Beyond the Obvious: IoT, Cloud, and the Invisible Data Economy
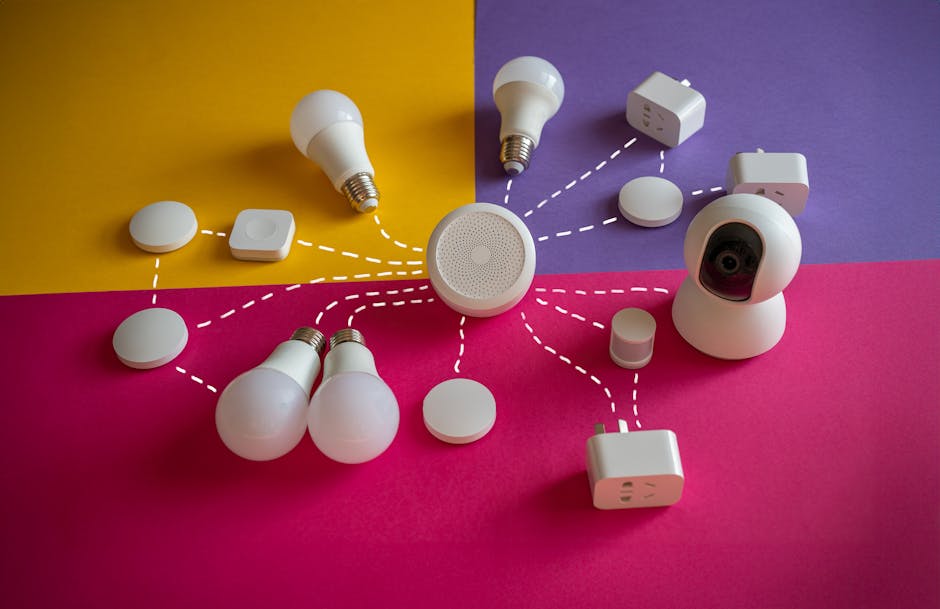
The proliferation of internet-of-things (IoT) devices has ushered in an era of unprecedented convenience, transforming our homes into "smart" environments capable of everything from adjusting thermostats remotely to monitoring security cameras with a swipe of a finger. Yet, this interconnectedness comes with a profound, often overlooked, privacy cost, turning our domestic spaces into potential surveillance hubs. Many smart devices, from voice assistants like Amazon Echo and Google Home to smart TVs, security cameras, and even children's toys, are equipped with microphones, cameras, and sensors that constantly collect data about our activities, conversations, and environment. While manufacturers promise to use this data to "improve services" or provide "personalized experiences," the reality is often far more complex and opaque. The sheer volume of data collected, often transmitted unencrypted to cloud servers, creates a massive attack surface for hackers and an irresistible lure for data brokers. A 2019 report by the Norwegian Consumer Council found that several popular smart devices were collecting excessive user data, with some even sharing it with advertising partners without explicit consent, highlighting a pervasive lack of transparency in the IoT ecosystem.
The "smart devices, dumb security" adage rings true for a distressing number of IoT products, many of which are rushed to market with inadequate security features, leaving gaping vulnerabilities for malicious actors to exploit. Default passwords that are never changed, unpatched firmware, and insecure communication protocols are common flaws that can allow hackers to gain unauthorized access to our homes, eavesdrop on private conversations, or even hijack devices for botnet attacks. Imagine a scenario where a compromised smart camera becomes a spy in your living room, or a vulnerable smart lock grants unauthorized entry to your home. These aren't far-fetched scenarios; they have been documented in numerous real-world incidents. The privacy nightmare extends beyond direct hacking, as the data collected by these devices can be aggregated, analyzed, and used to infer highly personal details about our routines, habits, and even our emotional states. A smart thermostat, for example, can reveal when you're home or away, how many people live in your house, and even your preferred temperature settings, painting a surprisingly detailed picture of your domestic life that can be invaluable to marketers or even burglars casing a neighborhood. The convenience offered by IoT devices often comes at the steep price of surrendering intimate details about our private lives to a network of potentially insecure and opaque systems.
