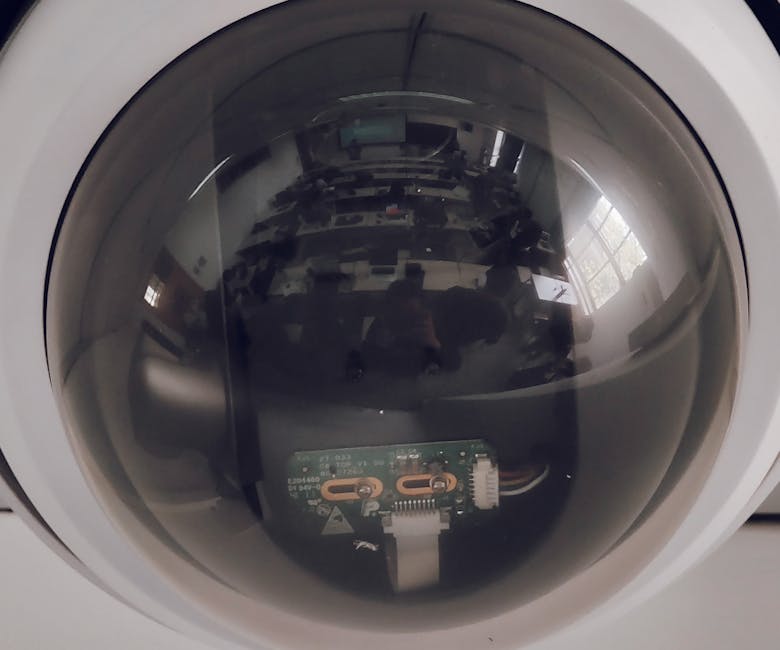
The data collected by our myriad smart devices, from the mundane to the deeply personal, doesn't simply vanish into the ether after being processed. It embarks on a complex journey through an intricate web of digital entities, each playing a specific role in the vast, multi-billion-dollar data economy. This is where the true scope of the AI privacy nightmare becomes chillingly apparent: it's not just about what your devices hear or see, but who ultimately gains access to that information, what they do with it, and the often-unforeseen consequences for our individual autonomy and societal norms. The journey of your data from your living room to the cloud and beyond is a tale of shifting ownership, opaque agreements, and a relentless pursuit of profit, frequently leaving the individual user with little control or even awareness of their digital footprint's destiny.
The Unseen Hands Who Profits From Your Private Digital Life?
When you purchase a smart device, whether it's a voice assistant, a smart TV, or a connected appliance, you're not just buying hardware; you're entering into a complex relationship with a multitude of entities. At the forefront are the device manufacturers themselves – companies like Amazon, Google, Apple, Samsung, and countless others. They collect a primary stream of data, often justified as necessary for device functionality, performance improvement, and personalized user experiences. However, their business models frequently extend beyond hardware sales; many are deeply invested in advertising and data analytics, meaning your data is a valuable asset that directly fuels their core operations. They want to understand your preferences, habits, and needs to better target ads, develop new products, and keep you locked into their ecosystems. This initial collection is often governed by lengthy, convoluted "Terms of Service" and "Privacy Policies" that few users ever fully read or comprehend, effectively granting broad consent to data collection and sharing.
But the data journey doesn't stop with the manufacturer. A vast network of third-party entities eagerly awaits their share. These include app developers whose software runs on your devices, cloud service providers who host the data, and, most significantly, data brokers. Data brokers are companies whose sole business model revolves around collecting, aggregating, and selling personal information. They meticulously piece together fragmented data points from various sources – your smart devices, online activity, public records, loyalty programs, and even offline purchases – to construct incredibly detailed profiles of individuals. These profiles can include everything from your estimated income and political leanings to your health conditions, purchasing habits, and family composition. They then sell these profiles to advertisers, marketing firms, financial institutions, political campaigns, and even governments, all without your direct knowledge or consent. This is a largely unregulated industry, operating in the shadows, making it incredibly difficult for individuals to understand or control the spread of their personal data.
The Fine Print and the Illusion of Consent
The concept of "consent" in the age of smart devices is, for many, an illusion. We are presented with lengthy terms of service and privacy policies, often written in legal jargon, that require us to click "agree" before we can even use our devices. These documents frequently contain broad clauses that permit companies to collect vast amounts of data, share it with third parties, and use it for purposes that extend far beyond the device's immediate functionality. The sheer burden of reading and understanding these documents for every app and device we use is prohibitive, leading to a phenomenon known as "privacy fatigue," where users simply click "agree" out of necessity, effectively surrendering their data rights without true informed consent.
"The problem with privacy policies isn't that they're hard to understand; it's that they're designed to be unreadable, to ensure that no one truly comprehends the extent of the data being taken." — Edward Snowden, Whistleblower.
Furthermore, even when privacy settings are available, they are often buried deep within menus, difficult to navigate, and sometimes reset with software updates. The "opt-out" mechanisms, where they exist, are rarely straightforward, often requiring users to jump through multiple hoops, contact various companies, or navigate complex online portals. This deliberate friction discourages users from exercising their privacy rights, ensuring a continuous flow of data. For example, many smart TVs have "ACR" (Automatic Content Recognition) features that track what you watch, even from external inputs like cable boxes or gaming consoles. While these features can often be disabled, the process is usually not intuitive, and the default setting is almost always "on," ensuring maximum data collection from the outset. This systemic design choice prioritizes data collection over user privacy, putting the onus on the individual to meticulously safeguard their digital footprint against a vast, interconnected industry.
The aggregation of this data by numerous entities creates compounding vulnerabilities. Each company that holds your data is a potential point of failure. Data breaches, unfortunately, are a common occurrence in our digital landscape. When a data broker or a third-party app developer suffers a breach, it's not just a single piece of your information that's exposed; it's often a comprehensive profile, meticulously built from years of collected data. This aggregated data is far more valuable to malicious actors, as it allows for highly sophisticated identity theft, targeted phishing attacks, and even blackmail. The ripple effect of a single breach can be devastating, as your information, once compromised, can circulate indefinitely on the dark web, affecting your financial security, personal safety, and long-term peace of mind. The invisible hands that profit from your digital life are also, inadvertently, the custodians of your digital vulnerability, and their security practices are often far from perfect.