Security Questions: A Treacherous Path to Account Recovery
The third pervasive myth, one that often acts as the Achilles' heel for even the most robust password strategies, centers around the perceived security of those familiar "security questions." You know the drill: "What was your mother's maiden name?", "What is the name of your first pet?", "What street did you grow up on?". These questions are presented as a convenient, failsafe method for account recovery, a benevolent guardian angel ready to swoop in when you forget your complex password. However, this seemingly benign feature is, in reality, one of the most significant vulnerabilities in our digital lives. The information required to answer these questions is often either publicly available with a bit of digging, easily guessable by someone who knows you even slightly, or, in many cases, so common that automated attacks can quickly run through a list of probable answers. This makes security questions less of a protective barrier and more of a welcome mat for social engineers and determined hackers. It's a system built on assumptions of privacy that simply don't hold up in the age of pervasive online information and sophisticated social engineering tactics.
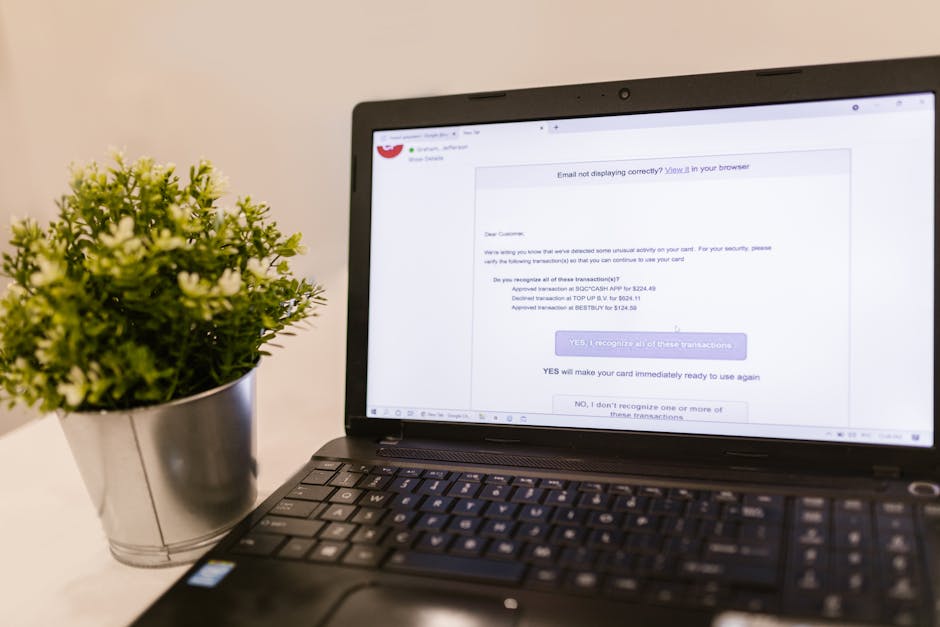
Consider the nature of these questions. "What is your mother's maiden name?" A quick search on genealogy sites, social media profiles, or even old newspaper archives can often reveal this information. "What was the name of your first pet?" If you've ever posted a nostalgic photo on Facebook or Instagram with a caption reminiscing about 'Fluffy' or 'Buddy', you've just handed over the answer. "What city were you born in?" This is often part of public records or easily found on professional networking sites. The fundamental flaw is that these questions rely on "secrets" that are either not secret at all or can be easily inferred by someone who knows you. Attackers don't need to be master hackers to exploit this; they just need to be good at open-source intelligence gathering (OSINT) and social engineering. A quick browse through your social media, a few minutes on Google, and suddenly, your "secret" answers are laid bare. This makes a mockery of the strong password you so painstakingly created, as the attacker can simply bypass it by correctly answering these predictable questions, effectively resetting your password and seizing control of your account.
The danger is compounded by the fact that many services offer a limited number of security questions, often with a predefined set of choices. This means that if an attacker knows you grew up in a certain region, they can then target a list of common street names from that area. If they know you went to a particular high school, they can try common mascots or school names. This isn't brute-forcing a random string of characters; it's brute-forcing a much smaller, more predictable set of answers. Furthermore, some services allow multiple attempts at answering security questions, giving attackers ample opportunity to try common answers or variations. The system is designed for convenience, not robust security. While the intent is to provide an easy recovery mechanism for legitimate users, it inadvertently creates a wide-open back door for anyone with a modicum of research skills or a lucky guess. We’ve been conditioned to view these questions as a safety net, but in reality, they often serve as a convenient bypass for determined adversaries, effectively rendering our primary password defenses moot.
When Your Life Story Becomes a Hacker's Key
The real insidious nature of security questions becomes apparent when we consider the prevalence of personal information available online. We live in an era of unprecedented data sharing. Every social media post, every online purchase, every public profile contributes to a vast digital footprint that can be meticulously harvested by malicious actors. Data brokers collect and sell personal information, and even seemingly innocuous details can be pieced together to form a comprehensive profile of an individual. For example, a birth announcement in a local newspaper from decades ago, now digitized and searchable, might reveal a mother's maiden name. A public record of a home purchase could reveal a childhood street. A simple Google search for an old high school reunion photo could expose a pet's name mentioned in a comment. Attackers leverage these publicly available data points to construct highly accurate guesses for security questions. This isn't about hacking; it's about intelligence gathering and pattern recognition, turning your life story into a hacker's key, all without ever touching your primary password.
A prime example of the devastating impact of compromised security questions is the infamous iCloud celebrity photo leak of 2014, often referred to as "The Fappening." While not solely attributed to security questions, social engineering tactics, which heavily rely on exploiting publicly available information to bypass authentication, played a significant role. Attackers targeted specific celebrities, gathering personal details that could be used to answer security questions or convince customer support representatives to reset passwords. This demonstrated that even high-profile individuals, presumably with robust primary passwords, were vulnerable to attacks that exploited the weakest link in the authentication chain – often, ironically, the "security" features designed to help them. It highlighted that if the information to answer a security question is guessable or discoverable, then the question itself is useless as a security measure. The lesson here is profound: a security mechanism is only as strong as its weakest link, and for many, that link is a set of poorly chosen, easily answerable security questions.
"Security questions are often a social engineer's dream. They turn publicly available information into a backdoor for your most private accounts." – Kevin Mitnick, notorious hacker turned security consultant.
So, what's the alternative? If security questions are so flawed, how should we recover our accounts? The consensus among cybersecurity experts is moving towards more robust, multi-factor authentication (MFA) methods for account recovery. This includes using a secondary email address that is itself secured with strong MFA, or, even better, using an authenticator app (like Google Authenticator or Authy) to generate one-time codes. Some services also offer recovery codes that you can print and store securely offline. When choosing security questions, if you absolutely must, treat them like a password. Don't use real answers. Instead, create entirely fabricated answers that only you would know, and ideally, record them in a secure password manager. For example, if the question is "What was your mother's maiden name?", your answer might be "PurpleElephantSpaceship." It's nonsensical, not publicly discoverable, and memorable only to you (if recorded). The key is to transform these traditionally weak points into strong, unique, and truly secret pieces of information that cannot be gleaned from your public life. This proactive approach is essential for plugging one of the most common and dangerous holes in our personal cybersecurity posture, shifting from relying on flawed "secrets" to actively creating unguessable ones.