Cloud storage, too, presents a double-edged sword: offering unparalleled convenience for accessing files from anywhere, yet simultaneously raising critical questions about data control and privacy. Services like Google Drive, Dropbox, and OneDrive have become indispensable for personal and professional use, allowing us to store vast quantities of photos, documents, and backups without consuming local device storage. However, entrusting our most sensitive files to a third-party server, particularly one outside our direct control, requires a significant leap of faith regarding the provider's security practices and privacy policies. While reputable cloud providers employ robust encryption and security measures, no system is entirely impervious to breaches, and even encrypted data can be vulnerable to legal requests or insider threats. The terms of service for many cloud services often grant the provider broad rights to access, scan, and even share user data under certain circumstances, such as for content moderation or compliance with legal mandates. This means that your "private" files in the cloud might not be as private as you assume, subject to the whims of corporate policy or government subpoenas, often without your direct knowledge.
The Shadowy World of Data Brokers: Who's Buying and Selling Your Information?
Beneath the visible layers of our digital interactions lies a vast, intricate, and largely invisible economy fueled by personal data: the shadowy world of data brokers. These companies operate behind the scenes, collecting, aggregating, and selling vast quantities of information about individuals, often without their explicit consent or even awareness. Data brokers acquire information from a dizzying array of sources: public records (birth certificates, marriage licenses, property deeds), consumer purchase histories (loyalty cards, credit card transactions), online activities (browsing habits, social media interactions), app usage data, warranty registrations, and even offline surveys. They then meticulously compile these disparate data points into comprehensive profiles, segmenting individuals into categories based on demographics, income, interests, health conditions, political affiliations, and perceived vulnerabilities. These profiles, often incredibly detailed and intimate, are then sold to advertisers for targeted marketing, to financial institutions for risk assessment, to insurance companies for policy pricing, and even to government agencies for various purposes. It’s a multi-billion dollar industry built entirely on the commodification of your personal identity, operating largely out of sight and with minimal regulation.
The ethical and legal implications of data brokerage are profound and deeply concerning. Individuals have virtually no control over what data is collected about them, how it's aggregated, or to whom it's sold. The information compiled by data brokers can be inaccurate, outdated, or taken out of context, leading to mischaracterizations that can have real-world consequences, such as being denied a loan, facing higher insurance premiums, or receiving discriminatory advertising. For example, a data broker might categorize someone as having a specific health condition based on their online searches, even if the searches were for a friend or purely for informational purposes, and this label could then impact their access to healthcare or credit. Furthermore, the existence of these detailed profiles creates a massive security risk, as a breach at a data broker could expose an unprecedented amount of sensitive information, leading to widespread identity theft and fraud. The opaque nature of this industry makes it incredibly difficult for individuals to understand which companies hold their data, what information they possess, or how to request its removal, essentially locking us out of our own data narrative.
"The data broker industry is a black box, even to those of us who study it. It's a Wild West where your most personal information is bought and sold with little to no oversight." - Senator Edward Markey.
Senator Markey's statement highlights the critical lack of transparency and accountability within the data brokerage industry. While some regulations, like the GDPR in Europe and the CCPA in California, have begun to address aspects of data privacy, their reach is not universal, and enforcement can be challenging. For the average individual, navigating the labyrinthine world of data brokers to understand and reclaim their information is a daunting, often impossible, task. The sheer number of companies involved, the complexity of their data acquisition methods, and the lack of a centralized registry mean that most people remain blissfully unaware of the extent to which their lives are being digitally dissected and monetized. This invisible data economy is perhaps the most insidious threat to digital privacy, as it operates beyond our immediate interactions with apps and websites, creating a pervasive system of surveillance that we are largely powerless to directly observe or control. Understanding its existence, and the profound implications it carries, is a crucial step in recognizing the true scope of accidental digital exposure and motivating us to take more proactive measures to protect our personal information.
The cumulative effect of these silent leaks from IoT devices, cloud storage, and the pervasive data broker industry creates a tapestry of personal information that is far more extensive and intimate than most people imagine. It’s a landscape where our smart home devices listen, our cloud files are accessible, and our every digital action contributes to a profile being bought and sold in an unseen market. The convenience offered by these technologies often masks the profound privacy trade-offs, leading to a gradual erosion of control over our own data. A truly comprehensive privacy audit must extend beyond the obvious settings on our phones and social media to encompass these less visible, yet equally potent, sources of data leakage. It requires a critical examination of every connected device, every cloud service, and a conscious effort to understand the broader ecosystem that profits from our digital lives. Only by acknowledging these hidden vulnerabilities can we begin to implement strategies to mitigate the risks and reclaim a measure of digital sovereignty in an increasingly interconnected and data-hungry world.