries that underpin modern life.
The "invisible" hacks are often the most insidious, as they involve data siphoning without any obvious signs of compromise. Your smart TV might be quietly collecting your viewing habits and selling them to advertisers, or your smart speaker might be sending snippets of your conversations to the cloud for "analysis," all without any overt indication that your privacy is being eroded. These subtle, persistent invasions of privacy, while not as dramatic as a direct hack, contribute to the vast data profiles that are built about us, enabling targeted manipulation and eroding our autonomy in ways we may never fully comprehend. The fallout from these incidents isn't always a headline-grabbing disaster; sometimes, it's a slow, steady bleed of personal information, leaving us vulnerable in a thousand tiny, imperceptible ways, gradually diminishing our digital sovereignty until we barely recognize the extent of the control we have lost, simply by embracing the shiny new gadgets that promised to make our lives easier, but quietly turned them into open books for anyone with the right tools and motivation.
These real-world examples paint a stark picture: the vulnerabilities in our smart devices are not abstract concepts or theoretical threats. They are concrete, exploitable flaws with tangible, often devastating, consequences for individuals, businesses, and even critical infrastructure. The lesson is clear: relying solely on manufacturers to secure our digital lives is a gamble we can no longer afford to take. We, as consumers, must become active participants in the defense of our own privacy and security, understanding that the convenience offered by these devices comes with a profound responsibility. The good news is that while the problem is vast, many of the most impactful solutions are surprisingly simple, requiring minimal effort but yielding significant improvements. It's time to move beyond passively hoping for the best and actively taking control, transforming our smart homes from potential spy hubs into fortified digital sanctuaries, ensuring that our technology serves us, rather than inadvertently exposing us to an array of threats that could very easily turn our everyday conveniences into deeply unsettling personal catastrophes.
The idea of our smart devices acting as unwitting spies can feel overwhelming, a problem too vast and complex for the average person to tackle. After all, we're not all cybersecurity experts, and deciphering arcane network protocols or understanding the intricacies of firmware vulnerabilities is hardly what we signed up for when we bought that shiny new smart gadget. However, the truth is far more empowering than you might think. While some advanced measures do require a bit more technical know-how, a significant portion of the most critical security improvements can be implemented quickly and easily, often in just a few minutes. It's about taking back control, understanding that you have the power to fortify your digital perimeter, and transforming your smart home from a potential open house for hackers into a well-guarded sanctuary. Don't let the complexity of the problem paralyze you; instead, focus on the actionable steps that can make an immediate and profound difference in your personal security posture, because reclaiming your digital privacy isn't just possible, it's surprisingly accessible if you know where to start and are willing to dedicate a few moments to the task, turning your initial fear into empowered action.
Reclaiming Your Digital Sanctuary: Actionable Steps to Fortify Your Smart Home in Minutes
You don't need to be a tech guru to significantly enhance the security and privacy of your smart home. Many of the most impactful changes are straightforward, requiring little more than a few clicks or a quick password update. Think of these as your digital deadbolts and alarm systems – basic, yet incredibly effective deterrents against most opportunistic attackers. The goal here isn't absolute, unbreachable security, which is often an impossible ideal, but rather to raise your security posture significantly, making you a much less attractive target and mitigating the most common and easily exploitable vulnerabilities. By implementing even a handful of these recommendations, you'll be taking a giant leap towards securing your digital life, ensuring that your smart devices work for you, not against you, and allowing you to enjoy the benefits of convenience without constantly looking over your digital shoulder, wondering who might be watching or listening, and what they might be doing with the intimate details of your daily existence, which are constantly being collected and processed by these omnipresent gadgets.
The absolute cornerstone of any robust cybersecurity strategy, and the easiest fix you can implement right now, is to create strong, unique passwords for every single device and account. This is not just for your Wi-Fi router, but for every smart camera, smart speaker, smart plug, and any associated app. Many IoT devices ship with default passwords like "admin" or "12345," which are public knowledge and prime targets for automated attacks. Change these immediately! Use a password manager to generate and store complex, unique passwords (a mix of uppercase, lowercase, numbers, and symbols, at least 12-16 characters long) for each device. This simple step alone can thwart the vast majority of opportunistic hackers who rely on default credentials or users reusing weak passwords across multiple services. If one of your accounts is breached, a unique password prevents that breach from cascading across all your other devices and services, acting as a crucial firewall between different aspects of your digital life, minimizing the damage of any single point of failure.
Next up, make regular firmware updates a non-negotiable part of your smart device maintenance routine. Just like your computer's operating system or smartphone apps, IoT devices receive software updates (firmware updates) that often include critical security patches. Manufacturers release these updates to fix newly discovered vulnerabilities that hackers could exploit. Ignoring these updates is like leaving known security holes unplugged. Most modern devices have an option within their companion app to check for and install updates; some even offer automatic updates, which you should enable if available. Make it a habit to check for updates monthly. This seemingly minor task is a powerful defense mechanism, closing known backdoors and ensuring your devices are running the most secure version of their operating software, staying one step ahead of the malicious actors who are constantly searching for outdated and vulnerable systems to exploit for their own nefarious purposes, whether it's data theft or weaponizing your devices.
