Imagine a world where your most intimate conversations, your secret desires, your health concerns, and even your precise location are not just known, but meticulously cataloged, analyzed, and traded. Now, open your eyes. This isn't some dystopian novel playing out in a distant future; it's the unsettling reality many of us inhabit right now, often without a second thought, all thanks to the powerful little device we carry in our pockets: our smartphone. For over a decade, I’ve been immersed in the intricate world of cybersecurity and online privacy, witnessing firsthand the relentless erosion of personal space in the digital age. What began as a convenience has stealthily evolved into a sophisticated surveillance tool, a digital tether that broadcasts our lives to an unseen audience.
The ubiquity of smartphones has transformed every facet of our existence, from how we communicate and work to how we shop and navigate the world. These devices, undeniably brilliant feats of engineering, have become extensions of ourselves, holding a vast reservoir of our personal narratives. Yet, this profound integration comes at a steep price, one often paid in the currency of our privacy. We've been lulled into a sense of digital comfort, trading convenience for an invisible monitoring system that operates 24/7, silently collecting data points that paint an astonishingly detailed portrait of who we are. It’s a trade-off that, upon closer inspection, feels less like a fair exchange and more like a slow, insidious surrender.
The Unseen Eye and the Digital Chains We Wear
The idea that a device we own and pay for could be actively working against our privacy feels almost conspiratorial, yet the evidence is overwhelming and often openly declared, albeit buried in pages of legalese. Every tap, every swipe, every spoken word near your device, every location you visit, and every website you browse contributes to an ever-growing dossier on your life. This isn't just about targeted ads, though that's certainly a significant part of the equation; it's about predictive analytics, behavioral manipulation, and the commodification of your very identity. It’s about creating a digital twin of you, one that can be influenced, understood, and ultimately, controlled.
Think about it: your phone knows when you wake up, where you go for coffee, your commute route, the music you listen to, the news you read, the people you call, the photos you take, and even the nuances of your voice. This isn’t accidental; it’s by design. The entire ecosystem of apps, operating systems, and network services is built upon the premise of data collection. Companies argue this data is essential for improving services, personalizing experiences, and ensuring the smooth functioning of their platforms. While there might be a sliver of truth to that, the sheer volume and granularity of the information harvested far exceed what’s necessary for basic functionality, venturing deep into the realm of pervasive surveillance.
The stakes are incredibly high. The erosion of privacy isn't merely an abstract concept; it has tangible, real-world consequences. It can impact your credit score, your insurance premiums, your employment opportunities, and even your personal relationships. Data breaches expose this sensitive information to malicious actors, leading to identity theft, financial fraud, and reputational damage. Furthermore, the aggregation of data by powerful corporations and governments raises serious questions about autonomy and freedom in a surveillance society. We are, in essence, building the infrastructure for a future where every move is tracked, every preference is known, and every deviation from the norm can be flagged.
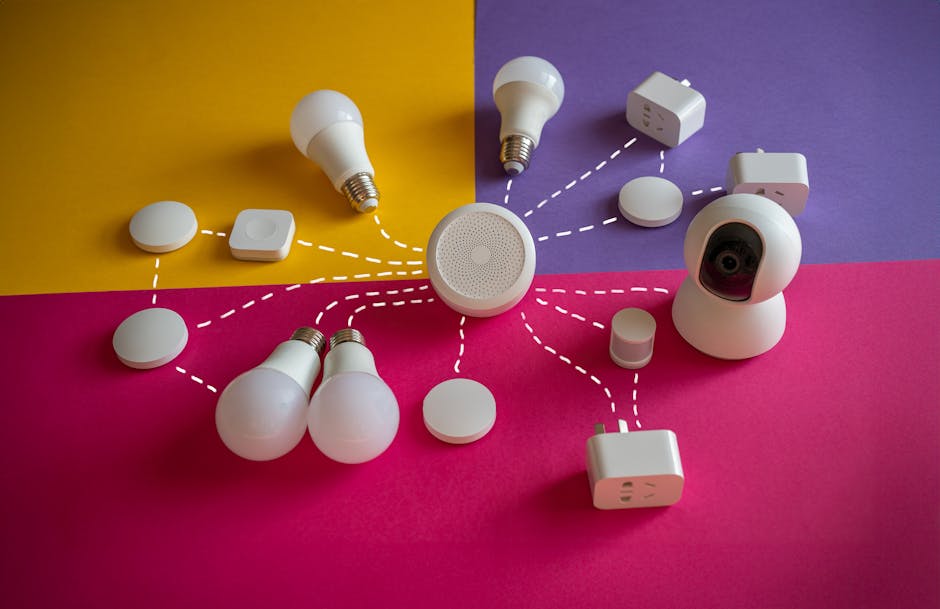
The Silent Symphony of Sensors and Software
Your smartphone is a marvel of miniaturized technology, packed with an array of sensors that are constantly active, silently gathering data about your environment and your interactions. The GPS chip pinpoints your location with startling accuracy, often within a few meters. Accelerometers and gyroscopes track your movement, differentiating between walking, running, driving, or even just holding the phone still. Microphones are always listening, not necessarily recording your every word directly for human review, but certainly processing ambient sounds for voice commands, "hot words," or even environmental data. Cameras capture not just images and videos, but can also be used for facial recognition, object detection, and even scanning QR codes that link to further data collection points.
Beyond the hardware, the software layer is where the real data magic happens. The operating system itself, whether Android or iOS, collects extensive telemetry data about how you use your device, app performance, crash reports, and system diagnostics. This data, often anonymized in theory, can still contribute to a broader profile. Then there are the countless apps we download, each demanding a litany of permissions: access to contacts, photos, microphone, camera, location, storage, and network activity. While some permissions are genuinely necessary for an app's core function (a mapping app needs location, a camera app needs camera access), many apps request far more access than they reasonably require, often justified by vague terms like "improving user experience" or "personalizing content." It's a digital land grab, where every piece of data is a valuable commodity.
"Privacy is not something that I'm merely entitled to, it's an absolute prerequisite." - Edward Snowden
The intricate web of data collection is further complicated by third-party trackers and advertising networks embedded within apps and websites. These aren't just the banner ads you see; they are invisible pixels, cookies, and scripts that follow you across the internet, building a comprehensive profile of your browsing habits, interests, and demographics. This information is then used to serve you highly targeted advertisements, a practice that can feel eerily prescient, almost as if your phone is reading your mind. But it's not mind-reading; it's just incredibly sophisticated data analysis, predicting your next move based on a mountain of past data points. The sheer scale and complexity of this surveillance infrastructure are difficult for the average user to grasp, making it even harder to protect oneself.