Fortifying Your Network and Devices from Within
Consider network segmentation, specifically using VLANs (Virtual Local Area Networks) for your IoT devices. This might sound a bit technical, but many modern routers offer this functionality, or you can purchase a dedicated router that supports it. A VLAN allows you to create separate, isolated networks within your home. By putting all your IoT devices on their own dedicated "guest" or "IoT" network, you effectively quarantine them from your primary network where your computers, phones, and sensitive data reside. If an IoT device is compromised, the attacker gains access only to that isolated network, preventing them from easily jumping to your more critical devices. This creates a crucial barrier, limiting the blast radius of any potential breach and significantly enhancing your overall home network security. It's a proactive measure that, once set up, provides continuous protection without any ongoing effort, acting as a digital moat around your most valuable digital assets.
Another crucial step is to disable unnecessary features and permissions on your smart devices and their companion apps. Many devices come with features enabled by default that you might not need, such as remote access from outside your home, always-on microphones, or location tracking. Review the settings in each device's app and turn off anything that isn't essential for its core function. Similarly, be judicious with app permissions on your smartphone. Does your smart light bulb app really need access to your camera or contacts? Probably not. Limiting these permissions reduces the attack surface and minimizes the amount of data your devices can collect and transmit. It's about being intentional with your technology, ensuring that every feature and permission serves a genuine purpose, rather than simply accepting the default settings that often prioritize data collection and convenience over your fundamental right to privacy, giving you back a sense of control over what your devices are truly capable of doing.
"The biggest myth in IoT security is that it's someone else's problem. The reality is, you're the first and most critical line of defense. Simple, consistent actions can build a formidable shield around your digital life." – Cybersecurity Educator.
Regularly reviewing privacy settings is also paramount. Most smart devices and their associated cloud services have dedicated privacy settings sections within their apps or web portals. Take the time to explore these settings. Opt out of data sharing with third parties, disable personalized advertising, and review what data is being collected and stored. Some devices even allow you to delete past recordings or data logs. While it might feel like a chore, understanding and configuring these settings is vital for controlling your digital footprint. Remember, privacy policies and default settings are often designed to favor the company's data collection goals, not your personal privacy. It's up to you to actively configure them to reflect your comfort level, ensuring that the convenience of a smart device doesn't inadvertently turn into a constant, unconsented data harvest, allowing you to draw clearer boundaries around your personal information.
For those looking for an extra layer of protection, consider using a VPN (Virtual Private Network) for your router. A VPN encrypts all internet traffic flowing through your router, meaning every device connected to your home network, including your IoT gadgets, benefits from that encryption. This makes it significantly harder for anyone to snoop on your devices' communications, even if the devices themselves don't have robust encryption built-in. While setting up a VPN on your router requires a bit more technical expertise, many VPN providers offer detailed guides, and some routers are specifically designed for easy VPN integration. It's a powerful, blanket solution that protects all your connected devices simultaneously, creating an encrypted tunnel for all your home's internet traffic, effectively making your entire smart home a much more private and secure environment, shielding it from the prying eyes of ISPs, hackers, and data brokers who might otherwise be able to intercept your unencrypted data, turning your entire network into a fortress.
A Proactive Approach to Your Digital Existence
Finally, adopt a proactive mindset by auditing your devices and monitoring network traffic. Periodically ask yourself: Do I really need this smart device? What data is it collecting? Is it still receiving security updates? If a device is old, unpatched, or no longer supported by the manufacturer, it might be time to disconnect it or replace it. Additionally, tools exist (like network monitoring software or even some advanced routers) that can show you what devices are connected to your network and what data they are sending. While this requires a bit more technical curiosity, it empowers you to spot unusual activity or identify devices that are behaving suspiciously, giving you crucial insights into the digital conversations happening within your home, allowing you to detect unauthorized data transfers or attempts at communication with suspicious servers that might indicate a compromise.
When it's time to retire an old smart device, ensure you securely dispose of it. Simply deleting the companion app isn't enough. Perform a factory reset on the device to wipe any stored data, and if possible, physically destroy any storage components before discarding. This prevents your personal information from falling into the wrong hands if someone else acquires your old device. The goal is to leave no digital trace, ensuring that the intimate details of your life, once recorded by these devices, are not inadvertently passed on to strangers. Your digital life is an extension of your physical self, and just as you wouldn't leave personal documents lying around for anyone to find, you shouldn't treat your digital data with any less care, understanding that proper disposal is the final, crucial step in maintaining your privacy and preventing your past from becoming someone else's future exploitation. These steps, while seemingly minor individually, collectively build a formidable defense against the pervasive threats of the connected world, transforming your smart home from a potential spy hub into a truly secure and private sanctuary, empowering you to enjoy the benefits of technology without sacrificing your peace of mind or your fundamental right to privacy.